
In-brief: IBM researchers say they have seen a spike in malicious activity linked to the Dyre family of malware. Sophisticated attacks on business banking accounts have led to the theft of millions of dollars, IBM says.
IBM says a new variant of some tried and true banking malware is behind a $1 million crime spree against companies in many industries, combining social engineering attacks and well-timed DDoS attacks to abscond with millions of dollars via wire transfer.
The report says that the Dyre (or Dyreza) malware is “one of the most effective banking trojans” online, accounting for a quarter of all malware attacks globally in the first three months of 2015. The malware, which first appeared in mid 2014, is linked to a “closed” cyber crime gang that operates from Eastern Europe. It is helped along by a steady stream of updates that help it avoid detection, advanced features and by the sophisticated knowledge of banking operations exhibited by those behind the Dyre campaign.
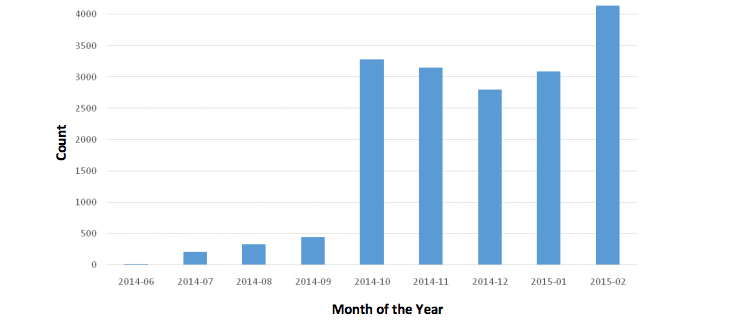
IBM recorded a jump in infections linked to Dyre in February, with in excess of 4,000 recorded by IBM globally, up from just over 3,000 in January, and fewer than 500 in September, 2014. This according to a report from the company: “The Dyre Wolf: Attacks on Corporate Banking Accounts.”
[Read more Security Ledger coverage of malware. ]
Among other things, the Dyre malware is capable of defeating so-called “two factor” authentication schemes used by many banks to protect access to customer accounts. Two factor authentication requires an account holder to enter a user name, password and an additional “factor” such as a numeric code that is sent to their mobile phone or generated by an application.
The Dyre malware, which is spread via malicious attachments posing as faxes and other documents, is capable of monitoring user activity and springing into action when users visit a targeted web site such as a bank. Using technique like web page injection attacks or redirection, the malware presents a phony web page, identical to the actual bank page, to users, collecting account information and login credentials in the process.
For select, high value targets, the malware is also capable of carrying out real-time, on the fly server-side injections, intercepting a user’s interactions with a banking web page and the responses from the bank’s servers. The malware then uses servers controlled by the attackers to present modified banking web pages back to the user with adapted code injections that are designed to harvest user credentials. In this scenario, the attackers can “communicate with victims in real-time, presenting them with carefully selected social engineering designed to complete a fraudulent transaction,” IBM said.
In still other scenarios, the attackers speak directly with their victim, posing as bank employees intent on resolving an “issue” with their account. Attackers in these scenarios can collect both the password and the one-time token needed to access the victim’s account.
IBM said it knows of several incidents in which amounts ranging from $500,000 to up to $1 million were stolen via illegal wire transfer from victim organizations. The attackers commonly launch crippling distributed denial of service (DDoS) attacks on the company immediately following the theft to distract resources and attention within the victim organization and to prevent them from getting access to their bank account, IBM said.

