The agricultural equipment industry has long considered itself immune from cyber attacks. After all: farm equipment wasn’t Internet-connected and the software and protocols that it used were obscure. Besides: farms- and farm equipment held little in the way of sensitive personal or financial data that cybercriminals could easily monetize.
But a lot has changed in the agriculture sector in the last decade. And farm country’s cybersecurity bill has come due…in a big way. A presentation at the annual DEF CON hacking conference in Las Vegas, scheduled for Sunday, will describe a host of serious, remotely exploitable holes in software and services by U.S. agricultural equipment giants John Deere and Case-IH. Together, the security flaws and misconfigurations could have given nation-state hackers access to- and control over Deere’s global product infrastructure, access to sensitive customer and third party data and, potentially, the ability to remotely access critical farm equipment like planters and harvesters that are the lynchpin of the U.S. food chain.
Opinion: my Grandfather’s John Deere would support our Right to Repair
A video of the presentation, “The Agricultural Data Arms Race Exploiting a Tractor Load of Vulns,” was posted on YouTube by conference organizers on Thursday. It is the most detailed presentation, to date, of a range of flaws in Deere software and services that were first identified and disclosed to the company in April. The disclosure of two of those flaws in the company’s public-facing web applications set off a scramble by Deere and other agricultural equipment makers to patch the flaws, unveil a bug bounty program and to hire cyber security and embedded device security talent.
Sick Codes (@SickCodes), an independent security researcher who declines to use his real name in public statements, worked with researchers from the group Sakura Samurai including wabaf3t; D0rkerDevil; ChiefCoolArrow; John Jackson; Robert Willis; and Higinio “w0rmer” Ochoa. Together, the group uncovered 11 other flaws in Deere software and applications and that the group shared with the company as well as CISA, the Cybersecurity and Infrastructure Security Agency.
You Had Me at “Log In.”
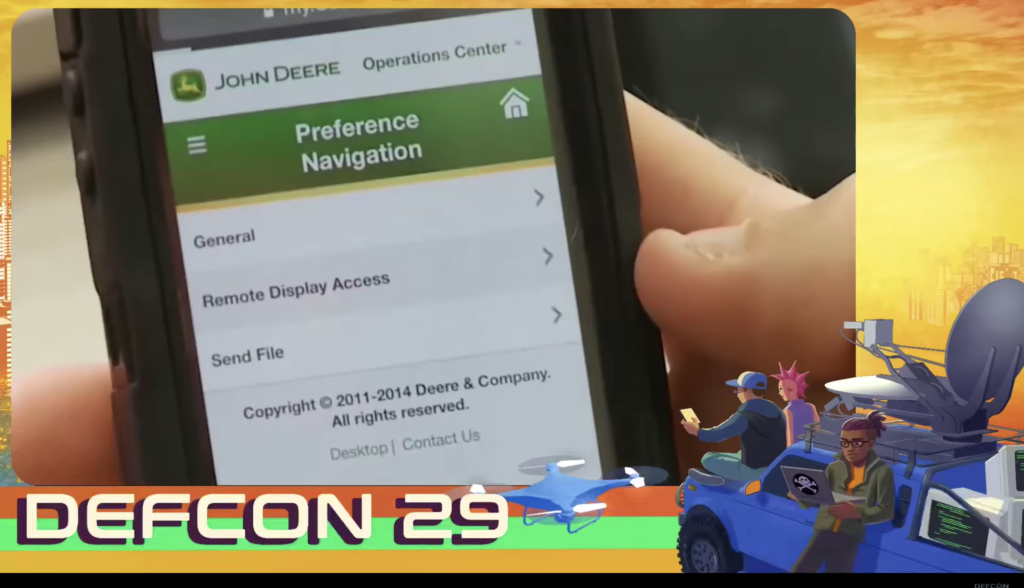
The presentation at DEF CON is the first time that details of those flaws have been publicly disclosed. In it, Sick Codes describes a range of flaws in software owned by Deere and third party platforms that the Moline, Illinois company relies on. He discovered the flaws after registering a developer account with John Deere and beginning to explore the company’s development, quality assurance and supplier networks, including JDConnect and the John Deere Operations Center, which allows company support technicians and dealerships to remotely connect to and control equipment in the field.
Episode 216: Signed, Sealed and Delivered: The Future of Supply Chain Security
For example, Sick Codes said that he discovered a DOM (document object model) cross site scripting (or XSS) flaw almost immediately after logging into Deere’s developer site. DOM-based cross site scripting attacks allow the attacker to make malicious modifications to how a vulnerable website runs by altering client side code contained in the page.
