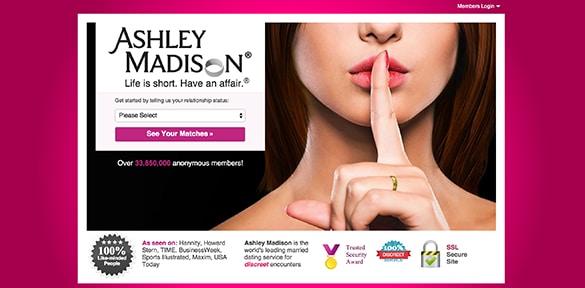
In-brief: Following a security breach, Avid Life Media, the parent of Ashley Madison and other adult-focused hookup sites, said that it was on the trail of the culprits. The question is whether ALM and its various properties will survive the incident.
Ashley Madison, a “hookup” site for married people is the latest, prominent online service to suffer a hack. According to a report by Brian Krebs at Krebsonsecurity.
The attack against the site’s parent company, Avid Life Media (ALM), affects Ashley Madison and two sister sites: Established Men and Cougar Life. In a message posted on the site Pastebin, a group calling itself Impact Team takes responsibility for the hack. The post includes information on a handful of Ashley Madison account holders – potentially embarrassing disclosures given the nature of the site. The company claimed Monday that it was hot on the trail of culprits. The question now is whether ALM and its various properties – whose reputation is based on discretion – will survive the incident.
Krebs first reported the breach Sunday, noting “large caches of data” from AshleyMadison.com that were posted online. Data from the breach was posted online alongside claims that the attackers gained total access to ALM network, obtaining information on some 37 million members as well as credentials for ALM employees, source code and more. The connection between whomever was responsible for the attack and those who posted the information is not clear. Nor is the motivation for the incident, though the message announcing the compromise suggested that anger over unethical business practices at ALM was the cause.
Among other things, the attackers noted that ALM appeared to make false promises to customers that they could erase their accounts by paying a one-time fee to the company. While customers who paid the fee had some data erased, enough was retained to easily identify those customers, according to the post by Impact Team said in its post.
Speculation in the wake of the attack has turned to a third party with access to- and knowledge of ALM’s network. In a statement to reporter Brian Krebs this morning, ALM CEO Noel Biderman said an investigation of the breach had identified an insider as the source of the breach, though it appears that individual was not an employee but someone who had “touched our technical services,” according to Krebsonsecurity.
In a statement released to media. ALM reminded the public that it was just the latest company to suffer a breach.
Indeed, data breaches are common at organizations across our economy, as the recent struggles of the Federal Office of Personnel Management and drugstores CVS and Walmart attest. Needless to say, most companies survive them – for better or for worse.
But not all companies – or all hacks are equal. And history has shown that firms whose core business is security and privacy face a particularly steep climb out of the hole left by a major compromise. Notably: the Dutch certificate authority Diginotar (part of the firm VASCO) was forced to declare bankruptcy and cease operation after it was compromised in 2011.
In the case of ALM and its various hookup sites, security experts caution, the injury caused by the compromise could be too grievous to overcome.
Steve Ward, a Senior Director at iSight Partners said he has been quipping for a couple years that the country’s real Digital Pearl Harbor won’t be a breach of critical infrastructure, but a compromise at Ashley Madison.
Madison said he used the online affair site as an example of a breach that would “make people to sit up and take notice.”As opposed to credit card information, which is easily replaced, or health data, which is abstract, a breach at a site like Ashley Madison would strike at the core of many lives: marriage, family, home. “My thesis was that you needed a breach that hit them in a place where they’d feel it the most as individuals,” he said.
Ward noted that the public has exhibited a short attention span when it comes to incidents like the breach at ALM and this breach, also, may soon fade into the background noise of similar breaches – replaced in the public’s memory by the next security slip up. But he also acknowledged that ALM and its sites are in a unique position that is different from firms like Target or Home Depot. “There’s no question this is a unique outfit. There’s a fundamental expectation of confidentiality and privacy,” he noted. “This could pose an existential threat – will they retain their user base becomes public? Will the confidence be there?”
Other security firms echoed that sentiment in their comments on the breach.
“This is an organization that relies on discretion and its clearly not meeting the requirements to provide both security and privacy that it brands itself on,” said Pete Tyrrell, the Chief Operating Officer of the firm Digital Guardian* in an e-mail statement. “As it stands, the breach will likely cause irreparable damage to Ashley Madison’s business and reputation.”
“This is devastating for ALM,” said Eugene Kuznetsov, the Chairman and co-founder of the firm Abine, which makes products that allow consumers to mask their identity online. Beyond that, however, Kuznetsov wonders whether the entire business model that companies like ALM rely on may be on the route to extinction.
“The fact is that data is nothing more than toxic waste. The more you accumulate, the more at risk you are for an accident like this.”
Despite promises of security and privacy, no company in the current environment can claim to be able to protect data from all attackers, Kuznetsov. Businesses that think they will be able to monetize the customer information they collect may find that hackers and other malicious actors find a way to do so before the company does. “The fundamental reality is that you can’t have all this data in big databases connected to the Internet,” he said.
The solution? “Just don’t retain records,” Kuznetsov said. “This is like toxic waste. You have to clean it up – you’ll have far less exposure and far fewer problems if you don’t retain the data forever.”
(*) Digital Guardian is a sponsor of The Security Ledger.

“The solution? “Just don’t retain records,” Kuznetsov said. “This is like toxic waste. You have to clean it up – you’ll have far less exposure and far fewer problems if you don’t retain the data forever.””
Someone is clearly talking out of their ass again. Was this some canned response he meant to dole out drolly about someone who dropped a USB stick full of hospital records from 2007 but never got a chance to use? Active accounts require records. The problem here wasn’t data retention (certainly not ‘forever’ — and I’m against long-term data retention).
What’s more the way the hack and data were ‘exposed’ is highly strange/unusual and outright contradictory. That’s probably the real story.
This is like a who’s-who of potential sponsors, Paul. I like your site, but I’m kind of cringing.
From that pastebin: “We are also releasing…executives’ google drives…” [sic]
I would hope that this meant that the attackers got to those Google Drives because those Google Drives were directories on a compromised Ashley Madison computer or the executives Google accounts used a duplicate password and also did not have two-factor authentication. I’m hoping that the attackers have not figured out how to compromise Google’s security. Paul, would you please investigate/comment?
Philip, I am not Paul, nor do I have any connection to this site (I figure that’s obvious), but I hope you don’t mind if I chime in.
Having done quite a bit of research on post-breach analysis in general, the more likely scenario is that the ‘execs’ were sloppy with their passwords (leaving them in files, for example), the access was sniffed, or the data itself was just collected while the drives were connected. If one is to believe the attackers’ pastebin, then they had access for years. Sniffing (perhaps with compromised binaries) is far more common and easy than compromising Google, on principle; so would, in the case of two-factor auth, just waiting and piggybacking in on the access.
That’s my theory, if it is an *outsider*. But it’s probably not a great idea for any of us to theorise on this stuff until more facts come out — it could very well have been an inside job. And there are aspects about that pastebin post which suggest something like ‘personal slight’. A good question to ask: Why do things publicly? It’s like someone’s been taking hints from the Sony case, IMHO.