The passwords to access more than two million online accounts have been recovered from a server that is part of the command and control network for the Pony botnet, a large and active network of infected computers, according to a blog post from the security firm Trustwave.

The company said that it found a cache of approximately two million compromised accounts, most from popular online services such as Facebook, Yahoo, Google and Twitter. More concerning: the cache also contained tens of thousands of credentials for FTP (File Transfer Protocol) servers, remote desktop and secure shell (SSH) accounts, and a site belonging to ADP, the payments processing firm.
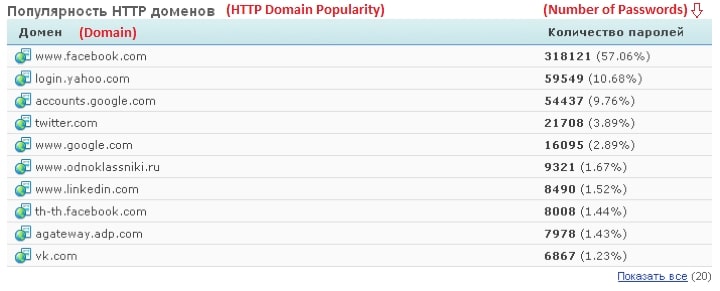
Facebook accounts made up the lion’s share of the haul, with 318,121 user credentials discovered – 57% of the total. Yahoo was the next biggest victim, with 59,549, almost 11% of the total. Leading Russian social networking sites vk.com and odnoklassniki.ru were also in the list of the top ten victim sites, suggesting the attack may have its origins in Russia or Eastern Europe.
The discovery is just the latest by Trustwave researchers to be linked to the Pony botnet. In June, Trustwave discovered a cache of some 650,000 credentials on a Pony botnet controller. Those passwords, also, were made up mostly of Facebook, Yahoo and Google accounts, in addition to stolen email account credentials, as well as FTP credentials.
The discovery suggests that the Pony botnet is still a potent threat. Analysis of the stolen passwords also provides proof that entreaties to the public to shore up the security of their logins isn’t working. Simple passwords like “123456” and “111111” made up 2.4% of all stolen passwords in the cache. More than three quarters of the stolen passwords were of “Terrible,” “Bad” or “Medium” quality, meaning they were too short and/or lacked a diversity of characters, according to Trustwave. Compared with an analysis of leaked MySpace passwords more than seven years ago, the percent of passwords that were of low quality was higher, while most users still chose relatively short six to nine character passwords.
“If our hypothesis is true,” Trustwave researcher Daniel Chechik wrote, “then the inevitable conclusion is that people still choose comfort over security. If you don’t enforce a password policy, don’t expect your users to do it for you.”

Google, Facebook, Twitter and LinkedIn all support two
factor authentication! If we all adopted 2FA, then these continuous password
leaks will become less of a concern – the perpetrator will only have one
factor.
Pingback: Obama Administration: Speak Up On Trusted ID Plans! | The Security Ledger