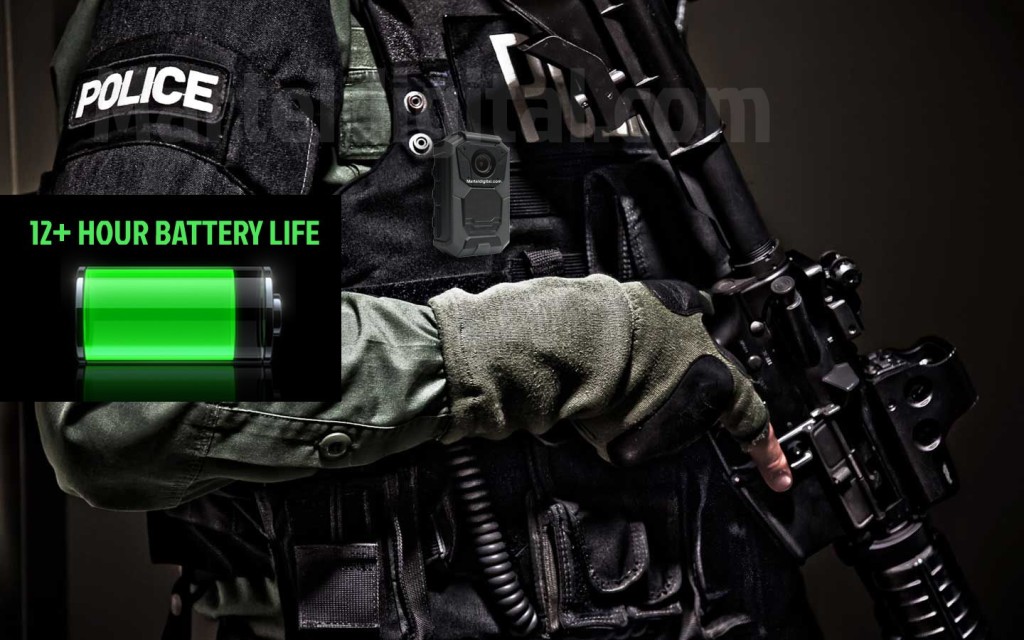
In-brief: a California company that makes wearable cameras that are used by law enforcement and the military said a report that it shipped cameras infected with the Conficker virus were “distressing,” but that it was unable to locate the malware on its devices or within its environment.
Tag: supply chain
Under The Hood: Wireless Software Links Teslas, Drones
In-brief: The same wireless software that powers a consumer quadcopter is also under the hood of Tesla’s Model S, according to a leading security expert – underscoring the increasingly long and complex software supply chain for connected products.
More Supply Chain Woes: DeathRing Is Factory-Loaded Smartphone Malware
The folks over at Lookout Security have an interesting blog piece on “DeathRing,” a Chinese Trojan that comes pre-installed on a number of smartphones most popular in Asian and African countries. According to the bulletin, the Trojan masquerades as a ringtone app, but downloads an SMS and WAP (or “wireless access protocol” ) content from a command and control server to the victim’s phone once it is installed. That downloaded content can be used for various malicious, money-making schemes, according to Lookout. For example, DeathRing can use the SMS content to send phishing text messages to the phone to elicit sensitive information from the user. The WAP content to manipulate a mobile user’s web browsing session. For example: the attackers might prompt victims to download additional mobile applications or add-ons, potentially extending their reach over the victim’s device and data. [Read more Security Ledger coverage of supply chain risks.] Lookout […]
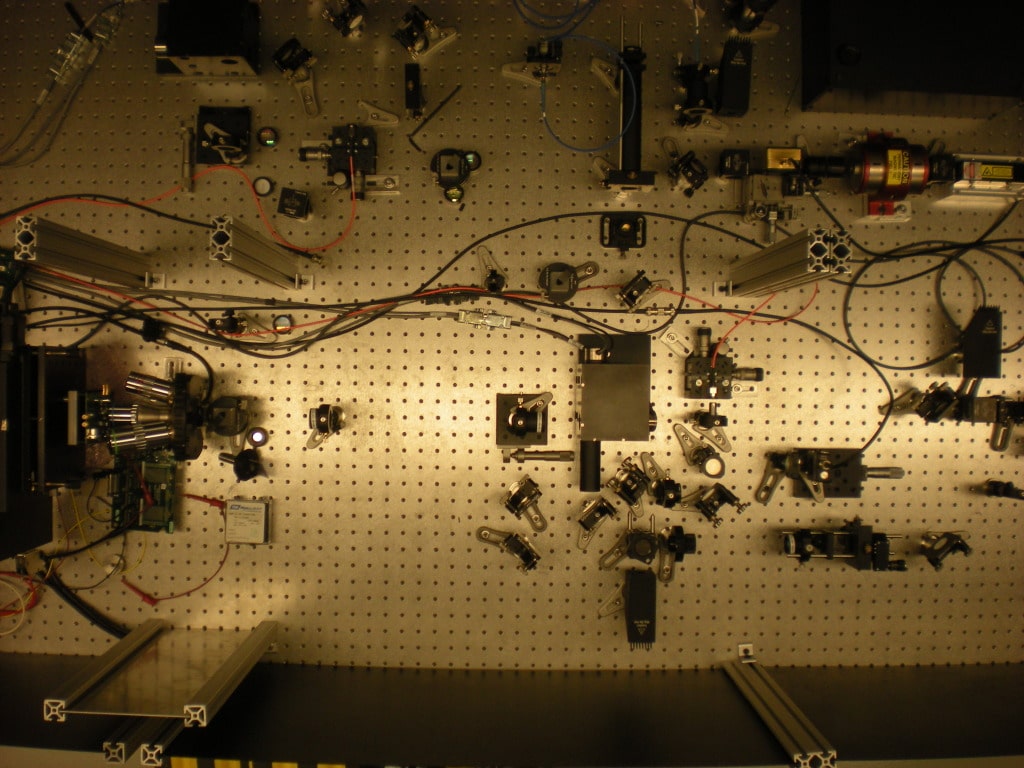
DARPA Tech Identifies Counterfeit Microelectronics
