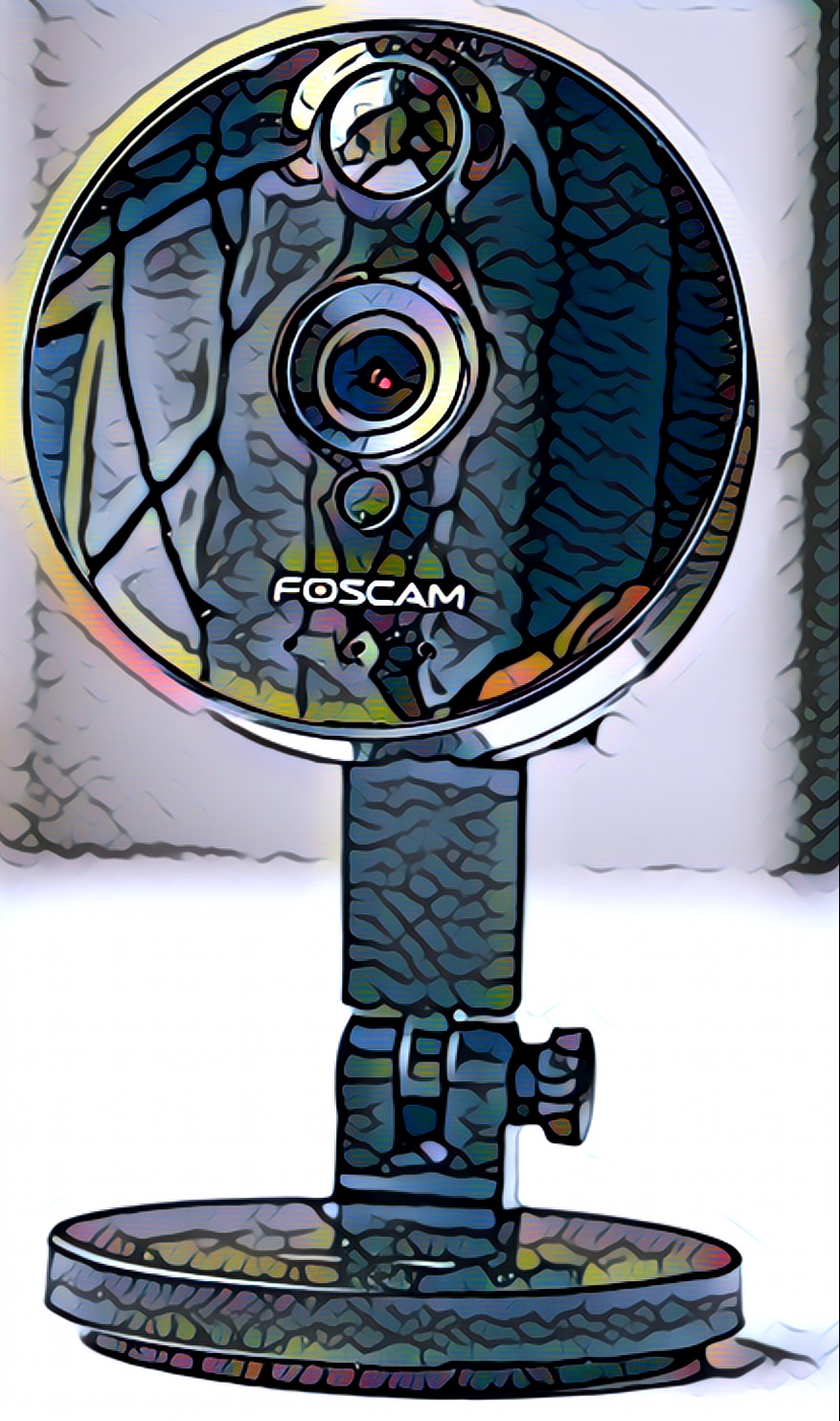
Cisco Systems is warning the public about a range of new vulnerabilities it has discovered in IP cameras from the firm Foscam, a popular maker of commercial and consumer surveillance cameras, the second trove of software security holes uncovered since June.
Cisco’s Talos group on Monday detailed eight vulnerabilities including remote code execution flaws that could allow remote attackers to place and run malicious code on Foscam indoor IP cameras.
According to Talos, Foscam’s C1 Series Indoor IP Cameras can be attacked using a variety of security holes. Among them: buffer overflow vulnerabilities, which were discovered in a Dynamic DNS client component of the cameras. Also: Foscam IP cameras were found to be vulnerable to code injection attacks and to allow unsigned firmware updates via a web-based administration interface – an easy route for hackers to place malicious code on the devices.
A second batch of flaws
This isn’t the first time Foscam cameras have been found wanting. In June, Talos warned of 20 other security flaws in firmware and applications that run on the C1 camera platform. Those included command injection flaws, undocumented FTP passwords that were “hard-coded” into the devices, allowing anyone with knowledge of the password value to gain access to an exposed Foscam camera.
Talos said the new vulnerabilities were discovered as part of a continuing security assessment of the Foscam devices and that the company has disclosed them to Foscam.
Cameras: Poster Children of Internet of Things Insecurity
IP enabled cameras have become the poster child for Internet of Things security woes. Problems with the devices range from hard-coded or easily guessed administrative credentials to vulnerable device firmware and application code.
Often, IP cameras are sourced from suppliers around the world, or white labeled, with different licensing the same hardware platform but selling it in different form factors and branding. The Mirai botnet leveraged security flaws in firmware from the Chinese firm Dahua that was shared across hundreds of different makes and models of IP cameras, digital video recorders (DVRs) and other devices. Further, researchers have warned about widespread security flaws in firmware that is used across thousands of different camera models (including those by Foscam).
Talos recommends Foscam customers update their firmware to resolve the security issues.