A researcher is warning users of the Signal secure messaging application that photos and video files shared in Signal chats may be hanging around on their devices unencrypted, even after the messages in which the images were shared have been deleted, putting users at risk. Signal contests the claim and says the researcher is needlessly sowing fear and alarm.
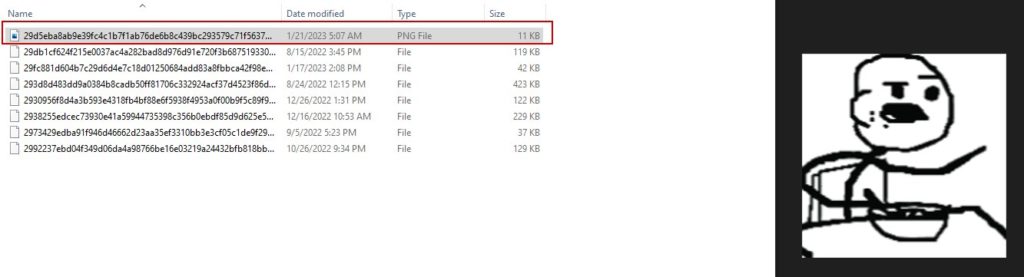
Researcher John Jackson (@johnjhacking) warned in a Twitter post on Saturday that the Signal secure messaging application doesn’t encrypt images shared in chat messages when they are stored locally, and that those images may linger on devices for weeks or months. That could put Signal users at risk, should their device be seized – for example: by police or government officials in authoritarian states, Jackson warned.
Signal is an encrypted instant messaging application that can be used across different platforms including Windows, Mac, iOs and Android. It is developed as open source software by The Signal Foundation and allows users to send one-to-one or group texts, share files, video and images or engage in group chats. The app users standard cellular telephone numbers as identifiers and secures all communications to other Signal users with end-to-end encryption. As of January 2022, Signal was estimated to have more than 40 million monthly users.
Months of images for the taking
According to Jackson, the Signal application stores “months worth of images from your conversations … unencrypted on disk.” While the cached images are at a reduced resolution, it still poses a security and privacy risk to Signal users, who may assume that the encrypted application clears out cached images, especially those associated with deleted messages.
To access the stored data, an adversary would need physical access to the device running the Signal service. That means Signal users, in general, are not at risk. However, Signal users who may be targeted by law enforcement or repressive regimes should be concerned.
Episode 233: Unpacking Log4Shell’s Un-coordinated Disclosure Chaos
“If you’re a reporter, activist, or someone that generally relies on Signal for encryption – be aware that reduced quality previews of the photos you send can be recovered via %AppData%,” Jackson tweeted.
The issue also applies to images shared with you by your Signal correspondents, Jackson said.
In a phone conversation, he said he stumbled on the problem late at night, after chatting with a contact via Signal and sending the contact a funny image in a chat message, which he subsequently deleted. When he checked the application’s cache to determine if the shared images was also deleted, he found that it wasn’t – and that cached images from prior chats still lingered on his device.
Bug, bad design or business as usual?
Those commenting on Jackson’s post debated whether it was appropriate to classify the behavior as a “vulnerability.” They observed that attackers would need access to the device and that it has long been known that Signal data can be accessed “at rest” on devices running the Signal application.
However, Jackson said that the issue closely resembles a flaw he discovered in Keybase, a secure messaging application similar to Signal. In that case, which Jackson disclosed in January, 2021, he found that Keybase also did not adequately clear the application cache and some residual files can be viewed, with no form of encryption on the files. As with Signal, Keybase allowed photos attached to messages to remain on disk even after clearing the containing chat. That resulted in the issuance of a CVE, CVE-2021-23827, describing the flaw.

According to MITRE, “cleartext storage of sensitive information” is a security problem with a unique identifier on its Common Weaknesses Enumerations (CWE) list, CWE-312, which describes situations in which “because the information is stored in cleartext (i.e., unencrypted), attackers could potentially read it. Even if the information is encoded in a way that is not human-readable, certain techniques could determine which encoding is being used, then decode the information.”
Israeli Group Exploited WhatsApp to Spy on Users
He said Signal’s app also shows evidence of CWE-459, “Incomplete Cleanup,” in which “the software does not properly “clean up” and remove temporary or supporting resources after they have been used.”
Jackson hypothesized that sophisticated adversaries who gained access to a Signal user’s device could tamper with and modify images and videos stored in the Signal cache, adding malicious code to them that might then be re-shared to other Signal users or groups.
