Are smartphones made in China trying to spy on us? Top U.S. security officials and the Department of Defense (DoD) think it’s possible, prompting a ban on the sale of Chinese smartphones military base exchanges worldwide.
Tag: Mobile Threats
No Teeth in UK Internet of Things Security Report
The UK government released a draft report calling for a “fundamental shift” in the approach to securing Internet of Things devices. One prominent UK security researcher is unimpressed, however, calling the effort toothless.
Smartphone Users Tracked Even with GPS, WiFi Turned Off
A team of researchers from Princeton has demonstrated that they can track the location of smartphone users even when location services like GPS and WiFi are turned off.
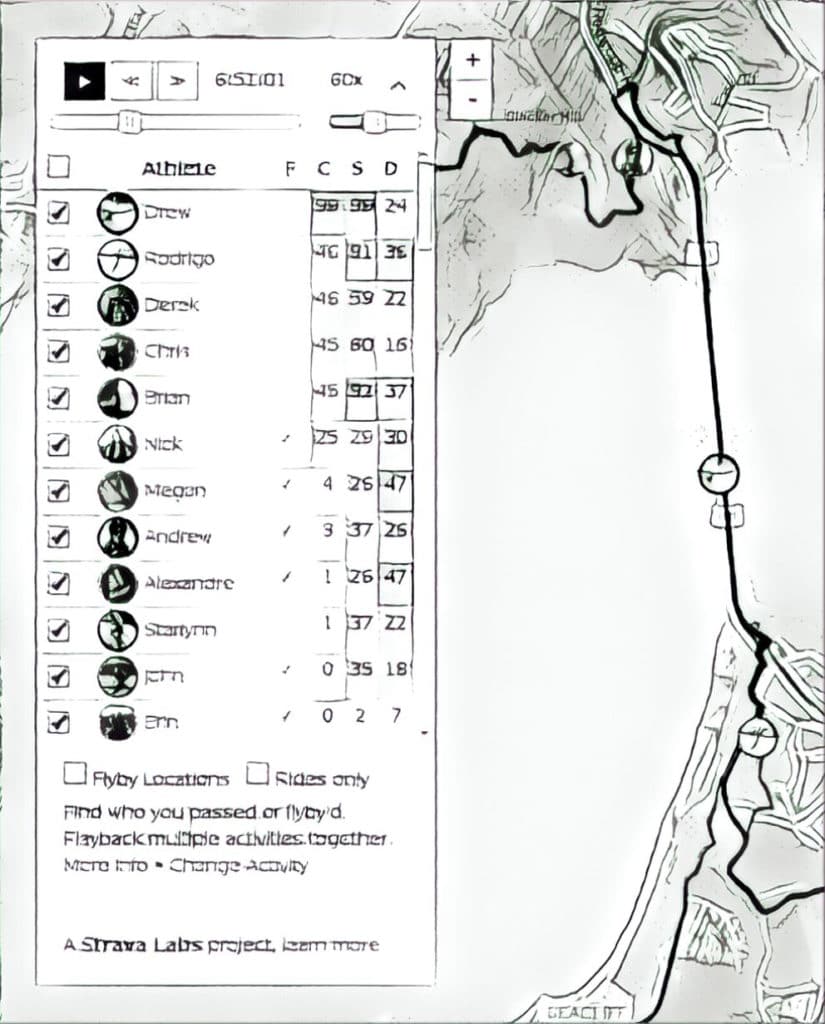
Privacy Meltdown: Strava tricked into Revealing Soldiers’ Names
Days after Strava fitness heatmaps were shown to reveal the location of military bases, a Norwegian journalist fooled Strava into revealing the names of some of soldiers and other personnel on those bases.
Episode 79: Hackable Nukes and Dissecting Naughty Toys
In this week’s Security Ledger Podcast episode, the UK -based policy think tank Chatham House warned last week that aging nuclear weapons systems in the U.S., the U.K. and other nations are vulnerable to cyber attacks that could be used to start a global conflagration. We talk with Eddie Habbibi of PAS Global about what can be done to secure hackable nukes. Also: with CES raging in Las Vegas last week, we go deep with security researcher Jay Harris on flaws in connected toys being sold to children.