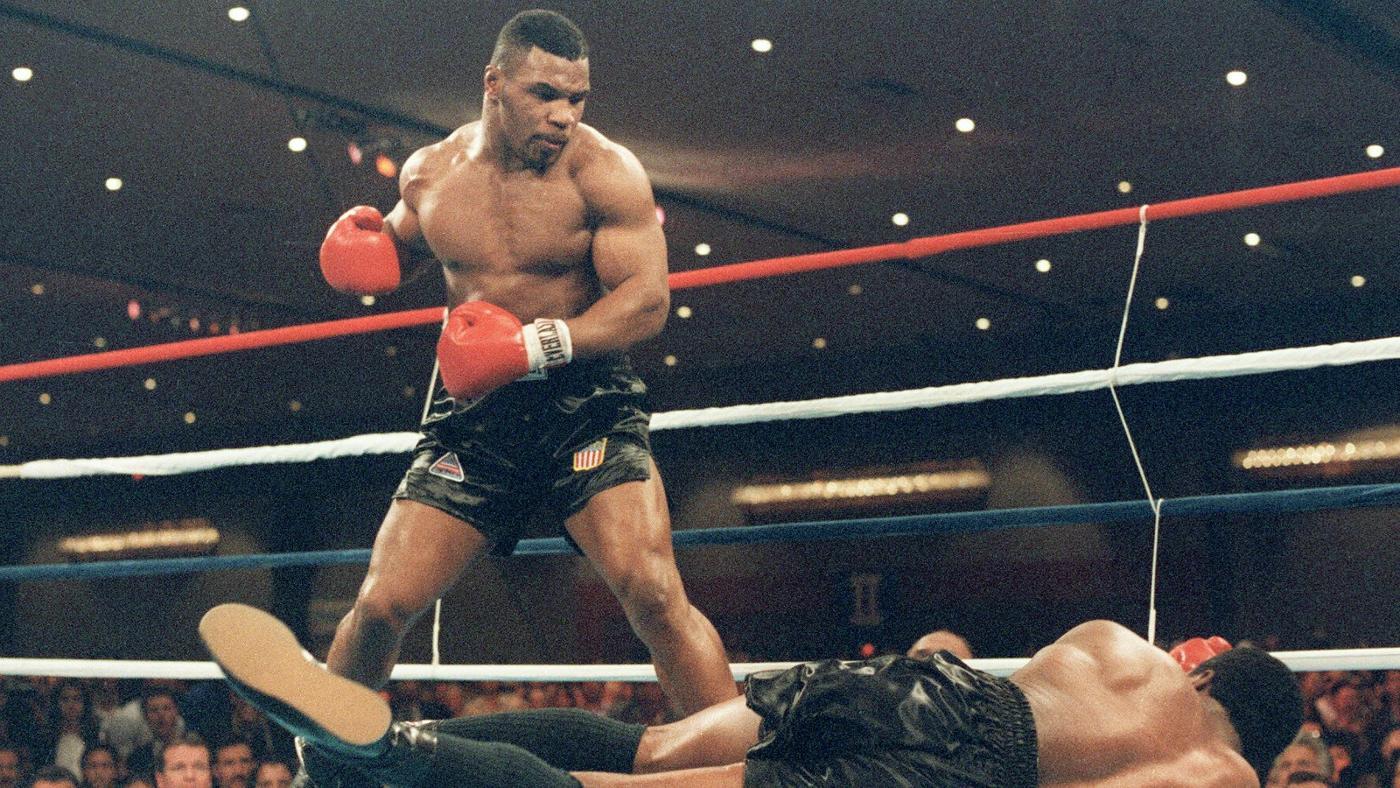
In-brief: Mike Tyson famously said of an opponent that ‘everyone has a plan until they get hit.’ That’s useful advice for information security teams worried about whether their existing network security plans will hold up to the onslaught of the Internet of Things, says Marc Blackmer of Cisco.
The pugilist Mike Tyson famously said of an opponent’s strategy for an upcoming match that “everyone has a plan until they get hit.”
It was a rare bit of wisdom from someone whose job was punching people in the head. The gist of Tyson’s statement is that meticulous planning under normal and controlled conditions goes out the window when an attack becomes reality. Now that the Internet of Things is broadening the already broad attack surface of enterprises, Tyson’s quote is becoming more relevant than ever.
The issue is this: good guys think alike. And we think like, well, good guys. We approach a network design project in a logical, process-oriented way to satisfy the requirements of external or internal customers. That’s a sound, proven method, for sure, but it is also our main vulnerability when it comes to protecting the networks we build. In short: we build defenses like defenders.

What we need to do is think, first, like attackers and then apply what insight we gain to our work as defenders. If you don’t break your network first and then learn how to fix it, the bad guys will be happy to break it for you.
Death by Lightbulb?
