Software developers working within the automotive industry are pessimistic about their ability to secure connected cars. A lack of support from employers is a big reason why, according to a Ponemon Institute survey.
In-brief: Software developers working within the automotive industry are pessimistic about their ability to secure connected cars, a Ponemon Institute survey reveals.
The challenges facing automakers who want to connect cars to the Internet have been demonstrated in dramatic fashion in recent months, as hackers have demonstrated techniques for launching remote attacks on connected vehicles.
But for those hoping that future generations of vehicles will repair the security failings in late-model cars, a new poll out from The Ponemon Institute gives reason for pause: almost half of software developers working for OEMs (original equipment makers) and top suppliers to automakers believe that it will be ‘nearly impossible’ to hack proof cars.
Developers working to create the software that runs within modern vehicles have deep misgivings about the security of the code they are creating. Sixty nine percent of those polled said that securing applications that run in vehicles is “difficult” or “very difficult” and close to half – 48%- believing that a major overhaul of the car’s entire software architecture would be required to make it more secure. A sizable minority – 47% – expressed the belief that making a car “nearly hack proof” was impossible, Ponemon reported.

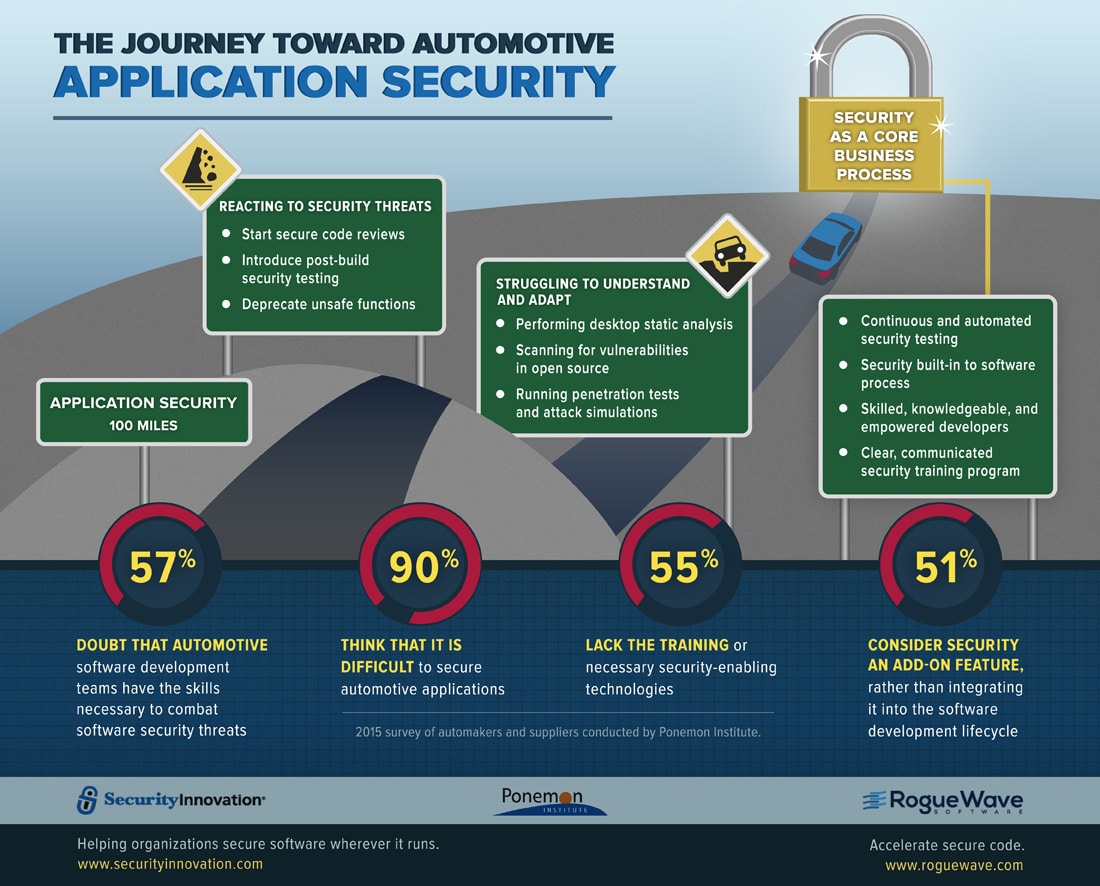
The survey, conducted by Ponemon and underwritten by the firms Security Innovation and RogueWave Software polled more than 500 automotive developers, engineers, and executives at automotive OEMs and Tier One suppliers. (Download a copy of the report here.)
The survey identified a number of common complaints that may contribute to the pessimistic attitude within the profession. Chief among them was a failure by their employer to emphasize and enable secure development.
[Read more coverage of connected vehicle security here.]
For example: 24% of those polled reported that pressure to develop code and meet deadlines takes precedence over making code secure. Twenty two percent reported that security was “not considered important” by their employer. An identical percentage reported that making code secure “takes too much time.”
Developers want – but do not have – the skills necessary to combat software security threats and they do not feel they are properly trained, Ponemon concluded. Nearly three-quarters of those polled – 72% – disagreed with the statement “I believe that automakers are as knowledgeable about secure software development as are other industries.” Just a quarter of those surveyed said they adhered to secure coding standards or conducted high-level assessments of their code and a minority of those surveyed – 45% – reported that their development processes including activities in support of security requirements, the survey found.
The results of the Ponemon survey come out amid other evidence that the rush towards a future of connected vehicles is giving experts and policy makers pause. Notably: the Government Accountability Office (GAO) issued a report in September (GAO-15-775) on the challenges of vehicle-to-infrastructure (V2I) technologies and identified a number of challenges to implementing them. Among them: “developing and managing data security and addressing public perceptions related to privacy.” There again, less than half of 21 experts surveyed by GAO were confident that systems could be developed to manage communications between connected cars and connected infrastructure securely.
More attention to security within development organizations and an investment in tools to help application developers address security issues during the design and development process could help improve the quality of the application code produced, the report concludes.
That’s the approach Microsoft took more than a decade ago in the wake of then CEO Bill Gates’s “Trustworthy Computing Memo.” In addition to implementing a secure development lifecycle (SDLC) company-wide, Microsoft pioneered the creation of automated software testing tools, which it then trained more than 10,000 developers to use.
“You need repeatable processes and a set of tools to support them,” Tim Rains, Microsoft’s Chief Security Advisor in the Worldwide Cybersecurity Business Unit said on Monday at the ISSA International Conference in Chicago.
But there’s worrying evidence that the automotive industry may be going in the opposite direction: looking for help from courts to discourage security research on cars, for example by using the U.S.’s Digital Millennium Copyright Act (DMCA) and the threat of litigation to scare researchers.
A substantial minority – 43% – of the developers surveyed felt that white hat hackers should be subject to the DMCA, slightly more than the 42% who felt that they shouldn’t be. But even among that more charitable population, more than half (54%) said that security researchers “shouldn’t be encouraged to test car software,” the report said.
The Electronic Frontier Foundation has warned that recent hacks of connected cars, like the Jeep Cherokee, underscore the need for independent security testing of vehicles.