
In-brief: a serious and remotely exploitable flaw in software from the firm Schneider Electric poses serious security risks for industrial control environments, according to a report by the firm Indegy.
A serious and remotely exploitable flaw in software from the firm Schneider Electric poses serious security risks for industrial control environments, according to a report by the firm Indegy.
A vulnerability discovered in Unity Pro, management software sold by Schneider, allows any user with access to the system to run code on any computer on which the software is installed, Indegy said. Practically, the flaw has a wide reach: the vulnerable software tool runs on engineering workstations used in every control network in the world that uses Schneider-Electric controllers. As such, the vulnerability impacts “virtually any process controlled by these PLCs,” Indegy said, referring to Schneider Electric’s programmable logic controllers.
“Since Schneider Electric is one of the largest industrial control equipment providers, this vulnerability is a major concern,” the company wrote.
In response to the issue, Schneider released a patch for the Unity Pro software that fixes the vulnerability. It can be downloaded here.
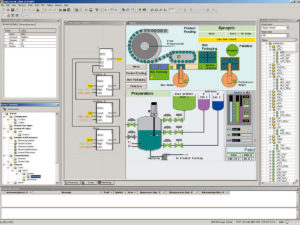
According to Indegy, the flaw can be found in every version of the Unity Pro software, a Windows-based application. It was discovered in a simulator component that allows engineers to test industrial controller code prior to running it on the PLCs. The control code projects are compiled as x86 instructions and loaded onto the PLC Simulator using a proprietary format named ‘APX’, Indegy said.
Indegy discovered that a knowledgeable attacker could use Unity Pro to author a particular control flow that would cause the PLC to execute arbitrary malicious code. That would be a high bar to clear if attackers needed to have physical access to the Unity Pro workstation to run the malicious apx file, but Indegy researchers discovered that Unity Pro is designed to accept .APX files from remote locations and run them locally in their simulator.
Attackers would need to create a large project file with what Indegy described as “random binary PLC code.” That code would then be replaced with shellcode used to infect the target system and a malicious payload. The malicious file would need to clear some checksum verifications, but could be downloaded to the target workstation via a TCP port that the Unity Pro leaves open by default.
Attacks would be difficult to detect in industrial control environments because the malicious APX file is an engineering control-plane activity, executed over a proprietary protocol. That means typical network intrusion detection tools would not have visibility into the traffic.
“The use of proprietary protocols for control-plane activities is a common yet misunderstood practice in ICS networks,” Indegy wrote. “Unlike IT networks where data-plane and control-plane activities are executed over the same communication protocols, in ICS networks different protocols are used for these activities.”
The most dangerous manipulations to ICS/SCADA networks and industrial controllers take place in the control plane using “proprietary, vendor specific protocols which are unnamed, undocumented, and unmonitored,” Indegy said.
The ramp up in threats to industrial control systems has given rise to new firms, among them Indegy as well as others, who promise to help companies that use industrial control systems monitor for threats against ICS equipment.
Vendors are also investing in security. Schneider on Wednesday introduced new cybersecurity protection services that it claims will help its industrial customers “manage and secure their connected plants.” The company is offering “Cyber Update services” that will automatically distribute Schneider Electric patches and endpoint protection, mirroring the types of features in common desktop environments like Windows and OS X.

