The NotPetya malware’s ability to cripple even sophisticated, global firms is a cautionary tale about the need for businesses to understand their risk and take a holistic view of security says Fadi Albatal, Chief Strategy Officer at Hitachi Systems Security.*
If you’re keen on information security and happen to enjoy horror stories, point your browser over to wired.com and check out writer Andy Greenberg’s exposé of the NotPetya malware and its impact on one company – international shipping giant A.P. Møller-Maersk.
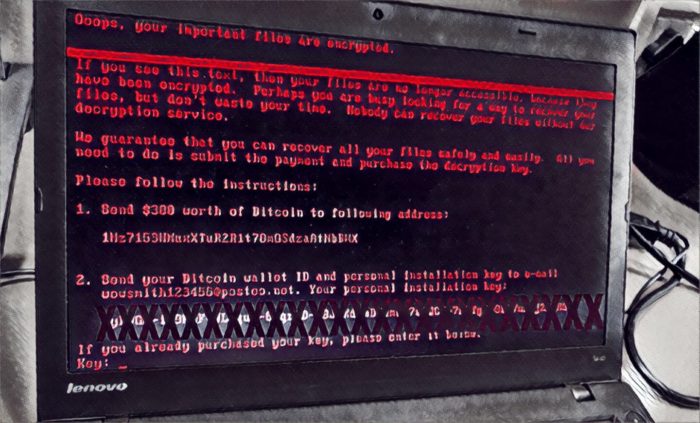
The story is not for the faint of heart. In it, you’ll read anecdotes about the first confusing hours following the outbreak on June 27, 2017. There are depictions of confused employees drifting – like moths – to the company’s technology help center carrying crippled laptops displaying ransom notes in red and black lettering.

Or you can read about IT administrator Henrik Jensen (not his real name) poking his head over the top of his cubicle to witness “a wave of screens turning black. Black, black, black. Black black black black black,” as NotPetya swept through the ranks of Maersk’s massive corporate network. IT staff and other employees were left to scramble from office to office, unplugging any IT equipment that hadn’t already been infected. By late afternoon, many of the company’s 80,000 employees were simply sent home: unable to do their jobs without the laptops, servers and routers that power modern organizations.
That’s chilling stuff. And we know that the cost to Maersk was also chilling. The company was forced to re-image 4,000 servers and 45,000 laptops and desktops to rid itself of NotPetya. Total costs to the company were $300 million, according to company statements.
Lesson 1: don’t panic!
In the face of such stories “from the trenches,” it is easy to panic: scrambling for security solutions like the Maersk employees scrambled to unplug vulnerable equipment. But that’s the opposite of what companies need to do. Rather, outbreaks like NotPetya underscore the need for us to take a cool headed and holistic approach to securing our IT environments: aligning security investments with business priorities and putting the most resources to protecting the most critical and vulnerable IT assets.

This is easier said than done. At Hitachi Systems Security, we are often asked by customers what security technologies and services are the best investments. Or we’re asked to justify investments by calculating the “return on investment” (or ROI) for a particular technology. But both of these are difficult questions to answer, at least in a blanket fashion. One simple response is “it depends.” Every business is different – even within the same industry. That means that security tools that might represent a tremendous ROI in one organization might be wasteful and ineffective in another.
[See also: Cisco Links Remote Access Tool Remcos to Cybercriminal Underground]
Security ROI is easy to understand…in hindsight
ROI is also something that is easier to calculate in hindsight than it is to predict. For example, NotPetya spread initially as a bogus software update for M.E. Doc, a tax and accounting software package published by a Ukrainian firm. Once in an environment, however, NotPetya spread via an exploit known as “EternalBlue” which triggered a known vulnerability in Microsoft Windows (MS17-010) that had been patched more than two months prior. It then used a custom version of a common Windows utility, PSEXEC and WMIC, to move laterally and infect other systems on the network.
The problem at Maersk and so many other organizations almost certainly wasn’t an absence of patch- or network management tools to remove Windows vulnerabilities or spot lateral movement. Rather, it was that the security posture of the company was to prevent disruptive or stealthy attacks like, say, Gh0st rather than destructive malware attacks like NotPetya. Too often we find that companies like Maersk are fighting “the last war” and fail to see new threats like NotPetya coming and to anticipate how destructive they will be.
[Also read: What the UK Knows: Five Things That Link NotPetya to Russia]
Yes, $300 million in damages in a single quarter makes it easy to justify pretty much any security spend – in hindsight. The trick is to be able to understand your security risks well enough to envision worst case scenarios in advance. Then the job of making much smaller, strategic security investments to mitigate those risks is manageable and affordable.
Don’t fight the last war
The best way to do that is by implementing a set of different security controls that are specific to your business context, threat exposure and risk appetite. You can choose from an array of different controls, such as firewalls, intrusion detection systems, privileged access control, 24/7 log monitoring or security awareness training. No matter what you choose, your security controls should be aligned to your overall security strategy, help strengthen your cybersecurity posture and manage your risks effectively. Remember that you’ll likely need to report on whether or not these controls are effective, so be sure you know how you’re going to measure your controls once they’re implemented.
You can also start by implementing a solid security management framework like the NIST Cyber Security Framework (CSF) or the ISO 27001 standard for creating an information security management framework. These frameworks also help organizations look beyond specific systems or technology platforms, taking a holistic view of security that encompasses people, resources, assets and processes that may affect business continuity.
Just to cite one example that bears directly on the NotPetya outbreak: the ISO 27001 standard asks organizations to consider their “role in the supply chain” as part of an assessment of their business environment. Such a requirement may have prompted the creation of a list of third party service providers or a larger (software) supply chain management program that might have been successful in limiting the damage from the malicious M.E. Doc update that began the NotPetya outbreak.
Rather than ‘fighting the last war’ or responding to the threat du jour, frameworks like NIST’s CSF help you create the policies, procedures and controls – both physical and technical – that will keep your data and IT assets secure.
(*) Hitachi Systems Security is a sponsor of The Security Ledger. For more information on how Security Ledger works with its sponsors and sponsored content on Security Ledger, check out our About Security Ledger page on sponsorships and sponsor relations.


FnGg
Pingback: Executive Insights on IT Pros Cybersecurity Challenges
Pingback: Report: Obvious Security Flaws Make ICS Networks Easy Targets | The Security Ledger