The U.S. Defense Advanced Research Projects Administration (DARPA) announced on Wednesday that advanced software and equipment it developed to spot counterfeit microelectronics in U.S. weapons and cyber security systems has been handed over to military contractors to continue development. DARPA said the product of its Integrity and Reliability of Integrated Circuits (IRIS) program: the Advanced Scanning Optical Microscope (ASOM) technology was transferred to the Naval Surface Warfare Center (NSWC) in Crane, Indiana, where it will be used to inspect microelectronics for signs of tampering or compromise. The technology was developed with the help of SRI International, an IRIS contractor. Read more Security Ledger coverage of supply chain risks. “The ASOM technology housed at NSWC Crane will help engineers provide forensic analysis of microelectronics, including integrated circuits (IC) confiscated by law enforcement officials,” DARPA said in a statement. The DoD is a major buyer of integrated circuit chips, which are mainly manufactured outside the U.S. […]
Parsing Google’s Internet of Things Acquisitions
Google has gone on an acquisition tear in the last six weeks that has many tech industry watchers wondering about the company’s future direction – particularly when it comes to the Internet of Things. Since the beginning of the fourth quarter, 2013, Google has acquired 14 companies with the latest, a $650 million buy of UK-based artificial intelligence software firm DeepMind Technologies hitting the wires yesterday. In addition to the DeepMind buy, Google spent $40 million on Flutter, a maker of gesture recognition technology and $23 million on FlexyCore, maker of the DroidBooster App for Android. Earlier this month, it plunked $3.2 billion down for super hot smart home gear maker Nest. Google’s size makes the exact amount spent on the other acquisitions is something of a matter of speculation. Google only has to disclose transactions that are deemed ‘material’ to the company’s finances – a number somewhere between $10m […]