Podcast: Play in new window | Download (22.3MB) | Embed
Subscribe: Apple Podcasts | Spotify | Email | TuneIn | RSS
In-brief: on this week’s Security Ledger Podcast, we delve deeper into the question of maritime cyber security, speaking with noted researcher Ruben Santamarta of the firm IOActive about the work he’s done exposing vulnerabilities in the software that runs both commercial and navy vessels. Also: Alan Brill of Kroll joins us to talk about The Internet of Things Cybersecurity Improvement Act. And we talk to Maria Loughlin of the firm Veracode about a new survey that suggests undergraduate computer science majors aren’t receiving adequate instruction in cyber security.
On the morning of August 21st, the USS John S. McCain, a guided missile destroyer collided with an oil tanker, the Alnic, in the straight of Malacca, a busy and narrow shipping lane. The accident caused severe damage and flooding on the McCain and cost the lives of ten crew members, injuring five others. It was the second fatal accident in the last three months, following a fatal collision between the USS Fitzgerald and the ACX Crystal in June. There have been two other accidents involving ships from the US Navys 7th fleet in just the last six months.
The spate of collisions between commercial vessels and Navy warships in recent months is unprecedented in recent navy history. In fact, Before this year, the last collision between a U.S. Navy ship and a civilian vessel was more than a decade ago, in 2004 when the USS John F. Kennedy ran over a small sailing vessel in the Persian Gulf during training exercises.
The unusual coincidence of collisions has prompted speculation that something other than bad luck may be at play, and has focused attention on the threat of hacking and other kinds of electronic tampering to the US’s modern, highly technology dependent warships. As we noted earlier in the week, there is both the means and the motive for such attacks on US Navy vessels. So, could the McCain or the Fitzgerald have been hacked? And if so, how?
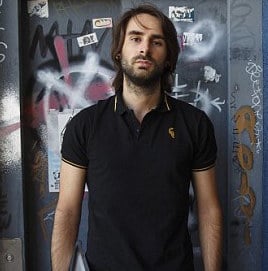
To answer those questions, we sat down for this week’s podcast with researcher Ruben Santamarta of the firm IOActive who is one of the world’s recognized experts in the security of maritime software. Ruben talks about the work he’s done exploring the security holes in both maritime systems and why hacking isn’t a likely cause for the incidents in the Pacific.
Also in this week’s podcast: the US Congress is taking a first swing at regulating the security of the fast-growing Internet of Things with the Internet of Things Cybersecurity Improvement Act, which mandates security features for connected devices. The bill applies only to software and hardware purchased by government agencies. But how big an impact might it have on private sector firms and consumers? We speak with Alan Brill, who is a senior managing director of Kroll cybersecurity. He joined us to talk about proposed law, which was introduced earlier this month.
And finally: we’ve heard over and over again about the shortage of skilled information security professionals in the workplace and the need to attract more men and women to the field. But what about the computer scientists and engineers who emerge every year from undergraduate and graduate programs without the necessary skills in software security they need to contribute to security-conscious development organizations? By one measure, undergraduate computer science majors may be exposed to between 3 and 9 hours of instruction in computer security in the course of a 4 year undergraduate degree.
A new survey by the firm Veracode found that 70% of information technology professionals feel their security education is not adequate for their current positions. In this week’s podcast we talk to Maria Loughlin, the VP of Engineering at Veracode about why that is, and how to fix it.
Check our full conversation in our latest Security Ledger podcast below or over at Soundcloud. You can also listen to it on iTunes. As always, if you like our intro music, give some love to the group JoeLess Shoe, who recorded “Baxton,” the song we use in just about every podcast.

