
In-brief: a report from the firm CrowdStrike finds sophisticated nation-backed hacking groups were very active in 2014, with attacks on governments, pro-democracy advocates as well as banks and retailers.
A year-end report from the security firm CrowdStrike finds that politically motivated hacking is on the rise, while sophisticated malware attacks against banks and retailers took a heavy toll in 2014.
The warning comes in CrowdStrike’s Global Threat Intel Report (GTIR), which collects the company’s research from throughout the year. The security firm said that 2014 was rife with examples of politically motivated hacks and online attacks, from distributed denial of service (DDoS) attacks aimed at the government of Ukraine and suffragists in Hong Kong to the group LizardSquad’s attack on online gaming environments in Europe and North America.
CrowdStrike makes it their job to research, document and, when possible, name the malicious groups responsible for online attacks – and their backers. Its profiles of sophisticated hacker groups include names like “Deep Panda” (a Chinese hacking crew with links to the People’s Liberation Army), “Energetic Bear,” (a group with its base in the Russian Federation) and “Flying Kitten” (with links to the Islamic Republic of Iran).
[Read more Security Ledger coverage of CrowdStrike research here.]
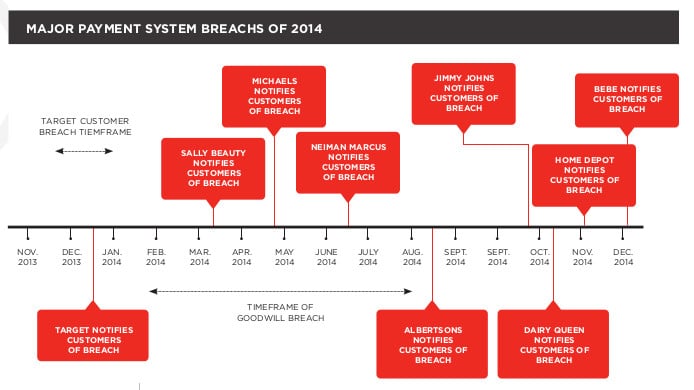
According to CrowdStrike, malicious actors found ways to best two-factor authentication schemes in 2014, leading to large-scale attacks aimed at online banking. In the retail space, point of sale (POS) credit card machines proved attractive targets to both sophisticated and pedestrian hackers during 2014, with attacks on retailers like Target, Home Depot and systems to make off with personal and financial information for hundreds of millions of people.
Speaking with The Security Ledger, CrowdStrike Chief Technology Officer Dmitri Alperovitch said that the perception of so-called “advanced persistent threat” groups as a problem only for high value and high profile organizations like military contractors, critical infrastructure operators and financial services firms was misplaced. Most organizations of any size, and across industries, have been targeted by APT groups like those CrowdStrike profiles, Alperovitch said.
Those firms often underestimate the determination of those groups to get access to sensitive IT assets and maintain a presence on their network.
“We find that most organizations still think of these attacks as discrete events,” Alperovitch said. “You get hacked, you clean up and then its over.”
But even companies that are successful in removing a malicious actor from their network often find that sophisticated hacker groups come back.
Alperovitch noted the work of one group, dubbed “Hurricane Panda.” CrowdStrike worked with what Alperovitch described as a “large, public technology company” to remove an infection linked to that group. However, after removing the Hurricane Panda group’s access to the network, it noted repeated efforts to regain access, including through the exploitation of previously unknown (“zero day”) software vulnerabilities to regain a foothold on the network. The group was also observed abusing free DNS services to disguise malicious communications and using Google Code to host malicious downloads – the better to mislead forensic investigators.
This year promises more of the same. CrowdStrike predicts more action by North Korea to boost its international standing through the use of cyber attacks. Sophisticated attackers will look for ways to exploit embedded or unmanaged Windows XP systems, as Microsoft ends support of that operating system. Third party providers of everything from content management to DNS services will also be targeted.
Still, Alperovitch said, despite the obvious successes of sophisticated hacking groups, that he is optimistic that 2015 may mark progress against such organizations. The U.S. government and law enforcement are working more closely with private sector firms to share intelligence about cyber attacks and to coordinate takedowns of malicious infrastructure, like the GameOver Zeus Trojan, he said. At the same time, the Obama Administration has announced plans to create a new agency to coordinate intra-government response to cyber incidents.
More and better sharing of intelligence, as well as better coordination with foreign governments may help raise the bar for attackers and make it easier to move against cyber criminal actors and raise the costs for governments that engage in state sponsored hacking, he said.

