One of the challenges of talking about security in the context of Internet of Things is that the Internet of Things (IoT) isn’t a discrete technology, but an umbrella phrase that encompasses a lot of separate innovations: mobility, inexpensive sensors, wireless connectivity, Big Data and so on. One of the biggest moving parts in the IoT puzzle is cloud computing. Cloud infrastructure – whether its Amazon’s Elastic Compute Cloud (EC2) or Google or any of the thousands (millions?) of private cloud – is the back end for almost every IoT product. That presents both opportunities and real challenge for companies that are looking to leverage IoT in their workplace. Next week, I’m going to moderate a panel at an event here in Boston where we’ll tackle some of these issues head-on. The event: The Connected Cloud Summit is taking place in Boston on Thursday, September 18 at The State Room in downtown Boston. […]
Payment Card Industry
This Week In Security: Poking Holes In Two Factor Authentication
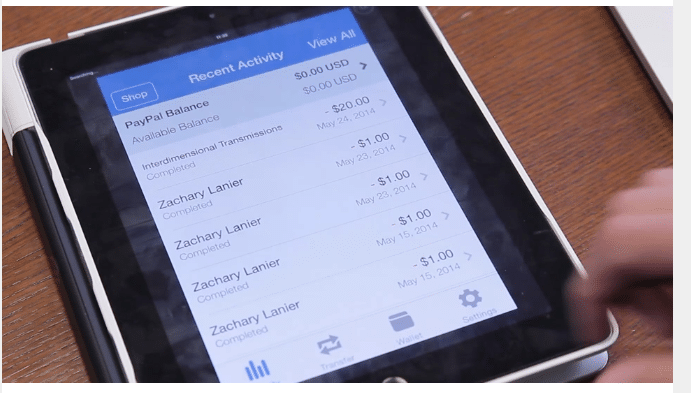
It was another busy week in the security world. There was big news on the legal front, as The U.S. Supreme Court took steps to protect the data stored on mobile devices from warrantless searches by police. (That’s good news.) But the week also plenty of concerning stories about the security of data stored on mobile phones, tablets and the like. One of the stories that gained a lot of attention was DUO Security’s report on a flaw in PayPal’s two factor authentication feature that could expose the accounts of security-conscious PayPal users. As The Security Ledger reported, DUO researcher Zach Lanier discovered a flaw in mobile APIs published by PayPal that would allow anyone with a valid PayPal user name and password to sidestep two-factor authentication when accessing PayPal accounts that had that option enabled. After DUO went public with information on the flaw, PayPal disabled two factor authentication […]
Researchers Sidestep Paypal Two-Factor Authentication
Researchers at DUO Security claim to have found a way of bypassing a two factor authentication feature that secures logins to Paypal.com, eBay’s online payment service. The vulnerability could allow an attacker who has stolen a Paypal customer’s user name and password to gain access to the account, even though the customer had enabled the more secure two-factor authentication option. DUO described the problem in a blog post early Wednesday. According to researcher Zach Lanier, Paypal has published an API (application program interface) for its Security Key two-factor authentication technology that contains a vulnerability that would allow even a non-technical hacker to bypass the second factor when accessing a Paypal customer’s account. An attacker only needs a victim’s PayPal username and password in order to access a two-factor protected account and send money. “The protection offered by the two-factor Security Key mechanism can be bypassed and essentially nullified,” the company wrote in […]
Wired Imagines Our Dystopian Connected Home Future
Over at Wired.com, the ever-provocative Matt Honan has a great little thought exercise on the “nightmare” that could come from connected home technology gone wrong. His piece, The Nightmare on Connected Home Street, is a first person narrative of a man who wakes up to discover he’s transformed into a cockroach inhabiting a virus infected home. “Technically it’s malware. But there’s no patch yet, and pretty much everyone’s got it. Homes up and down the block are lit up, even at this early hour. Thankfully this one is fairly benign. It sets off the alarm with music I blacklisted decades ago on Pandora. It takes a picture of me as I get out of the shower every morning and uploads it to Facebook. No big deal.” The story goes on to chronicle some of the other dystopian features of connected home malware – the hacked “Dropcam Total Home Immersion” account that […]
Video: The Internet of Things and Enterprise Risk
The Security Ledger recently hosted our inaugural event: The Security of Things Forum (SECOT). This was a high-energy, day long conference in Cambridge, Massachusetts, that brought together subject experts, executives and thought leaders from disparate areas like high tech, finance and industrial systems to talk about the tsunami of change that is the Internet of Things. One of the big questions hovering over the event: how will IoT technologies and services change the security paradigm that we’ve all be operating under- but especially in enterprises. In fact, IoT and enterprise was the topic of our very first discussion of the day: a panel chaired by Chris Rezendes of INEX Advisors, a leading consultancy focusing on IoT. SECoT Forum 2014 – Democratized Data, IOT and Enterprise Risk from Exhibitor Media Group on Vimeo It’s a really big and messy problem. As panelist Ken Pfeil of Pioneer Investments pointed out: the hack of […]