“Really Basic Stuff” Left Undone
Cross site scripting flaws are common on the web and “a really basic vuln(erability),” Sick Codes notes. However, the fact that one was found “on a major part of (Deere’s) website” suggests the company is not taking web security seriously, he said.
Further exploration revealed more serious security flaws in Deere’s public-facing website. For example, poor segmentation allowed Sick Codes and others to access areas of the site that should have been off limits to a user with a simple developer account, including areas dedicated to Deere suppliers and quality assurance. Sick Codes and his collaborators also found they could use features of Deere’s site to uncover the names of other active accounts on the site. Basic web application security practices should prevent any user from “enumerating” other accounts like that. Also: a feature for searching by purchase order number on an area of Deere’s site for suppliers spit out verbose error messages that revealed details about the type and structure of Deere’s back end database (IBM DB2) that could enable further attacks.
Deere John: Researcher Warns Ag Giant’s Site Provides a Map to Customers, Equipment
The attackers were further able to access Deere’s Machine Book, an area of the website used to reserve demonstration units of Deere equipment. Another cross site scripting flaw in the Machine Book interface allowed a malicious actor to book, cancel or reassign demo equipment. Sick Codes was also able to inject code into the Machine Book database and extract Deere data on “every demo unit ever provided” and the John Deere email address used to reserve the units.
Key to the Kingdom
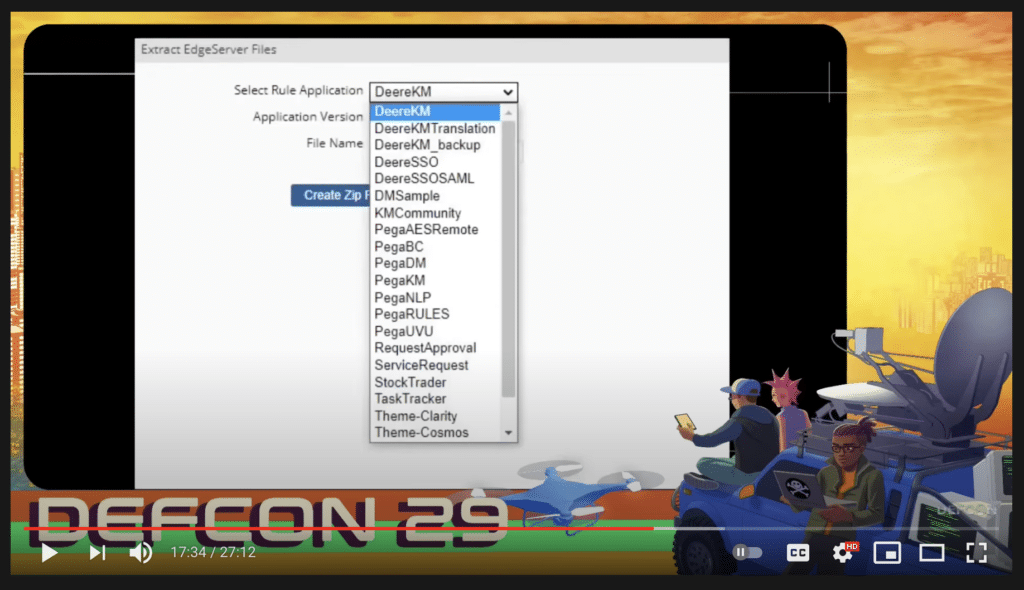
Even more concerning was the discovery of a vulnerability (CVE-2021-27653) in third party software by Pega Systems, a maker of customer relationship management (CRM) software that Deere uses. A misconfiguration of that software gave the researchers administrative access to the remote, back end Pegasystems server.
“So that’s what we did,” he said. That flaw gave them wide ranging, administrative access to the production backend server, which yielded other, administrative Pegasystems credentials including passwords, security audit logs, as well as John Deere’s Okta signing certificate for the Pegasystems server. With that, the attackers would have unfettered access to Deere’s infrastructure, including its Operations Center, he said.
Container ships easy to hack, track, send off course and even sink, security experts say
In an email statement to The Security Ledger, a John Deere spokesperson said that “none of the claims – including those identified at DEF CON — have enabled access to customer accounts, agronomic data, dealer accounts, or sensitive personal information.” Furthermore, “contrary to claims made at DEF CON, none of the issues identified by the security researchers would have affected machines in use,” the statement read.
“John Deere considers the security of our systems and the data within them a top priority and we work tirelessly to identify and address any misconfigurations as quickly as possible,” Deere’s statement reads. “Deere also recognizes the important role our products play in food security and within the global food supply chain.”