In fact: what makes you sure they haven’t broken it already? Just today, I had a conversation with my doctor about IoT cybersecurity (yes, he does ask me about these things). He was intrigued by the idea of smart light bulbs, but incredulous with the idea of a light bulb serving as an attack vector. “Why would anybody want to do that?”
Granted, my doctor’s expertise lies elsewhere (and he’s very good at what he does), but our conversation was very similar to the conversations I have with many people in the “biz.” Too many of us cannot see beyond traditional attack vectors and cannot understand why anybody would want to attack a light bulb, a connected car or other non-traditional targets.
The truth is that each device we add to our networks is a potential attack vector. It may not have the compute power to launch the attack, but it can be the first step to gaining access to the network and to IT assets that are suitable for launching or propagating an attack. My belief is that the more innocuous a device seems, the more necessary it is to get it into the lab and run it through its cybersecurity paces.
‘Where do I start,’ you’re wondering. Think about all of the devices on your network. If you wondered, ‘Why would anybody want to attack that?’ that’s a device you should be worried about.
Faster, better, cheaper: Choose two
I have spent enough time in IT shops ranging from a two-man IT operation to multinational enterprises to know that it’s much easier to talk about best practices than it is to fund and implement them. The reality is that most shops are pushed to their limits daily and have to fight just to keep up with their day-to-day responsibilities. Building out a lab to test products and then keeping up with testing is out of scope.
But we can’t just roll over for the bad guys. This is where the experts come in. Penetration testing (“pen testing”) by a professional third party is the best way to go for a number of reasons.
First, contracted penetration testers do not know your network. They think like attackers and will formulate their attacks based on what they can discover. This means they are far more likely to find vulnerabilities and attack vectors that you didn’t know were there.
Second, their reconnaissance techniques will include human engineering that would not be easy to pull off by in-house resources that may be recognized by the targeted individuals.
Finally, this is what they do – their jobs are to legally break into networks. They bring the experience of hundreds of engagements that will help you improve your security posture.
Bringing in a crack pen testing team may not be affordable for all organizations. That doesn’t mean nothing can be done. Investing in staff training can help you build out a basic penetration testing function within your own IT department. Simple red team/blue team exercises can identify network weaknesses and prepare staff to deal with adverse conditions.
To help foster security awareness with embedded devices, set up a capture the flag using a couple of $35 Raspberry Pis. Urge staff to get familiar with testing and hacking tools like Kali Linux, Wireshark, and the Shodan search engine. Use those tools to search your own IP space to look for rogue devices connected to the Internet, and use Kali’s utilities to look for and map rogue or misconfigured wireless access points. Wireshark will help you see what’s in the packets on your network.
Remember to always keep applicable laws and ethics in mind when testing. Keep management in the loop and involve your legal department as needed. It’s up to us to defend the IoT, and the more we can learn about offense, the better we can build our defenses.
Marc Blackmer is a Product Marketing Manager for Industry Solutions at Cisco Systems.

Hello Mr. Blackmer,
I was wondering, do you have an in-house Red Team? Or have you considered starting one? Does your company happen to hire people who have always been defenders, but with attacker mindsets? I like your article (this is something I rarely get to say enough on this site ;)), but I wanted to bring up something with regards to your statements about the whole ‘bring in a pentest team’. I kind of think in many cases pentest teams miss the point or aren’t appropriate; at the same time I’m wary of encouraging any user to come in and test security (it can INTRODUCE bugs — eg your Raspberry Pi idea — cool, but what if someone didn’t (or worse, did) know what they were doing and wound up creating a vector into your company’s internal network?
A lot of things can and should be solved in the hiring phase — and not just the security group hiring phase. I could discuss the Cisco backdoorability stuff as an example but it seems like overkill. Mostly I wanted to ask about your HR team’s familiarity with mindset — and if you have any way of testing it. I’m not fond of the whole Google Question To Hire thing (like the infamous manhole question), and I’m not sure HR would be able to catch things, but I do think that testing for the ability to think like an attacker and also pressuring hard to make sure that a potential hire is ethical through some trick questions can go a long way towards helping secure a team — in EVERY group (devs, managers, even HR people).
Not all I wanted to say, but it’s a start. Also, kudos to your bring up ethics in your last paragraph, especially after discussing using Wireshark to monitor networks. This is a very difficult thing to combine: monitoring networks and not impinging on peoples’ private communications (though I don’t know your awareness model there — perhaps permission to monitor is in the employment contract; still, someone exists to watch). I am a bit concerned btw about your suggestion vis a vis Wireshark, though… it speaks to me that you may not be segmented enough, if it’s that easy to catch someone via Wireshark (also there’s other ways to grab/monitor packets and be on networks that Wireshark wouldn’t pick up). I’d also recommend companies consider adding to their network team’s repertoire stuff like Bro.