Watering hole -style attacks are all the rage these days, as our recent coverage on the attacks against Facebook and Twitter suggest. That makes us look askance at any report of a web site compromise – especially at a site that’s known to serve an audience that’s of interest to sophisticated, nation-state backed hacking crews.
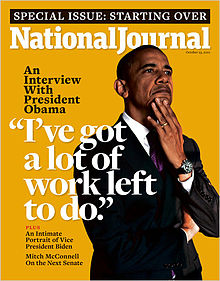
That’s why it caught our attention this week that the web site for the DC-insider magazine The National Journal (nationaljournal.com) was found serving malware.
According to a blog post by Anup Ghosh at the security firm Invincea, The National Journal’s Web site was serving up attacks to visitors of the site on Tuesday. The discovery was surprising, as the magazine acknowledged an earlier compromise on February 28th and said that it had since secured its site.
That National Journal, part of The Atlantic Media Company, is widely read within Washington D.C.’s political circles. It provides in depth coverage of national politics and policy issues.
Invincea’s analysis showed that the site had been compromised and an iFrame based redirect to a web site that hosted the Fiesta/NeoSploit exploit pack was discovered. That kit attacked visitors with exploits for two, known Java vulnerabilities: CVE-2012-0507 and CVE-2012-1723. For visitors with more recent versions of Java that protect against exploits of those holes, a separate redirect was included to an exploit kit that used Java object serialization to break the security controls of Java 7, Update 11, Ghosh wrote.
Those who were vulnerable to the attacks had a copy fo the ZeroAccess rootkit installed on their PC, as well as FakeAV, Ghosh said.
So – is this a watering hole attack, or just a run-of-the-mill web site compromise? Technically, there’s not much daylight between the two. After all, watering hole attacks, under the hood, are run of the mill web based attacks leveraging exploits for known or unknown vulnerabilities in common web browsers or browser components (like Java). What makes them different is the intentions of the attackers – they’re interested in just certain visitors to the site, not every possible visitor. And they’re passively hunting their prey (letting them come to the site) rather than actively hunting them (trying to hack their network or laptop).
Certainly, the profile of The National Journal – which is a staple of Beltway politicians and other policymakers – makes this hack look a lot like the compromise at The Council on Foreign Relations back in January. The Journal’s difficulty in beating back the attack underscores how tenacious web based attacks of any kind can be.
The incident also adds more fodder to the escalating tensions between Washington D.C. and Beijing over what U.S. policy makers have said is a wide ranging program of cyber espionage against the U.S. government and private sector firms.
So, while the site appears to have been cleaned of malware for now, its worth while using caution when visiting nationaljournal.com, at least in the near term!

Pingback: Twenty ISPs Responsible For Half Of All Spam | The Security Ledger