It’s H-Day + 2 – two full days since we learned that one of the pillars of online security, OpenSSL, has contained a gaping security hole for the past two years that rendered its protections illusory. As I wrote over on Veracode’s blog today: this one hurts. It exposes private encryption keys, allowing encrypted SSL sessions to be revealed. Trend Micro data suggests around 5% of one million Internet top-level domains are vulnerable. IOActive notes that Heartbleed also appears to leave data such as user sessions subject to hijacking, exposes encrypted search queries and leaves passwords used to access online services subject to snooping, provided the service hasn’t updated their OpenSSL instance to the latest version. In fact, its safe to bet that the ramifications of Heartbleed will continue to be felt for months – even years to come. In the meantime, there is a lot of interesting coverage and […]
IOActive
SOHOwned: 300K Home Routers Hacked
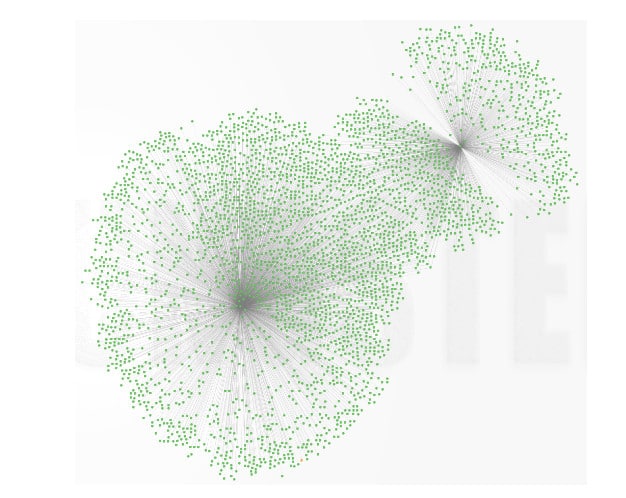
A string of reports in recent weeks has focused a spotlight on rising attacks against an often-overlooked piece of equipment that can be found in almost every home and business: the wireless router. Just this week, the security firm Team Cymru published a report (PDF) describing what it claims is a widespread compromise of small office and home office (SOHO) wireless routers that was linked to cyber criminal campaigns targeting online banking customers. Cymru claims to have identified over 300,000 SOHO devices (mostly in Asia and Europe) that were compromised. According to the report, the compromises first came to light in January, after Team Cymru analysts noticed a pattern of SOHO routers with overwritten DNS settings in central Europe. The affected devices are from a range of manufacturers, including well-known brands like D-Link, Micronet, Tenda and TP-Link. The devices were vulnerable to a number of attacks, including authentication bypass and cross-site […]
Update – Virtual Vandalism: Firm Warns Of Connected Home Security Holes
[This story was updated to include response from Belkin describing its response to the vulnerabilities identified by IOActive, including firmware updates. – PFR Feb 19, 2014] A researcher with the respected security firm IOActive says that he has found a number of serious security holes in home automation products from the firm Belkin that could allow remote attackers to use Belkin’s WeMo devices to virtually vandalize connected homes or as a stepping stone to other computers connected on a home network. In a statement released on Tuesday, IOActive researcher Mike Davis said that his research into Belkin’s WeMo technology found the “devices expose users to several potentially costly threats, from home fires with possible tragic consequences down to the simple waste of electricity.” IOActive provided information on Davis’s research to the US Computer Emergency Readiness Team (CERT), which issued an advisory on the WeMo issues on Tuesday. Belkin did not […]
Experts: Despite Warnings, Slow Progress Securing Industrial Systems
Despite increased media attention to the security of industrial control systems and critical infrastructure, progress in securing those devices has been slow, experts say. Despite progress in some areas, critical infrastructure – including energy and transportation networks- remains vulnerable to attacks leveled at known security holes for months or years because of a lack of vendor response or customers who lack the incentive or know-how to patch vulnerable systems. That according to some of the world’s top experts in cyber security and industrial systems, who are gathering this week at an industry conference in Miami. The S4 Conference, sponsored by the firm DigitalBond, is one of the premiere conferences for cyber security as it pertains to industrial control systems and often coincides with disclosures from industrial system vendors about serious security holes in their products. The security of industrial control systems has been a top concern of IT security experts and government […]
Siemens Patches Holes In Industrial Control Switch
A security researcher discovered two, serious security holes in a switch by Siemens that could allow an attacker to hijack industrial control system hardware that is heavily used by energy and transportation firms, among others. IOActive, a security consulting firm in Seattle, Washington, said on Thursday that Eireann Leverett, a senior security consultant, discovered two vulnerabilities in Siemens’ SCALANCE X-200 Switches. The vulnerabilities were in a web server component that provided administrators with access to features needed to configure the switches. If exploited, they would have allowed an attacker who had access to the same network as the SCALANCE switch to perform administrative actions on the devices, including updating the switch firmware and hijack active web sessions – all without needing to first log in to the device. SCALANCE is a family of Ethernet switches that connect to industrial control system (ICS) devices including programmable logic controllers (PLCs) and Human […]