In-brief: Revelations last week of hacks that exposed information on FBI and DHS employees underscore the massive challenges that the federal sector face in securing sensitive information.
There’s a famous and hilarious scene in the 1981 film Stripes in which Bill Murray and co-star Harold Ramis go to an Army recruitment office to enlist. Asked to sign his enlistment papers, Murray instead writes the government a get-well card. “Dear Sammy, feel better soon!” Then signs his name.
That scene came to mind for me last week upon learning of a new round of attacks on federal agencies that have spilled data on tens of thousands of federal employees, including the Federal Bureau of Investigation and the Department of Homeland Security. As The Security Ledger reported this week, news of the incident comes by way of Motherboard reporter Joseph Cox who received leaked employee data provided by an unidentified hacker. The data, part of more than 200 Gigabytes, includes email addresses and phone numbers of over 20,000 Federal Bureau of Investigation (FBI) employees and more than 9,000 Department of Homeland Security (DHS) employees.
Data on the FBI employees has since been released by the hacker, who uses the Twitter handle @dotgovs. According to Cox and Motherboard, the attack followed the compromise of a personal computer and credentials and email account of a DOJ employee. The culprit: a politically motivated hacktivist apparently animated by U.S. policy towards the Palestinians and Israel. (But, of course, attribution is hard, so who knows what the real motivation was?)
After compromising the system, the hacker then posed as a new DOJ employee and convinced a DOJ support worker to give him (or her?) a unique code needed to remotely access the employee’s computer via a DOJ web portal. From that portal, the hacker was offered access to a variety of systems and connected to the system of the employee whose identity he stole, access files, email and other data on the employee’s system, including the lists of employees.
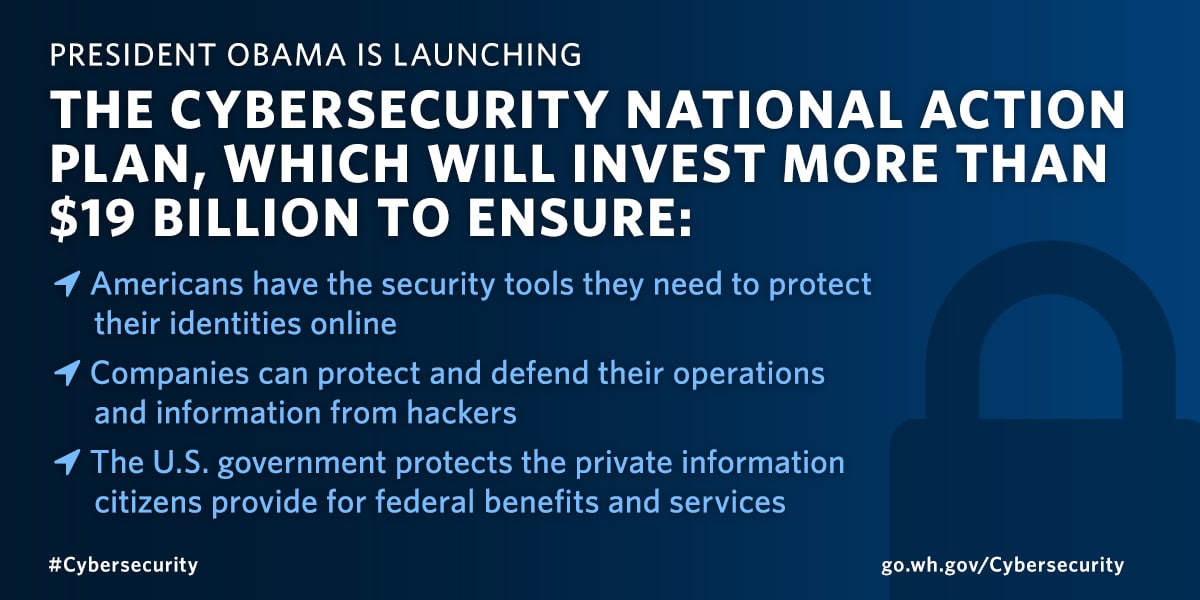
The report came just days ahead of the release of President Obama’s Fiscal Year 2017 budget, which proposes a 35% increase in funding for cyber security and a major push to improve the security posture of government systems. “It is no secret that too often government IT is like an Atari game in an Xbox world,” the President wrote, in an op-ed in the Wall Street Journal.
Atari, indeed. But the recent hacks of DOJ and DHS suggest that the challenges facing federal information systems and networks are far greater than just outdated software and hardware. President Obama called for investment in so-called “multi factor” authentication that combines a password and user name with another piece of identifying information.
But the ease with which DOJ support staff were socially engineered by the hacker to provide that critical, additional information to a hacker posing as an employee underscores the huge training and awareness issues that massive, bureaucratic organizations like the DOJ will have to undertake in order to realize the benefits from stronger authentication. That’s difficult – especially with a distributed workforce where technical skills and awareness trail the private sector.
Just as worrying: the ability of the attacker to obtain sensitive information on tens of thousands of federal employees by compromising the account of a single Department of Justice staffer. The fact that information on thousands of employees lay at the fingertips of a single DOJ employee suggests that much more work needs to be done in the federal government to identify sensitive information, discover where it resides on federal IT systems and then devise a way of isolating and securing that information.
Finally, the ability of the attacker to export the sensitive data from federal government systems exposes a worrying lack of visibility and control over employee activity. Gaining access to federal employee systems is bad enough. But allowing wholesale data theft with little more than a foothold on federal networks sets a very low bar for would-be attackers to clear.
Like most other proposals in Washington D.C., the Obama Administration’s budget is widely believed to be “dead on arrival.” That would be unfortunate, given the encouraging and needed investments it makes in information security.
The need is acute. Reports from government watchdogs have long warned about dysfunction in federal agencies when it comes to acquiring and maintaining information systems. In a 2013 report, for example, the Government Accountability Office noted that Uncle Sam has made negligible progress towards improving the security of its information systems, and has little to show in key areas such as responding to cyber incidents, promoting R&D on cyber security tools and technology and educating its workforce about cyber security, or responding to international cyber threats. In short, Uncle Sam needs a plan, GAO found.
Still, as the attacks on the DOJ and DHS, not to mention the massive breach at the Office of Personnel Management suggest, merely increasing the budget for information security isn’t likely to address the underlying operational and human resources challenges that, together, often contribute to adverse incidents. Feel better soon, Sammy!
