The spectacular collapse this week of Code Spaces, a cloud-based code repository, may have been the result of a an unspectacular “opportunistic” hack, rather than a targeted operation, according to one cloud security expert.

The sudden demise of the online application repository has sent shock waves through the tech industry, laying bare what some say are lax practices among many cloud-based application and infrastructure providers. But the attack itself was almost certainly the result of a larger, indiscriminate cyber criminal campaign, said Jeff Schilling, the Chief Security Officer of Firehost, a Texas-based secure cloud provider.
“This is something we pretty frequently: companies get held ransom with a DDoS attack, and if that doesn’t work, (the attackers) will resort to doing other things,” Schilling told The Security Ledger.
But Code Spaces almost certainly wasn’t the only company the extortionists worked on, Schilling said. Instead, the company was likely caught up in a wide net thrown by the attacker -who either phished employee credentials or took advantage of weak authentication to gain access to the administrative panel used to manage its infrastructure.
“It’s like fishing with dynamite,” Schilling said. “They almost certainly sent out lots of emails and got one back that looked interesting…(Code Spaces) was a target of opportunity.: The collapse of Code Spaces at the hands of an unknown hacker has left many customers scrambling to recover source code hosted on the site and bemoaning the company’s apparent failure to institute basic security protections for its infrastructure.
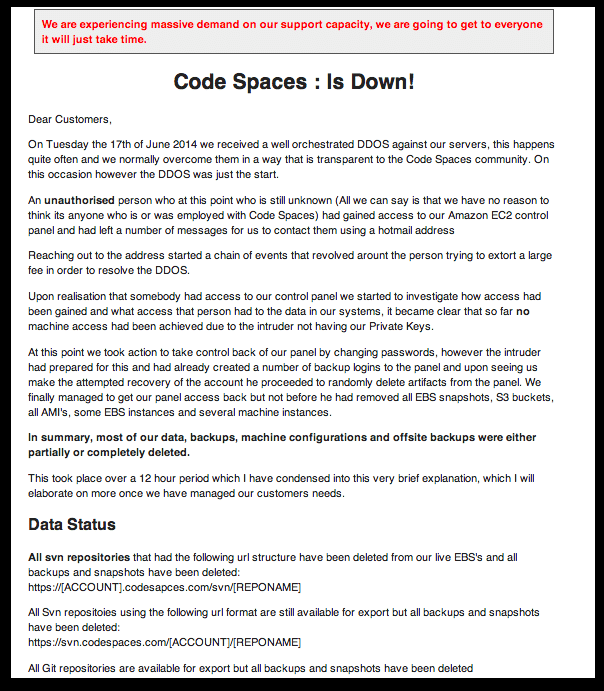
Six year-old Code Spaces was a UK-based provider of secure source code hosting and project management tools. The company, on Tuesday, posted a notice to its web page informing customers that it had fallen victim to an extortionist who crippled its servers with a distributed denial of service (DDoS) attack and gained administrative access to Code Spaces Amazon Web Services account.
Subsequent company efforts to lock out the the attacker prompted a retaliatory rampage in which “most of our data, backups, machine configurations and offsite backups were either partially or completely deleted.” The incident left Code Spaces unable to recover and, on Tuesday, the company called it quits, saying it needed to focus resources on “supporting our affected customers in exporting any remaining data they have left with us,” the company wrote.
In the wake of the incident, former customers and security experts have pointed to a number of apparent failings that left the company’s Amazon Web Services-based operations exposed.
First and foremost, Code Spaces still relied on simple user names and passwords to control access to their administrative console. That, despite Amazon Web Service’s support for multi-factor authentication options like text-message based one time passwords.
Code Spaces also appears to have used a cloud-based backup service that was accessible from the same AWS management console accessed by the hacker. That gave the intruder access to both the company’s production data and its backups.
Finally, Code Spaces opted to try to deal with the intrusion alone, rather than consulting with cyber incident response experts. The company’s ham-fisted efforts to lock the intruder out of its management systems prompted the deletion of customer- and company data. That included the deletion of all Code Space’s virtual machines and related cloud repositories.
Schilling, who was Director of Dell Secureworks’ Global Incident Response Practice and the Director of the Army’s global Security Operations Center under US Army Cyber Command prior to joining Firehost said that small operations are often lulled into thinking that they are too small to be targets of hacks and extortion, forgetting that attackers may act opportunistically.
Small firms often lack IT security expertise, as well – trusting IT staff to handle security incidents, he said.
Cloud providers like Amazon may offer security features, but customers often opt out of them, or don’t know enough to enable them when they are standing up their infrastructure. Cloud providers often face less scrutiny and due diligence than other kinds of application and infrastructure providers – especially when it comes to IT security, he said.
“As the saying goes ‘You can outsource services, but not responsibility,'” Schilling said.
Online extortion is a fact of life for high tech and ‘brick and mortar’ firms alike. Just this week, Reuters reported that the Finnish mobile firm Nokia paid millions to unknown hackers, who claimed to have discovered a vulnerability that would have rendered devices running the company’s Symbian operating system vulnerable to remote attacks.
Pizza giant Domino’s also acknowledged that it was being extorted for €30,000 by hackers who claim to have made off with sensitive data on some 600,000 of the company’s customers in France and Belgium. That breach appears to have been the result of an insecure web application.