Recognizing the persistent need for security to protect connected devices, industry leaders are collaborating through two separate efforts on Internet of Things (IoT) standards and guidelines to help combat the emerging IoT threat landscape.
Tag: Mobile Threats
Evasive MyloBot botnet can take over enterprise devices to steal data, spread ransomware
A new, extremely evasive botnet has been discovered that takes unique leverage of command and control servers and can completely take over an enterprise device to execute any type of code it wishes, from ransomware to trojans to data extraction, according to researchers at endpoint and mobile security firm Deep Instinct.
RSA Labs: cloud, microservices, mobility shift terrain for security providers
In this exclusive interview from April, the head of RSA Labs* says that keeping up with bad guys is only half the job. Security firms also need to work hard to stay relevant as trends like cloud adoption, containerization, microservices and mobility shift the ground under information security providers.
Container ships easy to hack, track, send off course and even sink, security experts say
Modern container ships already face a number of serious perils at sea. Now new research from Pen Test Partners shows just how vulnerable these ships are to new dangers from hacking–including being steered off course and sunk–thanks to their use of always-on satellite communications and general lax security practices on board.
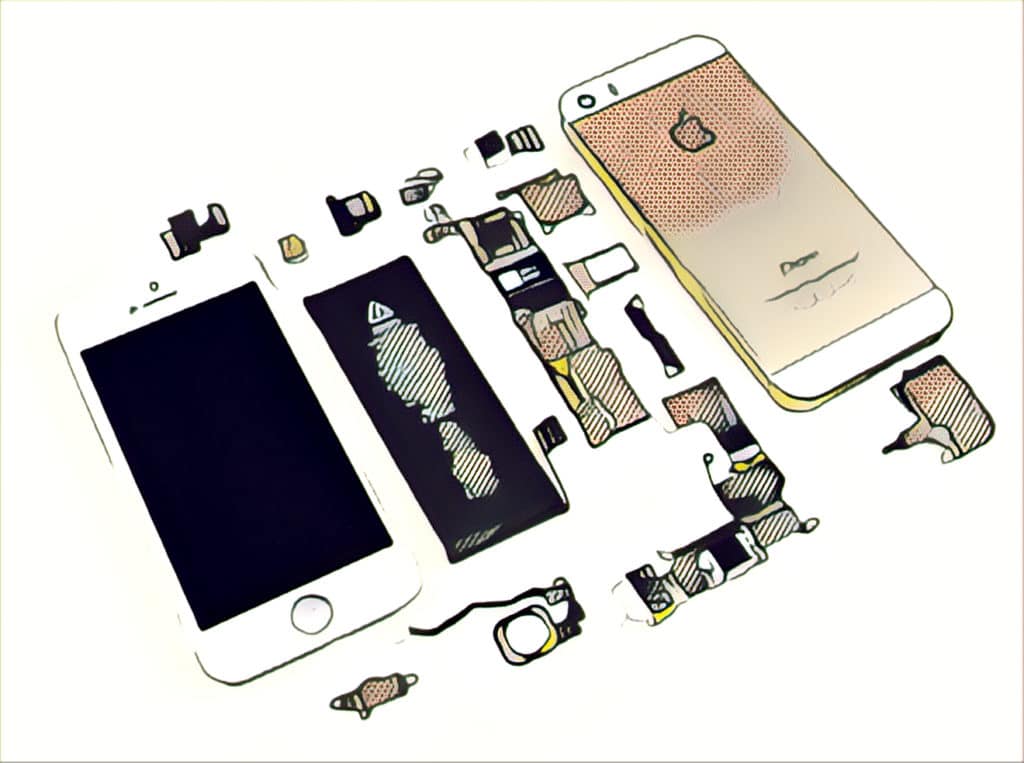
FBI exaggerated inability to access encrypted devices in promotion of ‘Going Dark’ problem
The FBI has mislead Congress and the public about the extent to which encrypted cellphones are hampering federal investigations by preventing authorities from accessing the devices–presumably to support the agency’s own agenda to gain backdoor access to them.