In-brief: VNC Roulette is just the latest warning shot across the bows of industrial firms and the public sector: parading screen shots of remotely accessible but insecure SCADA systems for all to see.
The security of Internet-connected infrastructure was in the headlines last week, after the Department of Justice indicted an Iranian man, Hamid Firoozi, on computer hacking charges stemming from the hack of Supervisory Control and Data Acquisition (SCADA) systems controlling a small flood-control facility in Rye, New York.
Firoozi, it has been reported, used simple search engine queries (aka “Google dorking”) to locate The Bowman Avenue Dam and compromise the systems controlling it – just the latest evidence that ubiquitous connectivity is exposing sensitive infrastructure to remote and random attacks.
As if to underscore that message, a new website called VNC Roulette launched last week to make a display of vulnerable infrastructure, via a parade of screenshots of systems that use Virtual Network Computing (VNC), a popular remote access technology used to manage both personal computers and industrial control systems.
The project is the work of someone going by the name of Revolver on Twitter (@1×0123), “just another security guy” as he likes to describe himself.
VNC was developed more than 15 years ago and the source code was subsequently released as open source. It uses a client-server architecture, with the target system running a VNC server and the controlling system using a VNC client to access the server and remotely manage it. VNC uses the Remote Frame Buffer protocol (RFB) to send keyboard and mouse commands to the remote (controlled) system. There are VNC clients for most major platforms including Windows and Unix.
Security researchers have long warned about the risk of leaving the VNC connection (or any remote access technology) open to public access. VNC Roulette suggests those warnings are falling on deaf ears: compiling a database of snapshots of VNC-enabled systems including personal computers showing emails or social network profiles, to login screens for servers, closed circuit television (CCTV) cameras and medical equipment.
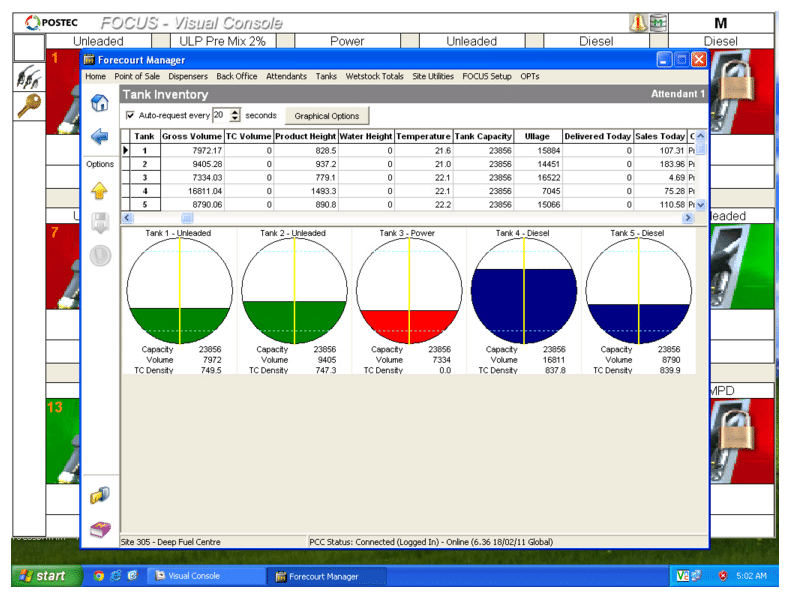
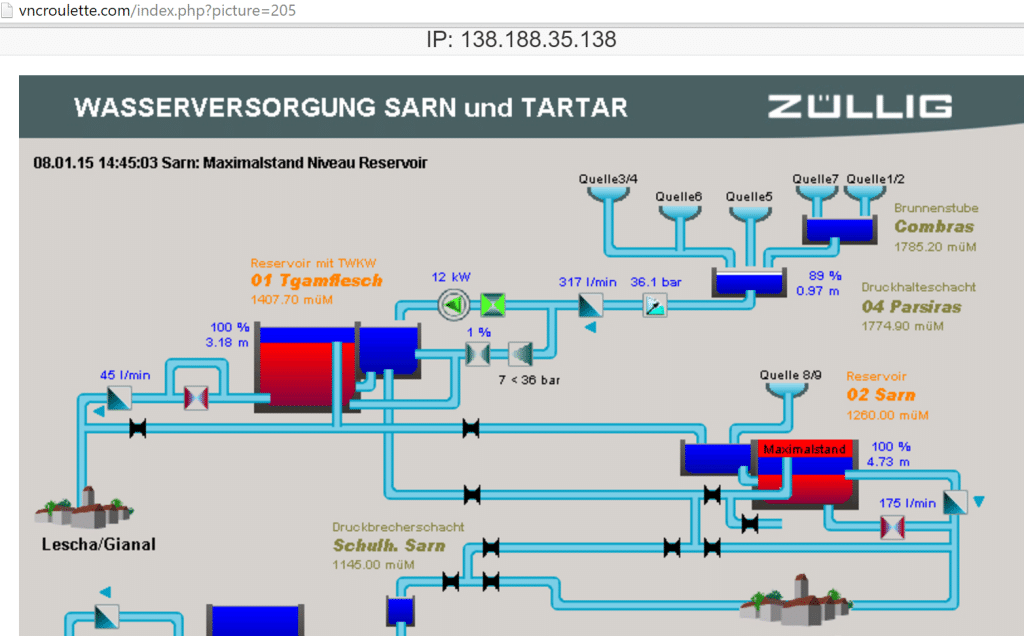
The database also contains images of control panels of industrial control systems (ICS)and SCADA equipment including back-up power generators, fuel tank management systems, sales management software, water supply systems, production machinery, and a control panel from Spanish mobile phone operator Movistar.
The systems captured on VNC Roulette database were accessed using a simple script and without the use of a password, according to this post, which explained the project. Vulnerable VNC servers were compiled from Whois databases. A web-based VNC script then tested to see if free remote (no password) access was possible. If so, a script connected to the system and grabbed a shot of the remote screen and active VNC session.
Easily accessible computers have a wide range of applications for cybercriminals, who can use them to launch remote attacks, distribute malware or steal credentials to different online services (banking accounts, email). Ransomware can be used to hold hostage the information stored on the vulnerable system and demand a ransom.
Among the systems depicted in the photo archive are a water supply system. The IP address suggests it is located in the Sarn and Tartar regions in Switzerland. Another image shows a Forecourt Manager application, a fuel tank management tool, running on a Microsoft Windows system. The IP address associated with the image suggests the system is deployed in New Delhi, India.
In a blog post published last week, Revolver said that the screenshot database was 23GB large with new machines being added. A report by Motherboard.com last week alleged that Revolver, identified as an unnamed Jordanian hacker, planned to sell the collection of unprotected VNC servers to Russian nationals for $30,000 and “disappear.” However, the site remained online this week.
VNC Roulette is just another red flag about the forest of insecure, Internet connected systems. The online provocateur and white supremacist Weev recently acknowledged responsibility for sending anti semitic fliers to tens of thousands of publicly exposed and insecure printers. Such systems can easily be located using tools like Shodan, a search engine for internet-connected devices that scours metadata the servers return to the client.
Reducing the risk of unwanted visitors though the VNC session is not a particularly difficult endeavor. Most remote desktop software offers password protection capabilities. Additionally, organizations can limit the connection to a “whitelist” of safe IP addresses and running communications through an encrypted SSH channel in order to avoid sniffing of the data by third parties.

Pingback: New Stuxnet-Like Industrial Control System Malware Ups The Ante | The Security Ledger