Consumer Reports warns that smart TVs by Samsung and other vendors are vulnerable to disorienting remote attacks.
There have been countless reports of vulnerabilities in smart television sets in recent years. Now Consumer Reports, the consumer product review magazine, has warned that millions of smart TVs sold under the Roku and Samsung brands are vulnerable to remote attacks.
In a report on Wednesday, Consumer Reports warned that the problems affect smart TVs by Samsung, TCL and other brands that use the Roku TV smart-television platform. Video streaming devices such as the Roku Ultra were also vulnerable, Consumer Reports found.
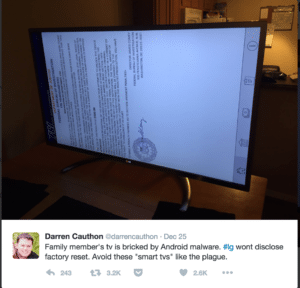
“We found that a relatively unsophisticated hacker could change channels, play offensive content, or crank up the volume, which might be deeply unsettling to someone who didn’t understand what was happening,” Consumer Reports researchers found.
Attacks could be launched remotely via the web. However, the vulnerabilities would not allow a hacker to spy on the user or steal information.
This is the first time Consumer Reports has reported on the cyber security of smart televisions. The firm used a newly launched standard, dubbed the Digital Standard (PDF) that assesses the security of devices using a number of measures, including how the software was written, whether the product encrypts data, secure configuration standards (including password security) and even whether the manufacturer offers a bug bounty program to encourage independent assessments of its technology.
The findings were part of a broad privacy and security evaluation, led by Consumer Reports, of smart TVs from LG, Sony, Vizio and other brands. The TCL vulnerability, for example, applies to devices running the Roku TV platform. That includes sets by manufacturers like Hisense, Hitachi, Insignia, Philips, RCA, and Sharp and some of Roku’s own streaming media players, such as the Ultra.
Researchers pinpointed the problem in an application programming interface (API), which was unsecured and enabled by default on affected sets, permitting even trivial hacks. Attackers would need to work from within the same network the TV was connected to. Also: users would need to download a malicious application to give attackers control over the device.
For Samsung smart TVs, researchers found that a feature designed to limit activity to only authorized third party mobile applications on the set was flawed, allowing anyone to place malicious code on the device.
Finally, researchers found more evidence that smart set makers were harvesting detailed information on their customers. And, while features to limit data collection were available, they came with a heavy price tag: sacrificing many of the TV’s smart features.
In recent years, smart TV makers have been forced to withdraw or reconsidered features that allowed smart sets to monitor and track customers viewing habits, or that surreptitiously monitored their conversations in the name of “voice activated commands.”
In 2015, for example, Samsung faced criticism following reports that its TVs are capable of eavesdropping on the conversations that happen around them. According to Samsung’s terms of service for some smart TV models, that the information may be “captured and transmitted to a third party” through voice recognition features built into the set. Nearly identical language also exists in a terms of service agreement for users of LG’s smart TVs.
In 2017 smart TV maker VIZIO agreed to pay $2.2 million to the FTC and the State of New Jersey to settle charges that it collected the viewing history of some 11 million smart televisions without users’ consent. The settlement stems from a 2014 case and requires the company to “prominently disclose and obtain affirmative express consent” for data collection and sharing.

Pingback: Report: Android Monero-Mining Malware Bricks Your Smartphone | The Security Ledger
Pingback: Next privacy trap for consumers? Their cars. | The Security Ledger