In-brief: After seeding the globe with hackable DVRs and webcams, Zhejiang Dahua Technology Co., Ltd. of Hangzhou, China will be working with the U.S. firm Synopsys to “enhance the security of its Internet of Things (IoT) devices and solutions.”
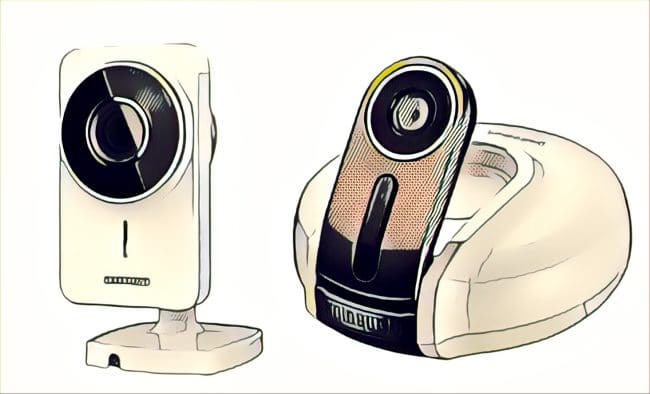
The surveillance camera maker whose name became synonymous with insecure, connected devices after its cameras formed the backbone of the Mirai botnet has hired a top secure software development and testing firm to makes its products less prone to hacking.
Zhejiang Dahua Technology Co., Ltd. of Hangzhou, China will be working with the U.S. firm Synopsys to “enhance the security of its Internet of Things (IoT) devices and solutions.” In a joint statement, the companies said Dahua will be adopting secure “software development life cycle (SDLC) and supply chain” practices using Synopsys technologies in an effort to reduce the number of “vulnerabilities that can jeopardize our products,” according to a statement attributed to Fu Liquan, Dahua’s Chairman.
Dahua’s cameras and digital video recorders (DVRs) figured prominently in the Mirai botnet, which launched massive denial of service attacks against websites in Europe and the U.S., including the French web hosting firm OVH, security news site Krebsonsecurity.com and the New Hampshire based managed DNS provider Dyn. Cybercriminals behind the botnet apparently exploited an overflow vulnerability in the web interface for cameras and DVRs to gain access to the underlying Linux operating system and install the Mirai software, according to research by the firm Level3.
In March, Dahua was called out for another, serious vulnerability in eleven models of video recorders and IP cameras. Namely: a back door account that gave remote attackers full control of vulnerable devices without the need to authenticate to the device. The flaw was first disclosed on the Full Disclosure mailing list and described as “like a damn Hollywood hack, click on one button and you are in.”
Reports at the time suggested that the impact of the flaw affects more than the 11 Dahua devices that the company has identified. In a letter to customers, the company said that it is conducting “exhaustive tests” and developing “a series of firmware patches” to address the security hole.
Synopsys provides products and services for connected product makers. Its Software Integrity Platform does automated analysis and testing as part of the software development process, spotting security vulnerabilities design defects and compliance issues during the software development life cycle, as well as what Synposys calls “security assurance and visibility into (the) software supply chain.”
Lax coding practices by device makers and their suppliers is an endemic problem on the Internet of Things, where core components like embedded operating systems, web servers and other hardware and software components might be used by hundreds thousands of different devices made and sold by hundreds of different vendors. For example, previous botnets of DVRs and webcams have been linked to vulnerabilities in commonly consumed components like the Cross Web Server by TVT, a China based firm.