In-brief: Managed DNS firm Dyn, a victim of the Mirai botnet, got its revenge: taking part in a coordinated takedown of WireX, a botnet of compromised Android devices, according to an announcement Monday.
A group of security firms, including Dyn – a victim of the Mirai botnet – joined forces to take down WireX, a new botnet built on compromised Android mobile devices, the firms disclosed on Monday.
The joint operation involved researchers from content distribution network (CDN) firms Akamai and Cloudflare as well as Google, Dyn (now part of Oracle) and the firms Flashpoint, Team Cymru and RiskIQ following attacks on August 17 that attracted the attention of the firms.
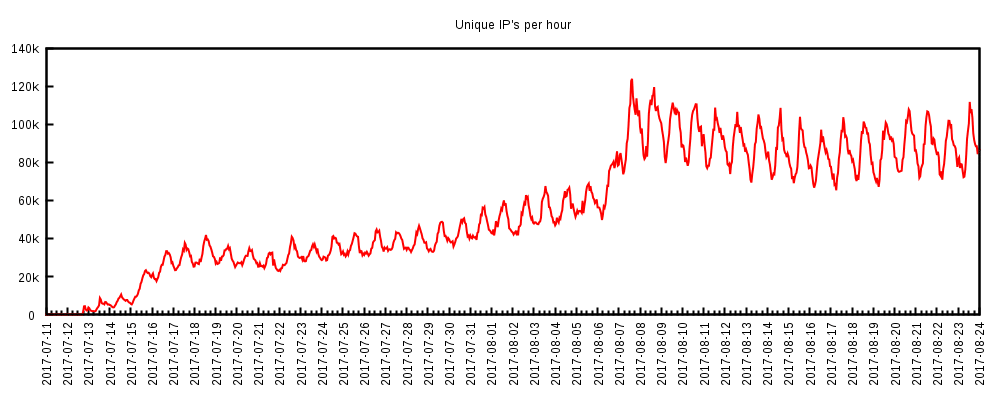
The action follows a decision by Google to remove some 300 suspicious applications from its Google Play store after they were linked to a wave of denial of service attacks in August. Analysis of so-called “User-Agent” strings in those attacks emanated from a global network of some 70,000 IP addresses, many of them Android devices, according to the statement.
Behind the attack: a range of free applications from Google Play with names like “Lucky Patcher Booster” (which promises to boost your phone’s performance) and Tube Player (a YouTube knock off). DDoS attacks were launched in the background, while the application was being used or while the phone was idle.
From a joint statement released by the firms involved in the takedown:
Many of the identified applications fell into the categories of media/video players, ringtones or tools such as storage managers and app stores with additional hidden features that were not readily apparent to the end users that were infected…The applications that housed these attack functions, while malicious, appeared to be benign to the users who had installed them. These applications also took advantage of features of the Android service architecture allowing applications to use system resources, even while in the background, and are thus able to launch attacks when the application is not in use.
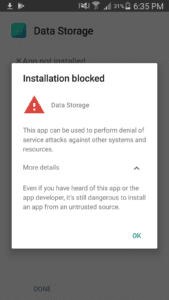
Google has since blocked the mobile applications from running on Android devices, and removed it from devices on which it had already been installed.
Among the participating organizations: Dyn, the managed domain name system (DNS) provider that was hobbled by the Mirai botnet in October, 2016. Despite suffering a loss of business as a result of the attack, Dyn was subsequently acquired by enterprise software giant Oracle Corp.
The security marketplace is crowded and competitive. But there have also been plenty of occasions on which competitors for the attentions of CEOs and CIOs have lain down their marketing brochures and joined forces to battle Internet bad guys. In the past, tech firms such as Symantec and Microsoft have cooperated with law enforcement to kneecap botnets like Avalanche, Kelihos, Simda.
Source: The WireX Botnet: An example of cross-organizational cooperation – The Akamai Blog