The integrity of data stored on- and transmitted between Internet-connected embedded devices is one of the biggest technical hurdles standing in the way of widespread adoption of Internet of Things technology.
For one thing: embedded devices like wearable technology and “smart” infrastructure are often deployed on simple, inexpensive and resource constrained hardware. Unlike laptops or even smart phones, these are purpose-built devices that, by design, run for long periods in remote deployments, with extremely constrained features and low power consumption that is the result of limited processing power and memory.
[Read Security Ledger’s coverage of connected vehicles.]
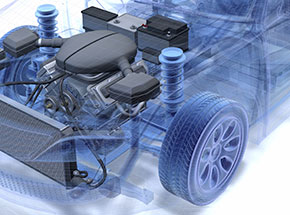
Now Intel is promoting a platform that it says can bridge the gap and provide robust security features even for resource-constrained Internet of Things devices like wearables and connected vehicles.
Back in April, the Intel Labs unveiled the results of joint research with Technische Universität Darmstadt in Germany. The researchers have developed a platform, dubbed TrustLite that they claim comprises a “generic security architecture” suited for low-cost embedded systems.
According to Intel, TrustLite will allow embedded device manufacturers to add features like remote device management, authentication, secure OTA (over the air) updates and remote attestation to their embedded devices, regardless of OS and application.
[Read more Security Ledger coverage of embedded device security.]
The heart of the new platform is something Intel calls an Execution Aware Memory Protection Unit (EA-MPU) – a software based module that “allows a flexible allocation and combination of memory and peripheral I/O regions without burdening CPU.”
Unlike many modern secure execution environments, Intel’s TrustLite doesn’t use virtualization, trusted execution or a secure firmware runtime. There is no assumption of a secure co-processor to provide a root of trust, meaning that TrustLite could be implemented on low-cost hardware.
The details of TrustLite are subtle and worth reading for yourself. Just as interesting are the many possible applications of the technology.
In the video below, Intel describes how TrustLite can be used to secure electronic control units (or ECUs) embedded in modern, connected vehicles. The video talks about the concept of “Trustlets” – basically discrete instantiations of a security mechanism on an embedded device running the TrustLite platform.
In essence, TrustLite enables small, ultra efficient security applications to run within the ECUs without burdening processor or memory resources in ways that affect their operation.
Check out the video below! And read Intel’s report on TrustLite here.

Pingback: Two glimmers of hope for enterprise security | LamboArchie Blog