
In-brief: RSA said it detected evidence of a malicious software campaign that targeted employees at point of sale vendors – a possible effort to compromise the PoS supply chain.
For companies concerned about securing their infrastructure, nothing is more frightening than the notion of buying compromised hardware and software – “certified pre-pwned,” as it were. But while that threat has mostly the stuff of Hollywood screenplays and “what if” scenarios, there’s increasing evidence that the threat is real. [Updated to include comment from Alex Cox of RSA. PFR 4/30/2015)
The latest sign of smoke comes from RSA, which wrote on Wednesday about what is describes as an attempted “supply chain subversion” attack against prominent point of sale (POS) hardware vendors.
In the post, RSA describes a sophisticated “spear phishing” campaign against a European POS vendor. The attackers used e-mail from a malicious domain disguised to look like a well-known and high end New York City restaurant. The message complains about POS systems “crashing” with “blue screens of death.” Characteristics of the attack, including malicious software used and domains used for command and control suggest the campaign is part of the PoSeidon campaign identified by Cisco in March.
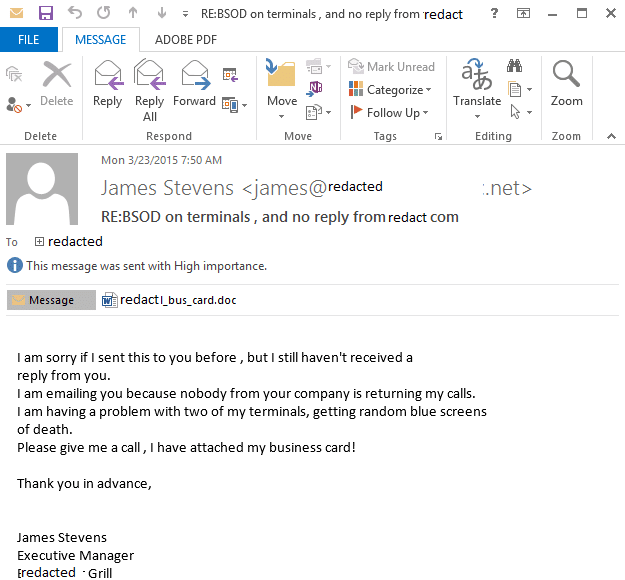
The e-mail messages were sent to a “small number of employees” of the Point of Sale system vendor, said Alex Cox, the senior manager of RSA’s Threat Watch security group. The e-mail message content was catered to that audience, though RSA said it was not clear whether a merchant (the New York restaurant) was compromised and used to launch an attack upstream against that merchant’s point of sale vendor, or whether the attackers merely stood up malicious infrastructure to mimic a legitimate merchant with the goal of targeting the PoS vendor.
A malicious Microsoft Word document attached to the e-mail, if opened, installed a copy of the Vawtrak banking Trojan, which is adept at credential theft and can be easily modified for use in a variety of scenarios, Cox told Security Ledger.
[Read more Security Ledger coverage of supply chain risks.]
But the company said the goal of the attack was apparently to compromise the vendor itself, providing an avenue to “realize subversion of the vendor’s firmware or software built into the products.” While a high risk gambit, a successful supply chain compromise carries the promise of granting back door access to a vendor’s entire installed customer base, RSA notes.
“Based on the way we’re seeing criminal elements and (advanced persistent threats) escalate, its not too big of a leap to think that they might be targeting firmware,” said Cox, who called that a “worst case scenario.”
Reasonable quality assurance practices should catch any attempt to make modifications to the Point of Sale firmware. However, recent history tells us that such attacks aren’t impossible. Specifically: the Zombie Zero attack identified in 2014 by the firm TrapX was evidence of malware that infiltrated a shipping and logistics firm as a compromised firmware update for the scanning hardware used by the firm. The malware was discovered in a software image that could be downloaded from the manufacturing firm’s website.
TrapX says that malware installed on scanners used by shipping and logistics firms resulted in compromises at eight firms, including a leading Robotics maker.
A more likely outcome would be that attackers, having gained a beach head inside the point of sale vendor’s network would exploit its connections to its customers and business partners to gain access to their networks.
In the case of the Point of Sale attack, the objective may have been to establish lateral access to merchants through their point of sales systems. Companies can make it easy for attackers to conduct those attacks. RSA notes that the point of sale vendor targeted in the campaign posted logos for more than a hundred commercial and technology partners as well as systems integrators. Those companies would be downstream victims of any successful supply chain campaign, RSA noted.

Pingback: RSA Warns of Supply Chain Attack on Point of Sale Vendors - Procurement Professionals