In-brief: Cisco Systems has patched a serious security hole in its Prime Home, a network management tool that it markets as a way for service providers to manage “Internet of Things” devices in connected (“smart”) homes.
Cisco Systems has patched a serious security hole in its Prime Home, a network management tool that it markets as a way for service providers to manage “Internet of Things” devices in connected (“smart”) homes.
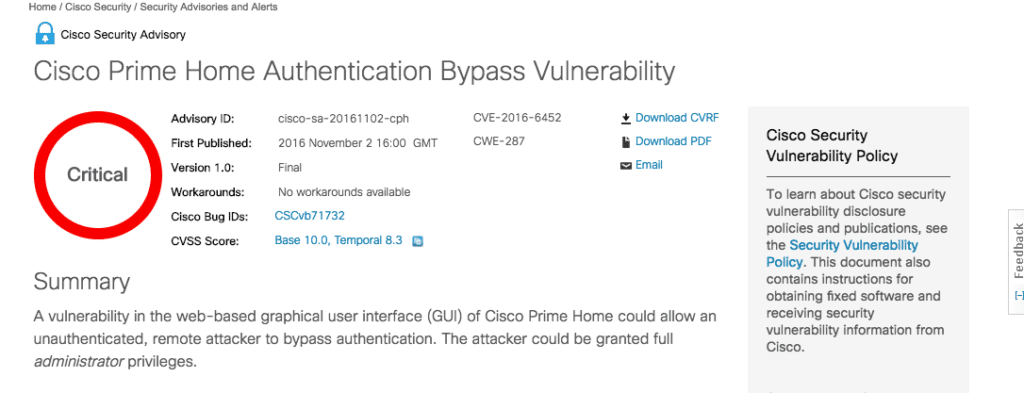
The company on Wednesday issued an alert warning of a flaw affecting the web-based graphical interface (GUI) of Cisco Prime Home. An attacker who knew the right web address to enter into her browser could use the flaw to circumvent the user authentication feature of the product, gaining administrative access to the product without a valid user name and password.
Cisco said it released a software update that addresses the vulnerability, but that no mitigations “workarounds” are available – short of patching. The flaw affects Cisco Prime Home versions 5.1.1.6 and earlier and version 5.2.2.2 and earlier. Cisco Prime Home versions 6.0 and later are not vulnerable.
The flaw could be troublesome for Cisco customers, including Internet Service Providers that use Cisco Prime Home to provide visibility into and manage home networks. Prime Home is marketed for its ability to provide “deep operational visibility into a variety of devices in the home and the network behind them.”

Prime Home allows ISPs to directly manage connected home appliances like (Cisco) residential gateways, IP phones, set-top boxes, network attached storage and other devices. The device allows “zero-touch provisioning, remote configuration and configuration updates, software (including firmware) upgrades, monitoring, real-time problem diagnosis. Service providers can use it to troubleshoot of common home networking problems, such as a loss of wireless connectivity.” Bulk operations help “automate the mass management of home devices and help service providers lower the cost of deploying and maintaining large numbers of subscriber devices.”
This is just the latest authentication bypass vulnerability to make news. A report by the security firm Flashpoint identified a similar authentication bypass vulnerability in a web interface developed by the Chinese firm Xiongmai that used to manage closed circuit TV cameras, digital video recorders and other devices that used Xiongmai’s hardware. That flaw, and the use of a hard-coded administrator account, allowed attackers to take control of more than 100,000 cameras and other devices and infect them with the Mirai software, which was then used to launch denial of service attacks against the managed domain name system (DNS) provider Dyn and other sites.
The impact at least of the Cisco Prime appears to be small. A search of the Internet shows fewer than 100 of these devices publicly exposed. Many more are (likely) deployed, but protected behind firewalls and not easily discoverable. Unclear from the alert, however, is if the flaw is in a common component that is used by Home Prime, it may have impact well beyond that specific platform.







Pingback: 10Fold- Security Never Sleeps- 117 - 10Fold Communications