Jackson registered two vulnerabilities with NIST’s National Vulnerability Database (NVD) related to his discoveries: CVE-2023-24068 and CVE-2023-24069. Those are “awaiting analysis” and Signal could contest Jackson’s filing.
Signal: nothing to see here
Signal’s President, Meredith Whittaker, said that Jackson was mistaken.
“What @johnjhacking posted is not a 0-day, not a Signal vulnerability, and not new,” Whittaker said in a statement via Direct Message. “(Jackson) is looking at the default–and widely-known–file storage location for Signal Desktop. Their alarming tweets recount the fact that Signal Desktop stores attachments that you receive on your device. This is not new. This is how those attachments can be viewed and shared within Signal. Signal makes no claims to provide at-rest encryption, and we encourage everyone to enable full-disk encryption at the OS level, which is available on most desktop operating systems and is the right tool for this job.“
Whittaker said that Signal is bound by the limitations of the environments in which its applications run. “Signal operates in a larger ecosystem, and runs on devices and platforms which we do not and cannot take full responsibility for. If someone is able to breach the security of your device, they will likely be able to use your device on the same terms you would – listening to your Spotify playlists, checking your browser history, and perhaps opening Signal Desktop and viewing the contents of messages and shared files.” The lesson for Signal users, she said, is ” is not that something is wrong with Signal, but that in addition to using Signal it is important for privacy- and security-conscious people “to take precautions to secure their devices, like not leaving your computer unlocked, and to follow best security practices generally.”
As for Jackson’s allegations that images remain after the messages they were transmitted in are removed, Whittaker also contested that.
“When you delete an entire conversation on Signal Desktop, all media in that conversation is deleted. Full stop. If someone in a Signal conversation sends a quoted reply to an image, a small thumbnail of that image is generated and used in the quoted reply. Just as with the original full-size image or attachment, the quoted-reply thumbnail will also be removed from the disk if the message containing that quoted reply is deleted. This is not a vulnerability.”
Reason for concern
Richard Forno, the Assistant Director of the Center for Cybersecurity at UMBC said that the dispute between Jackson and Signal may boil down to semantics about what is and is not a “vulnerability.” However, when it comes to Signal storing attachments unencrypted, he said that Jackson has a point.
”From a pure security perspective, it very well could be considered a vulnerability in certain situations and contexts, for example: if the device gets remotely exploited and any sensitive data exfiltrated.” Since remote exploitation is a very real concern, “Signal might consider encrypting that data at rest as well and allaying concerns,” Forno said.
Bad blood over Signal flaws
Jackson was a founding member of the now-defunct hacking crew known as Sakura Samurai. (Check out our interview with John in Episode 200 of Security Ledger podcast.) This isn’t his first run-in with Signal.
In 2021, he and a group of researchers tangled with the company’s development team over an alleged flaw with the application’s management of “safety numbers,” which Jackson and colleagues discovered. At the time, Jackson and others alleged that Signal denied the existence of the problem, while secretly patching the application’s code and updating documentation to reflect changed behavior. Signal, including founder Moxie Marlinspike, said that the behavior the researchers observed was by design and that no flaw existed.
Whittaker said Jackson’s latest warning are part of a “troubling pattern.”
“(Jackson) has been confused about Signal in the past,” she wrote, linking to Marlinspike’s 2021 Twitter exchange with the researcher. “Like now, their enthusiastic confusion led them to claim that vulnerabilities were present where none existed. We suggest they take a more measured approach in the future, and double check whether dramatic alarm is in fact warranted before posting on main.”
Messaging apps a target
Messaging applications like Signal and WhatsApp are a rich target for oppressive regimes around the world. In 2019, for example, reports surfaced that software developed by the Israeli firm NSO Group could exploit a flaw on the WhatsApp encrypted messaging application to install itself on a vulnerable iPhone or Android device – a risk to more than 1.5 billion WhatsApp users globally.
This wouldn’t be the first security flaw to affect the Signal application. In 2019, a researcher from Google’s Project Zero team reported a vulnerability to the firm in which a specially crafted Signal client can initiate an audio call to the targeted user and force their device to answer the call, including a video call.
Around 1,900 Signal users were also affected by a breach of the third party service Twilio in August 2022. Signal used Twilio for text verification services.

Pingback: Beware: Images, Video Shared on Signal Hang Around – Yet Another News Aggregator Channel