Andy Greenberg over at Wired has an interesting piece of news coming out of last week’s Derbycon hacker conference in Louisville, Kentucky. According to Greenberg and Wired, researchers Adam Caudill and Brandon Wilson showed off their own version of Karsten Nohl and Jakob Lell’s BadUSB malware, and that they’d released the code on Github.
Their presentation raises the stakes for USB manufacturers to fix the BadUSB problem or leave hundreds of millions of users vulnerable, Greenberg writes.
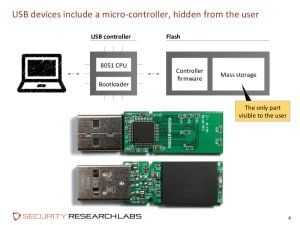
At a presentation at the Black Hat Briefings in August, Nohl and Lell, both of Security Research Labs (SRLabs), showed how the controller chips inside common USB devices can be reprogrammed, allowing USB peripherals to impersonate other kinds of devices. Among other things, Nohl demonstrated how a BadUSB infected device could emulate a USB keyboard, issuing commands to a connected machine using the permissions of the logged-in user. Alternatively, an infected USB could spoof a network card and change the computer’s DNS setting to redirect traffic, Nohl warned.
Speaking at Derbycon, Caudill said that making the malware public – something Nohl and SR Labs did not do – was a way to force the hand of manufacturers.
“If you’re going to prove that there’s a flaw, you need to release the material so people can defend against it,” Greenberg quotes him saying.
Read more via The Unpatchable Malware That Infects USBs Is Now on the Loose | WIRED.


“Nohl demonstrated how a BadUSB infected device could emulate a USB
keyboard, issuing commands to a connected machine using the permissions
of the logged-in user”
It amazes me how even my personal machine can be turned against me! Technology is evolving at such a rapid pace that security issues are popping up left and right—how many years have we been using USB devices? And now they are a danger? It just goes to show nothing is 100% secure.