In-brief: A report by The Munk Center finds attackers believed to be affiliated with China are shifting tactics as Tibetans and the Tibetan Government in Exile rely more on the cloud to communicate.
Sophisticated hackers believed to be working for the government of China have switched up their methods for trying to hack the Tibetan community in response to more awareness about malicious email attachments.
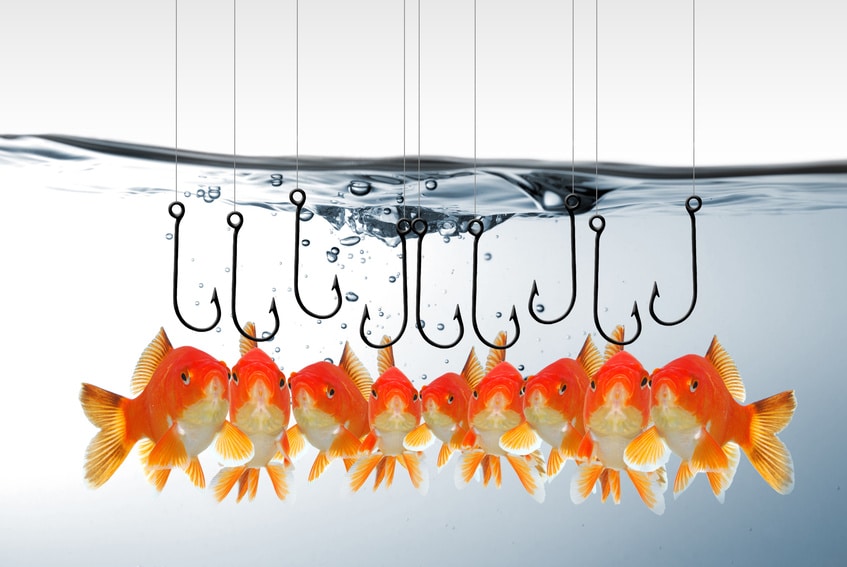
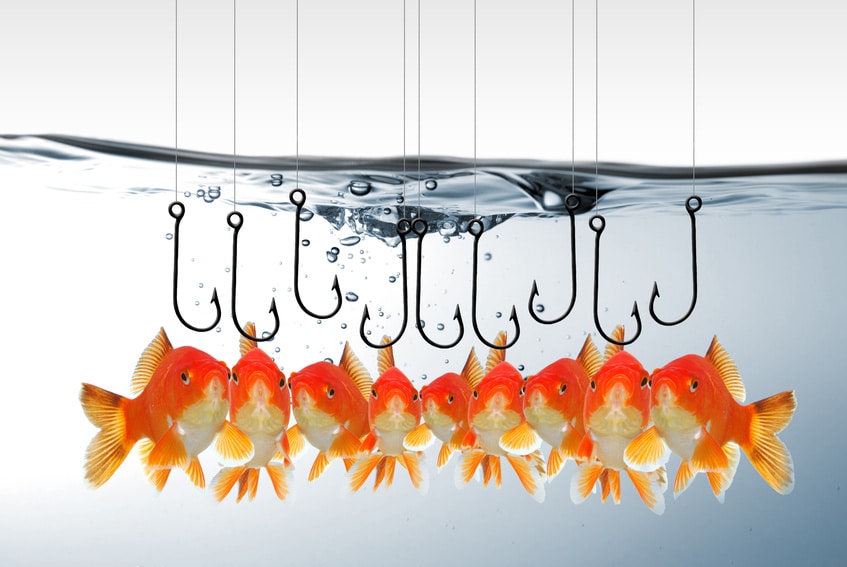
Phishing attacks aimed at harvesting credentials to cloud based resources are now the method of choice for attacking Tibetan activists, according to a post over at Citizen Lab, part of The Munk School of Global Affairs at University of Toronto.
Researchers at The Munk School, working with researchers at Palo Alto Networks, have been tracking the doings of a hacking crew, dubbed Scarlet Mimic, that is believed to be working on behalf of Chinese authorities.
Targeted attacks against Tibetans and the Tibetan Government in Exile go back more than a decade. In recent years, however, Tibetans have become more savvy about these APT-style campaigns. Malware embedded in documents and other email attachments accounted for 95 percent of attacks against six, separate Tibetan groups that the Munk School studied.
In response, the Tibetan community has responded with a digital security training campaign called “Detach from Attachments”, which “urges users to avoid sending or opening email attachments, and to use cloud-based storage (e.g., Google Drive) to send files instead.”
As the community changed its behaviors, attackers simply adapted, the researchers say.
Specifically: attackers are using targeted (“spear”) phishing email messages to members of the Tibetan community containing what appear to be share links to documents or videos hosted on Google Drive or video sharing websites. The messages contain subjects like “How CHINA takes care of Tibet and Tibetans – video” and other topics.
When the targets go to view the document, the attackers harvest their credentials.
Though the front end of these attacks are new, The Munk center notes that, under the hood, they are almost identical to attacks against the Tibetan community that have been observed for close to a decade. Often, the same command and control infrastructure used in previous attacks is leveraged in the newer, phishing campaigns, the report said.
What’s the goal? The Munk Center theorizes that phishing campaigns are trying to infiltrate social networks used by Tibetans and the Tibetan Government in Exile by targeting organizations and individuals in the Tibetan community that act as distributed networks, with staff members and collaborators around the world.
“Credential phishing is a potentially more efficient means of gaining access to these networks than document-based malware,” the report finds.