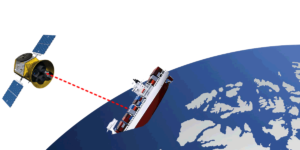
Modern container ships already face a number of serious perils at sea. Now new research from Pen Test Partners shows just how vulnerable these ships are to new dangers from hacking–including being steered off course and sunk–thanks to their use of always-on satellite communications and general lax security practices on board.
Pen Test Partners (PTP), a penetration testing and security services firm, demonstrated a number of methods for hacking into the satcom systems of ships, which can allow bad actors access to shipboard systems and wreak potential havoc for the vessels and the shipping industry.
PTP researchers applied expertise in IoT, automotive and SCADA hardware security to a Cobham (Thrane & Thrane) Fleet One satellite terminal and demonstrated various methods of intrusion this week at Infosecurity Europe, as well as published their findings online.
“Ship security is in its infancy–most of these types of issues were fixed years ago in mainstream IT systems,” PTP consultant Ken Munro wrote in a blog post outlining its finding. “The advent of always-on satellite connections has exposed shipping to hacking attacks. Vessel owners and operators need to address these issues quickly, or more shipping security incidents will occur.”
The latest research builds upon some poking around on satcom networks connected to ship terminals that Munro did last year that showed how vulnerable ship security is, likening them to industrial control networks, “but floating.”

[Also read: No Teeth in UK Internet of Things Security Report]
In its new research, the firm demonstrated and published online what it believes is “the first ever VULNERABLE ship tracker” by linking version details from a satcom terminal to live GPS position data, Munro wrote.
“Two public data sets have been linked, so we now have a clickable map where vulnerable ships are highlighted with their real time position,” he said. Researchers deliberately didn’t refresh the data in use so it can’t actually be used by hackers but do plan to update it at a later time.
Lack of basic security on ships
One reason it’s so easy to hijack the satellite communications of a ship and take admin rights on the on-board terminal is that many terminals are available on the public Internet and have default credentials “admin/1234” or “admin/12345,” which are obviously quite common and easy to guess, Munro said.
The PTP team also managed to hack a ship’s satcom terminal hardware, which had admin interfaces over telent and HTTP and, upon closer inspection, unsigned firmware, he said.
Moreover, the team also could edit the entire web application running on the terminal, something that also can be leveraged in attacks. Hackers with a bit of access also could elevate their privileges by installing an older, more vulnerable version of the firmware because there was no rollback protection for it, Munro said.
Once the satcom terminal was hacked, researchers found it’s often quite easy to get directly onto the ship’s own network, which is where some of the real harm can be done and the danger lies for those on board.
“We often find a lack of network segregation on the vessel,” Munro said. “Hack the satcom terminal and you’re on the vessel network.”
Once on the ship network, researchers demonstrated two methods for sending a ship the wrong way–one by hacking its ECDIS, which are the electronic chart systems ships use to navigate, and the other by exploiting the serial networks on board that control the Operation Technology (OT).
[See also: Researcher calls in-flight entertainment hacks a safety threat]
Most modern vessels are in “track control” mode most of the time, where they follow the ECDIS course, Munro said. So if someone manages to hack the ECDIS, crashing the ship is not such a remote possibility, especially in foggy conditions, he said.
“Younger crews get ‘screen fixated’ all too often, believing the electronic screens instead of looking out of the window,” Munro said.
‘Crazy security flaws’ present in systems
In the more than 20 different ECDIS units the PTP team tests, they found “all sorts of crazy security flaws,” including the running of ancient operating systems like Windows NT, he said.
A poorly protected configuration interface on one system even allowed the team to “jump” the boat from one side of Dover Harbor to another by spoofing the position of the GPS receiver on the ship–basically telling the ECDIS that the GPS receiver is in a different position on the ship, Munro said.
In the other scenario, researchers showed just how easy it is to exploit a ship’s OT system, which is used to control much of the critical control infrastructure on board, including the steering gear, engines and ballast pumps
These systems communicate using plain-text NMEA 0183 messages that aren’t authenticated, encrypted or validated in any way. “All we need to do is man in the middle and modify the data,” Munro said. In his post he outlined the modification of a GPS autopilot command that could change the rudder and steer the ship off course.
Munro acknowledged in his post that all of the vulnerabilities the team covered at InfoSec could be resolved by setting a strong admin password in a satcom terminal, “as per the manufacturers guidance.” However, the team did find more significant flaws that aren’t so easy to fix and will reveal them publicly later after privately disclosing their findings to Cobham, he added.

Pingback: Container ships easy to hack, track, send off course and even sink, security experts say - Secure Signal NYC
Pingback: CounterTack, Phishing Attacks, and Who Uses Flash? - Paul's Security Weekly #563 - Security Weekly
Pingback: CounterTack, Phishing Attacks, and Who Uses Flash? – Paul’s Security Weekly #563 – Cyber Sercuirty
Pingback: CounterTack, Phishing Attacks, and Who Uses Flash? – Paul’s Security Weekly #563 – f1tym1