In-brief: Pharmacy chain CVS and discount chain Costco acknowledged this week that a July security incident involving a third party firm that provides online photo processing and printing services resulted in the theft of some customer data. (Updated to add comment from Staples and CVS. PFR Sept. 16, 2015)
The pharmacy giant CVS and discount wholesaler Costco acknowledged this week that a security incident at a third party firm it uses to provide photo processing services resulted in the exposure of customer data including credit card information and e-mail addresses.
Customers of the two stores were advised to change their passwords and to beware of scams in the wake of the incident, which stems from the hack of third party online photo service PNI Digital Media in July. However, questions remain about the extent of the breach and its impact on other, large retailers including Sam’s Club and Rite-Aid.
In an e-mail dated September 11 and signed by CVS Vice President and Chief Privacy Officer Neal Baker, the company admitted that a reported breach at PNI Digital Media “potentially resulted in the unauthorized acquisition of data entered by certain customers on CVSPhoto.com.” Data exposed included customers’ first and last name, phone number, email address and user name and password. Some customers using CVSPhoto may have also had credit card information stolen, according to Mike DeAngelis, CVS’s Director of Public Relations. Costco separately acknowledged to its customers that some users of its online photo store may have had credit card information stolen directly from the site during their shopping session if they used the site between June 19 and July 15th, 2015.
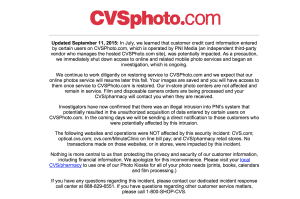
The admission by CVS and Costco that customers lost data in the breach is the first indication that the incident involved the theft of personal and financial information. It follows a forensic investigation of the incident, which was first reported in July. The incident resulted in the suspension of activity on CVSPhoto.com, Costcophotocenter.com and other sites for more than a month as an investigation ensued.
PNI, of Vancouver, British Columbia, was acquired by Massachusetts-based Staples Inc. in 2014. In a statement on Wednesday, Staples said that its investigation of the incidents “suggest that an unauthorized party entered PNI’s systems and was able to deploy malware designed to capture user input on PNI’s servers that support some of its customers’ websites.” Customer photos and “PIN numbers” (?) were not affected, according to an e-mail statement by Mark Cautela
Staples’ Director of Corporate Communications. Catuela declined to say how many individuals were affected by the breach or how long it lasted. The company is working with “outside security experts to determine the nature and scope of the incident, including what user data was impacted and the time period involved,” he wrote.
“We take the protection of information very seriously and have taken steps to remedy this incident and to further enhance the security of PNI’s network. It is important to note that consumers are not responsible for any fraudulent activity on their credit cards that is reported on a timely basis,” Catuela said in an e-mail message sent to The Security Ledger.
The effects of the breach have been felt far and wide. In addition to CVS and Costco, retailers Sam’s Club and Rite-Aid also used PNI and may have been exposed in the incident. As of Tuesday, CVSPhoto.com remained offline, with customers instructed to use the pharmacy chain’s in-store photo centers to process orders. Those centers were not affected in the breach, CVS said in a notice on its web site, nor were the pharmacy’s other in-store and corporate systems.
Official response to the breach have varied in the weeks since it became public. In an e-mail dated September 7, Costco said that its online photo site, Costcophotocenter.com, was back online. That, despite the fact that “some Costco members who typed credit card numbers onto the site during the compromise window had credit card information (including security code and expiration date) taken.” The customer’s name, phone number, billing address, email address, password and ship-to information may have also been exposed but “stored credit card numbers or photos” were not believed to be compromised, Costco said. Despite brining some photo store features back online, Costco said that full access to customer photos will not be available immediately, with photos from 2013 or earlier inaccessible “for another few weeks” – a suggestion that the relaunch of PNI’s service is not yet complete.
The company did not immediately respond to a request for information about the breach.
Still other affected retailers have yet to update customers on the conclusions of the investigation such as Riteaid.com. Others, like Sam’s Club, have restored their online photo store and describe a fairly low level compromise in which no data or photos were compromised in the incident at PNI. Sam’s Club even suggested that updating the password they used at PNI was “optional,” suggesting the impact of the breach was felt unevenly across PNI’s customer base.
Breaches and other security incidents at third party vendors are a growing risk for both online- and brick and mortar retailers.
The home improvement giant Home Depot acknowledged in November that cyber criminals who attacked the company’s network first gained access to the “perimeter” of Home Depot’s network by way of a user account at a third party contractor. The attackers were able to move within its network by elevating their level of network access and install what Home Depot described as “unique, custom-built malware” on self-checkout systems in the U.S. and Canada.
Target, the box store retailer, sketched out a similar scenario to describe the breach that resulted in the theft of 70 million credit cards numbers from its customers. In that case, a company that serviced HVAC systems in Target’s headquarters was reported as the source of the breach. The most recent Payment Card Industry Data Security Standard, Version 3.0, raises the bar for security requirements that third party vendors must meet in order for downstream customers to be considered PCI compliant.
But the impact of third party falls well outside of the retail sector, as well. In July, the Indiana Attorney General revealed that four million patients of more than 230 hospitals, doctors offices and clinics had patient data exposed in a May hack of Fort Wayne, Indiana firm Medical Informatics Engineering (MIE) and its NoMoreClipBoard electronic health records system. That breach affected healthcare organizations from across the country, ranging from prominent hospitals to individual physicians’ offices and clinics.
