GigaOm has an interesting, high-level piece that looks at the issue of law, liability and the Internet of Things. The article takes off from a discussion at the Download event in New York City earlier this month, wondering whether adoption of Internet of Things technologies like wearables is starting to run far ahead of society’s ability to manage them. Specifically: is the pace of technology innovation outstripping the ability of our legal system to reign in excess and protect public safety and civil liberties? On the list of ‘what-if’s’ are some familiar questions: How to assign liability. (“If one of Google’s automated cars crashes, is it the fault of the driver or Google?”) Read more Security Ledger coverage of Internet of Things here. What responsibility to users have to take advantage of safety features in connected products? (Does a parent’s failure to password-protect a baby monitor change the manufacturer’s liability when and […]
home networking
AllSeen Alliance Announces Smart Lighting Framework
Smart lightbulbs aren’t anything new. In fact, products like the Philips Hue bulb have been in the market for years. The devices, which typically couple a standard incandescent or CF bulb with a wireless transmitter, allow lights to be managed via mobile device and also respond to environmental changes monitored by other sensors. But – as with much of the Internet of Things – each family of smart bulbs is something of an island: interacting- and communicating mostly with other smart home products from the same manufacturer. That’s good for the lightbulb maker, but bad for smart home advocates, see out-of-the box connectivity across product silos as a precursor to broad adoption of smart home technologies. It’s also been the case that the products that have been released have often fallen short in areas like security. In August, 2013, security researcher Nitesh Dhanjani disclosed a proof of concept hack […]
Unpatchable USB Malware Now Open Source | WIRED
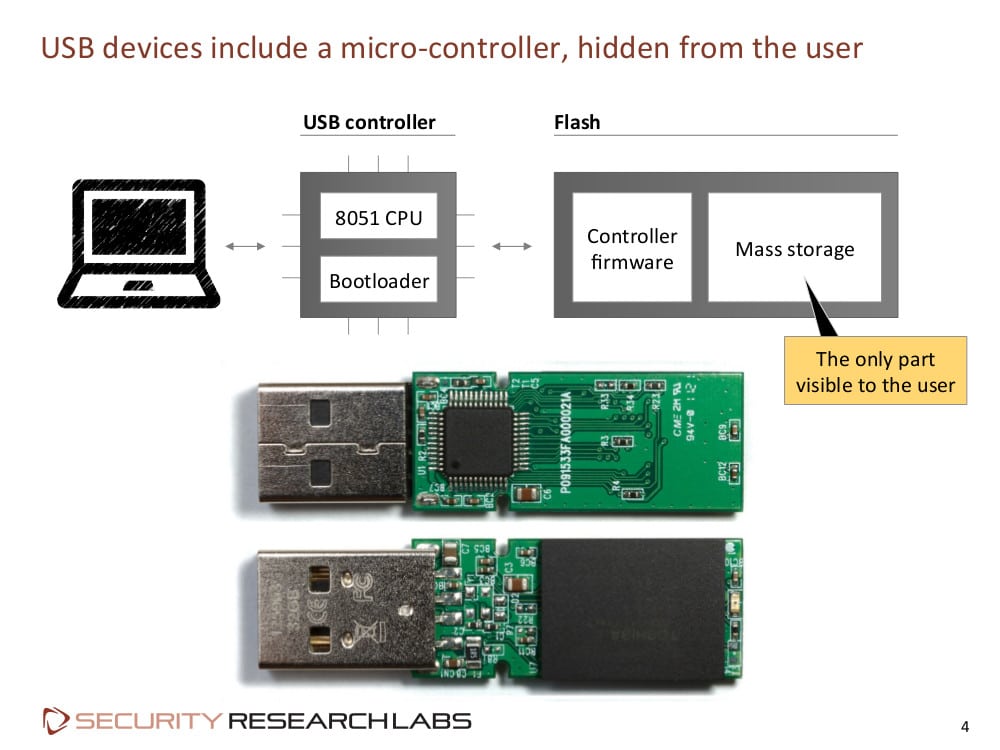
Andy Greenberg over at Wired has an interesting piece of news coming out of last week’s Derbycon hacker conference in Louisville, Kentucky. According to Greenberg and Wired, researchers Adam Caudill and Brandon Wilson showed off their own version of Karsten Nohl and Jakob Lell’s BadUSB malware, and that they’d released the code on Github. Their presentation raises the stakes for USB manufacturers to fix the BadUSB problem or leave hundreds of millions of users vulnerable, Greenberg writes. At a presentation at the Black Hat Briefings in August, Nohl and Lell, both of Security Research Labs (SRLabs), showed how the controller chips inside common USB devices can be reprogrammed, allowing USB peripherals to impersonate other kinds of devices. Among other things, Nohl demonstrated how a BadUSB infected device could emulate a USB keyboard, issuing commands to a connected machine using the permissions of the logged-in user. Alternatively, an infected USB could spoof a […]
3G Module Just 26mm Wide OK’d by AT&T| ITworld
Steve Lawson at IDG News Service has an interesting article that notes AT&T’s certification of the U-blox SARA-U260 model, which is dubbed “the world’s smallest 3G module.” The 16 x 26 millimeter device is seen as a harbinger of the kind of low power device that will greatly expand the Internet of Things. The SARA-U260 is designed to transmit small amounts of data over 3G networks and could enable a new generation of even smaller and smarter devices – from Smartmeters to wearable technology to connected cars. The U260 has features that support applications from voice calling to auto industry telematics to retail point-of-sale terminals and handheld devices, according to U-blox. It uses A-GPS (Assisted Global Positioning System) and a technology called CellLocate that uses nearby cellular towers to triangulate a location in situations where GPS isn’t available. 3G and 2G networks are being replaced by 4G and even 5G networks for most consumer smart phones. But the technology still works great […]
Concept Worm Could Spread Between Networked Attached Storage Systems
Kelly Jackson Higgins over at Dark Reading has a really interesting story about a researcher who is building a NAS worm. That’s right: some automated malware that will be capable of roaming the Internet finding and compromising consumer network attached storage (NAS) devices. Higgins interviewed Jacob Holcomb, a security analyst at the firm Independent Security Evaluators, has rolled more than two dozen previously unknown and undiscovered (‘zero day’) software vulnerabilities in NAS products into a proof-of-concept, self-replicating worm. According to Higgins, the worm scans for vulnerable services running on NAS systems — mostly web servers — and identifies the type of NAS device and whether it harbors the bugs. If a known, vulnerable platform is discovered, the worm launches the corresponding exploit from its quiver to take control of the device. Compromised devices are then used to scan for other, similar devices. Holcomb has already informed affected vendors – a list that includes […]