
In-brief: General Motors (GM) has launched a program to entice white hat hackers and other expert to delve into the inner workings of its software. The reward: so far, a promise not to sue.
General Motors (GM) has launched a program to entice white hat hackers and other expert to delve into the inner workings of its software.
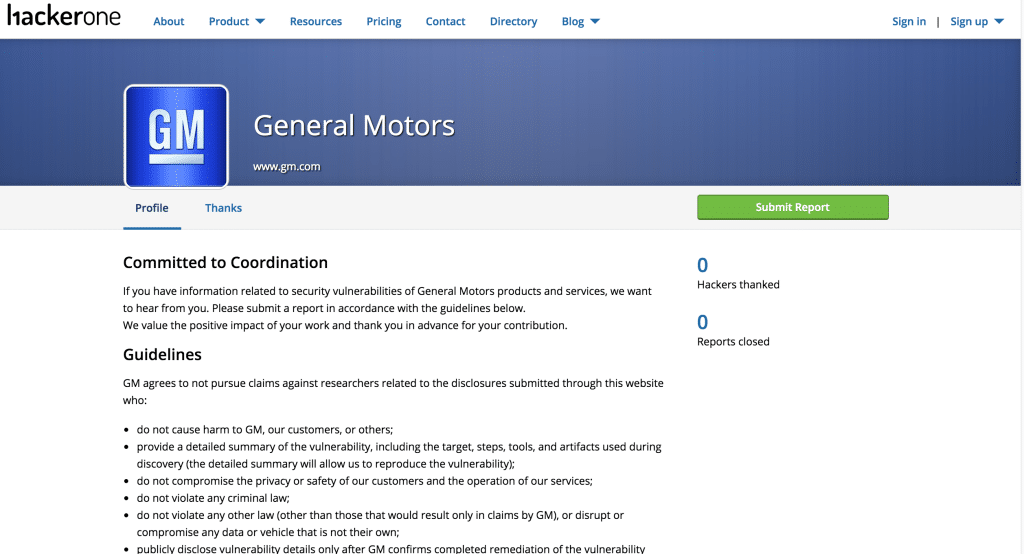
The company launched a bug bounty on January 5th on the web site of Hackerone, a firm that manages bounty programs on top of other firms, promising “eternal glory” to security experts who relay information on “security vulnerabilities of General Motors products and services.” The firm is not offering monetary rewards – at least not yet. A page on Hackerone detailing how vulnerability reporters will be thanked reads “Be the first to receive eternal glory,” but does not spell out exactly what rewards are proffered.
GM wouldn’t be the first “old economy” giant to delve into the world of bug bounties for information on software flaws and vulnerabilities. United Airlines recently launched a similar program on the Hackerone platform, offering rewards of up to one million airmiles to researchers who find remotely executable vulnerabilities in the company’s web properties (though not its planes).
GM’s program does not seem to be as restrictive, and doesn’t specify Internet domains as the subject of testing. Rather, the company promises to “not pursue claims against researchers related to the disclosures submitted through this website” as long as they meet a number of conditions, including:
- not harming GM, its customers or “others”
- providing details of their work
- not compromising the privacy or safety of customers or the operation of the companies services
- not breaking any laws
- Researchers must also promise to hold the details of their finding until GM confirms its existence and fixes the issue.
Security researchers who are working from Cuba, Iran, North Korea, Sudan, Syria or Crimea are barred from the program, as are researchers on the U.S. Department of the Treasury’s Specially Designated Nationals List.
Distinctly missing from the program is a monetary reward. That’s a bitter pill to swallow from a company with a $47 billion market capitalization. Bounty programs have become an important source of income for talented security researchers, some of whom earn hundreds of thousands of dollars a year finding holes in software from firms like Yahoo, Paypal, Twitter and Facebook. (Read my story “Glitches to Riches” over at Christian Science Monitor Passcode.)
GM earned immediate praise from security researchers Chris Valasek and Charlie Miller, whose research exposing security holes in vehicles manufactured by Fiat Chrysler attracted worldwide attention.
“Great step in the right direction to Massimilla and the whole GM team,” wrote Chris Valasek of Uber (@nudehaberdasher) in a Twitter post, an apparent reference to Jeff Massimilla, GM’s Chief of Cybersecurity.
Valasek said offering security researchers a contact and a way to disclose vulnerabilities was important, even in the absence of a monetary reward.
Still, some researchers are skeptical that firms are willing to “walk the walk” when it comes to addressing and fixing reported vulnerabilities. “If we waited for Chrysler before disclosing the jeep hack, I bet it still wouldn’t be fixed,” wrote Valasek’s research partner Charlie Miller (@0xCharlie) on Twitter.







Really need to impose a time limit on how soon they have to fix it before disclosure. 60 days is the industry practice. As it stands now, they are simply imposing a gag order on vital security flaws — flaws that, because they impinge on the control domain, may have safety-critical implications. Where’s the “eternal glory” in that? If flaw is exposed in the forest by no one is allowed to hear about it …
The company should get smart real quick if they know what they have started…..These hackers usally have a big ego that goes with their talent and if the company is smart they should reward and appeal to these guys for help..The money their going to save on Research and Development{R&D} is well worth rewarding these guys…If its done for Good and not for criminal rewards…..
Pingback: GM's Launches Bug Bounty Program Minus the Bounty – Hacker Planet
what about big auto killing off inventors who create ways to lower dependence on oil by increasing mpg’s? fuck all 3 of the big auto manufacturers in America they are all hoarding intellectual property and are in league with big oil. Don’t help these guys they are corrupted. That’s why they want to privatize work done on vehicles. GM is not for open source mods. Hey GM go eat a dick http://boingboing.net/2015/05/21/gm-says-you-dont-own-your-ca.html
Pingback: General Motors запустила собственную Bug Bounty program, но без вознаграждений | IT-Solutions
Pingback: General Motors launched its own Bug Bounty program, but without remuneration
Pingback: Podcast: Craig Smith of OpenGarages on Vehicle Security and GM's Bug Bounty | The Security Ledger