The hack of a Pennsylvania municipal water treatment facility in late November is part of a larger campaign by hackers affiliated the Iranian military against private and public sector organizations in critical sectors that include energy, food and beverage, manufacturing and healthcare, according to a U.S. Federal Bureau of Investigation (FBI) warning, issued a warning on Friday.
The FBI, joined CISA, the NSA, the EPA and Israel’s National Cyber Directorate (INCD) in issuing a joint Cybersecurity Advisory (CSA) to highlight what it described as “continued malicious cyber activity” by Iran’s Government Islamic Revolutionary Guard Corps (IRGC)-affiliated Advanced Persistent Threat (APT) cyber actors.
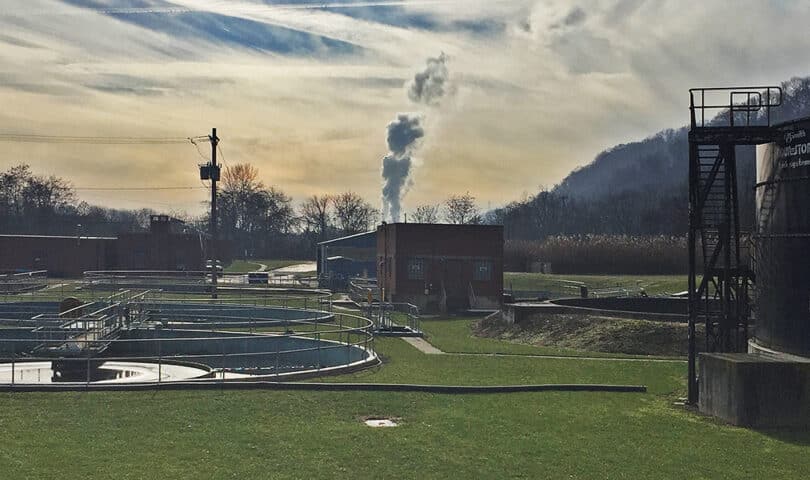
An attack in Aliquippa
The announcement followed an attack in November on a water treatment facility in the town of Aliquippa, Pennsylvania, outside Pittsburgh. That attack forced the utility to switch over to manual operations. Cyber Av3ngers, a hacking group with links to Iran, claimed responsibility for the attack and has been linked to attacks on water systems in Israel, according to a report in the Pittsburgh Post-Gazette.
The broader malicious campaign isn’t limited to water facilities, however. Attackers are targeting and compromising operational technology (OT) devices manufactured by Israel-made Unitronics Vision Series programmable logic controllers (PLCs). Those PLCs are used in the Water and Wastewater Systems (WWS) Sector and industries like energy, food and beverage manufacturing, and healthcare, according to the alert. Also: the PLCs may be ‘white labeled’ and appear as branded products by different manufacturers and companies.

Programmable Logic Controllers (PLCs) are type of industrial computer that are used to control manufacturing processes that require high reliability, such as on assembly lines, controlling robotic devices or industrial equipment. In the wastewater sector, PLCs are used to control and monitor the stages and processes of water and wastewater treatment: turning pumps on and off at a pump station, filling tanks and reservoirs, flow pacing chemicals to meet regulations, and gathering compliance data for monthly regulation reports, as well as monitoring for faults and triggering alarms, according to the CISA Alert.
Since November, the IRGC-affiliated hackers have exploited default credentials in Unitronics devices in multiple US states, leaving a defacement image that reads: “You have been hacked, down with Israel. Every equipment ‘made in Israel’ is CyberAv3ngers legal target.”
Behind attacks: poor password security
The Cyber Av3ngers threat actors likely hacked the Unitronics Vision Series PLC via the device’s Human Machine Interface (HMI), possibly by exploiting poor password security on a device that was exposed to the public Internet.
CISA guidance to Unitronics customers includes changing the default Unitronics password, “1111” to something secure, employing multi-factor authentication on the device and making sure it is not accessible from the public Internet and changing the default TCP port used to access the device.
Geopolitics ratchets up cyber risks
Dawn Cappelli, the head of the OT CERT at the OT cyber firm Dragos said the attacks on Israel-made operational technology underscore the ways the tense geopolitical environment is intensifying cyber threats.
In the case of the hack of the Aliquippa Municipal Water Authority, the community was fortunate in that the affected PLC was disabled and the Water Authority was able to fall back to manual operations, greatly limiting the impact of the attack on the Aliquippa community. However, a ransomware attack that affected multiple systems may not have been as easy to recover from, Cappelli said. In the first half of 2023, Dragos observed an average of 2.6 ransomware attacks that impacted industrial organizations each day, a more than 50% increase from 2022.
“You don’t read about it. Small organizations don’t want it to make the news,” she said.
The FBI and other agencies advice organizations using the Israeli-made PLCs apply the recommended mitigations to avoid compromise. But Cappelli of Dragos notes that small, local utilities often lack the staff and expertise to address cyber risks.
“At a lot of small utilities, their budget is for replacing pipes that are crumbling – that’s a much bigger threat than cyber,” she said.

Pingback: Citing Attacks On Small Utilities, Dragos Launches Community Defense Program - The Security Ledger with Paul F. Roberts
Pingback: Dragos Community Defense Program Helps Small Utilities Facing Cyber Attacks – Raymond Tec