In-brief: Security firm FireEye is claiming to have discovered proof-of-concept malicious software that targets industrial control systems software that is used to operate critical infrastructure worldwide.
Security firm FireEye is claiming to have discovered proof-of-concept malicious software that targets industrial control systems software that is used to operate critical infrastructure worldwide.
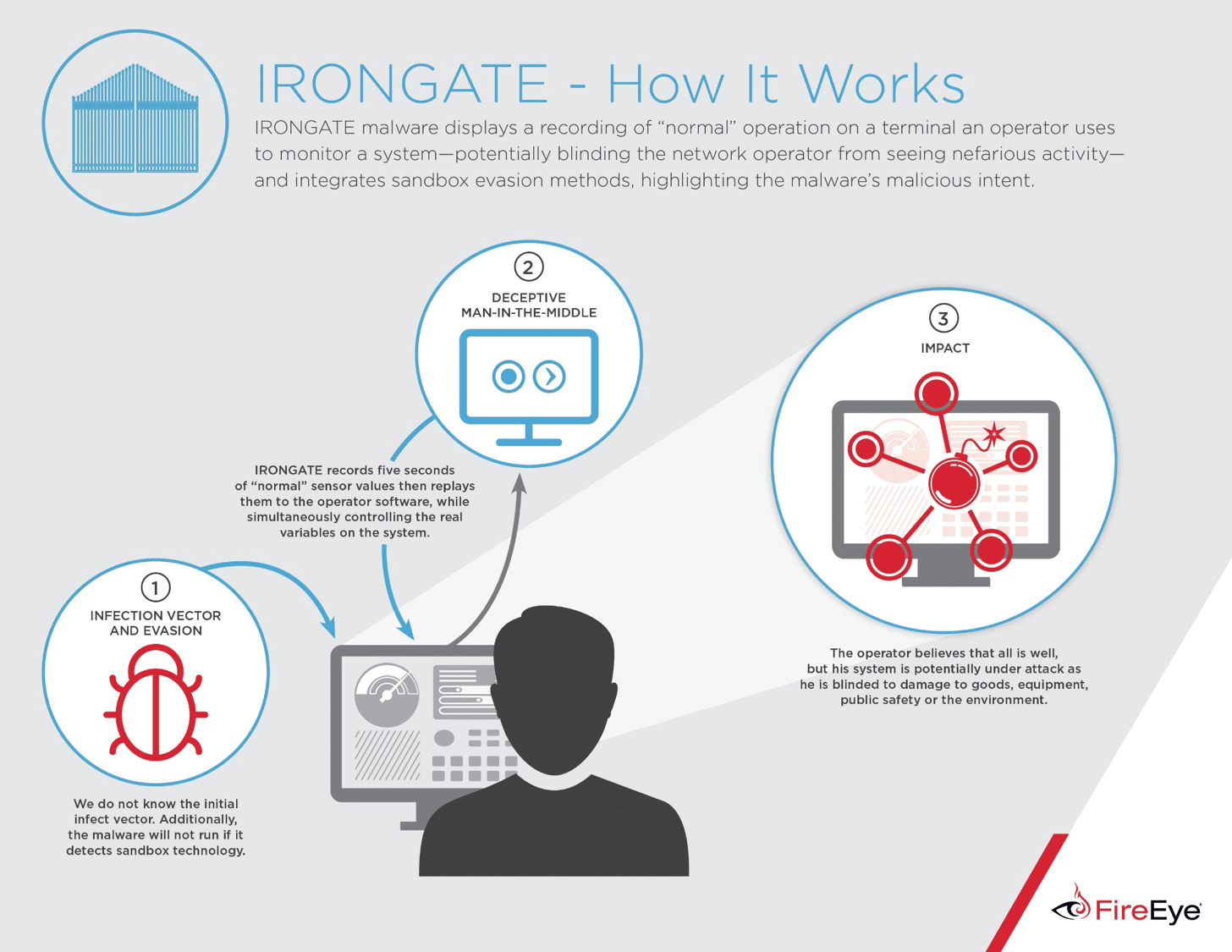
The malware, dubbed “IRONGATE” was discovered via VirusTotal, a kind of online clearinghouse for malicious software samples. While the software isn’t yet capable of infecting actual industrial control systems, FireEye warns that it suggests that malicious software authors are upping their game: adding evasion features that prevent the malware from being fooled by so-called “sandbox” environments and enabling sophisticated “man in the middle” attacks on applications used with programmable logic controller (PLCs) made by Siemens – the same equipment targeted by the Stuxnet worm.
FireEye cautioned that the malicious software samples its researchers discovered do not pose a threat to industrial control environments currently. The code would require “widespread changes” to actually attack Siemens programmable logic controllers.
[Read more Security Ledger coverage of Industrial Control System Security.]
Rather, the malicious software seems to suggest that malicious actors are testing out their creations before using them in actual attacks. Among other things, FireEye researchers observed the malware carry out a man in the middle attack against a custom-compiled user application in a Siemens Step 7 PLC simulation environment (PLCSIM).
The malware appears to be highly targeted: searching for a “single, highly specific process” and then replace a library used by the process in order to gain control over the application. And, in a throwback to the Stuxnet attacks against Iran’s Natanz Uranium enrichment facility, the malware is designed to fool operators into believing that all is well: recording 5 seconds of “normal” traffic from a simulated PLC to the user interface and replaying it, while sending hardcoded data values back to the simulated hardware behind the scenes, FireEye said.
FireEye worked with Siemens to study the malware but said that much remains unknown. The company does not yet know how the malware would spread and infect its victims or what might trigger the malware to launch a man in the middle attack.
The malware, currently, doesn’t pose a risk to industrial control system owners and operators. But it does alarms about what kinds of attacks they might face in the future, FireEye said.
Firms operating industrial control system hardware and software should implement more stringent checks for software updates to their ICS assets as well as “sanity checking” for IO (input/output) to ICS systems, to detect the kind of attacks carried out by Stuxnet and IRONGATE, where the operator is fooled into thinking a process is operating normally.
Malicious software targeting industrial control systems isn’t common, but it isn’t unknown, either. In addition to Stuxnet, malware like Dragonfly has been detected on business systems used to manage ICS environments. Further, hackers have claimed to be interested in selling information on vulnerable industrial control systems.
That has drawn the interest of traditional anti virus firms like Symantec and Kaspersky Lab, who see a role helping to protect industrial control environments from the kinds of threats that have traditionally targeted enterprise IT environments.