Sick Codes said the statement amounted to “gaslighting” about the severity of the discoveries. “We were root,” he said, describing the level of access he and other researchers had to the Pega Systems server and other assets. While he and other researchers did not attempt to manipulate deployed Deere hardware, details from his previous disclosures, the DEF CON presentation and information shared with Security Ledger suggest that data on employees, dealers and customers – including email addresses, usernames and passwords of Deere employees and third parties (like PegaSystems)-was exposed as a result of the discovered flaws. Determined cyber adversaries may well have been able to leverage such access to obtain even greater control over Deere’s environment and deployed equipment.
Deere wasn’t the only agricultural equipment maker the researchers targeted. The group also interrogated public-facing infrastructure operated by Case-IH. Among other discoveries, Sick Codes and his partners were able to access a Javamelody application monitoring server operated by Case. Through that they were able to access data that exposed Case-IH customers in Brazil including their username, first and last name, IP address, session ID and so on, which could allow them to log into the Case-IH application as the user.
Nobody Home
Neither manufacturer was initially prepared to receive reports about software security flaws in their products, according to Sick Codes and the other researchers who worked with him. Specifically: Deere did not respond to initial efforts by the researchers to relay their findings to Deere’s security team. Eventually (and with help from this reporter), the researchers made contact with officials at the Cybersecurity and Infrastructure Security Agency (CISA), who facilitated a conversation with Deere staff. (CISA declined to comment for this story.)
Deere said it has information security professionals on staff. After Sick Codes initially reported his findings, the company also established a bug bounty program through the firm HackerOne.”Our participation in this program will help us leverage the ethical hacking community to identify system improvements and bolster information security,” Deere said.
Case IH, also, was unresponsive to multiple efforts to report the vulnerabilities. Researchers eventually used the company’s compliance and governance portal to connect to Case through a third party “compliance hotline” portal provided by Navex Global, Sick Codes said.
Case IH did not respond to a request for comment.
Ingredients of a crippling attack
Taken together, the vulnerabilities discovered by the researchers suggest that major agricultural equipment makers have lax cyber security practices for public facing websites and applications. That, even as they have moved aggressively in the last decade to connect platforms to equipment and other hardware used by their customers.
The combination of remote access and control and lax application- and data security on platforms like Deere’s Operations Center or Case IH’s AFS Connect could be devastating for U.S. agriculture and the global food supply chain, should sophisticated cyber criminal or nation state adversaries take an interest in these platforms, experts say.
For one thing, agricultural production has become concentrated in a few hands – a risk the recent ransomware attack on meat processor JBS exposed. USDA data shows rapid consolidation in agriculture in the last thirty years, much of it driven by the advent of “precision agriculture,” which has facilitated “economies of scale” in areas like crop management and livestock. “In recent years, the technologies encompassed by precision agriculture — GPS-assisted vehicle guidance systems, yield and soil mapping, and variable-rate applications of inputs—appear to have spurred further increases in farm size,” the USDA noted in a 2018 report (PDF). Other studies have found that the equipment supporting precision agriculture carries substantial fixed costs and is far more likely to be adopted on larger farms, encouraging consolidation.
Kevin Kenney (@GrassrootsKK), a fuel systems engineer and vocal critic of technology-based restrictions for farmers in agricultural equipment said that the growth in cloud based agriculture platforms like John Deere’s Operations Center has been rapid and that such systems now constitute a single point of failure for the agricultural sector.
An adversary with access to and control over Deere’s Operations Center would have access to years of granular, “forensic” information on farmers’ activities and the output of thousands of US farms. If compromised, such a platform could also give those countries the ability to remotely cripple critical planting and harvest equipment at critical junctures – potentially imperiling food production across the US, he said.
Sick Codes’ DEF CON presentation is an embarrassment to Deere and Case IH- the equivalent of getting “pants-ed on the playground,” Kenney said. Still, he doubted that it would prompt any real change in the companies’ behavior – at least in the short term. And given their influence and reach in the agriculture industry, the security flaws won’t necessarily lead to improved security for farmers, their equipment or their data. “Farmers won’t even know this happened,” he said.







Pingback: Flaws in John Deere Systems Show Agriculture's Cyber Risk - F1TYM1
Pingback: Exclusive: DEF CON: Security Holes In Deere, Case IH Shine Spotlight On Agriculture Cyber Risk – Last Bulletin
Pingback: DEF CON: Security Holes In Deere, Case IH Shine Spotlight On Agriculture Cyber Risk - F1TYM1
Pingback: DEF CON: Security Holes In Deere, Case IH Shine Spotlight On Agriculture Cyber Risk - Slashdot
Pingback: Connected Farms Easy Pickings for Global Food Supply-Chain Hack - JAIALA Small Business Insurance Santa Clarita CA
Pingback: Connected Farms Easy Pickings for Global Food Supply-Chain Hack | Threatpost
Pingback: Updates 2021-09-14 - SaferPC