In-brief: Healthcare organizations are woefully prepared to defend against cyber attacks that could affect patient health due, in part, to a narrow focus on protecting patient health information.
A survey of a dozen healthcare organizations across the United States found that they are ill prepared to fend off cyber attacks aimed at disrupting services or compromising patient health, despite – or possibly because of – an intense focus on protecting patient privacy.
Hospitals and other healthcare organizations pour resources into protecting patient health records, but are ill prepared to defend their facilities, networks, employees and infrastructure against targeted attacks by online adversaries who wish to cause disruptions in service or even to target patients, according to the report (PDF) issued by Independent Security Evaluators (ISE) on Wednesday.
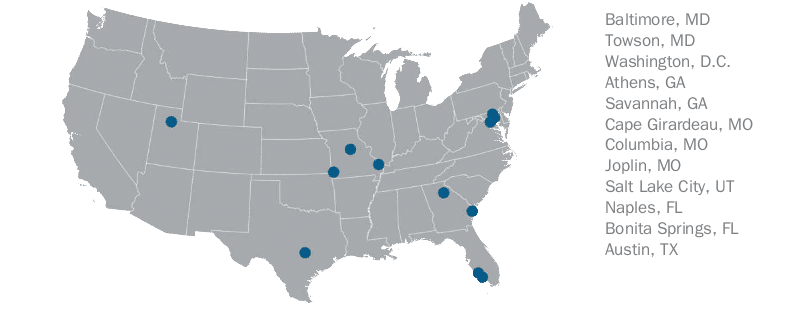
Researchers at Security Evaluators spent two years studying 12 hospitals, as well as two health data storage facilities. Researchers also analyzed supporting technologies and online services used to provide patient care.
[Read more Security Ledger coverage of healthcare security]
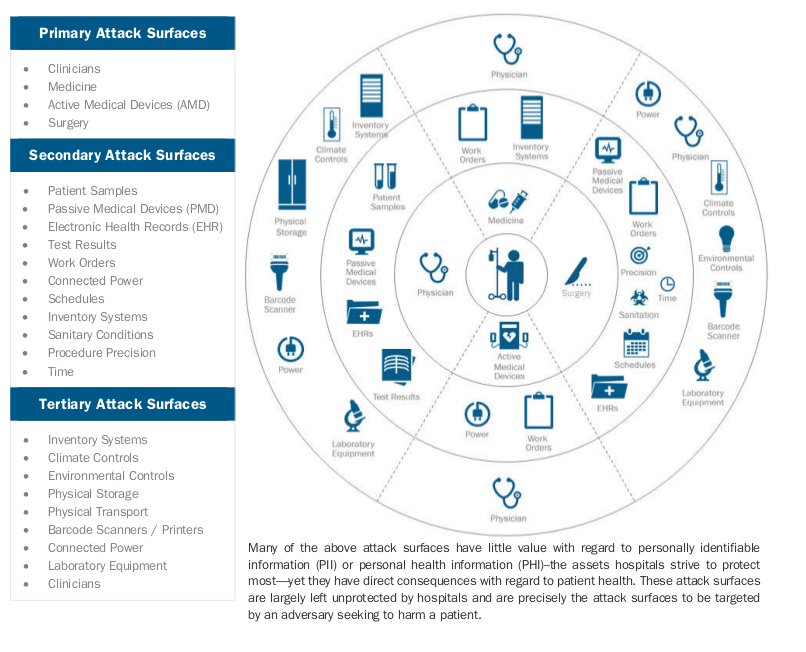
The research uncovered a number of serious concerns, including what the report describes as an “inadequate threat model” in place at many hospitals. Hospitals and healthcare facilities focus “almost exclusively on the protection of patient health records,” the researchers found. As a result, technology and information security staff rarely venture beyond that narrow focus to address broader and more serious “cyber” threats, including to patient health.
Adversaries attacking hospitals and healthcare facilities may target patient health records – which can be sold on the black market. But they may also pursue the compromise of the facility or the patient health herself, Security Evaluators note. Yet hospitals devote few resources to defending against those later scenarios.
“The healthcare industry looks at protecting patient records as a proxy for protecting patient health,” said Ted Harrington, an Executive Partner at ISE in Baltimore, Maryland.
“That’s problematic, because there are a lot of vulnerabilities that impact patient health in ways that are notably different from impacting patient records,” he said. “We asked ourselves ‘could someone launch an attack that affected patient health?'” The researchers determined that the answer was “yes,” and that doing so would not be difficult.
There were other systemic issues, as well. The researchers found what the report describes as “a drastic lack of funding for security departments,” contributes heavily to the problems that plague the industry. Lack of funding are compounded by a lack of appropriate staffing of security personnel and the absence of effective security training at “all levels of the organization.”
“Hospitals had very few proper security policies and procedures, and those that did exist were ineffective in practice. Furthermore, very little was done with regard to audit to determine what security problems existed and to create action plans to address them,” the report concludes.
Instead, security policies and practices are often subordinated to the needs and demands of clinical staff, who lack information security training.
Hospital networks studied by Security Evaluators were “antiquated in their network designs” when it came to network security. Staff was “unsure about the technologies that could effectively help them.” When security products were purchased they often were “inappropriate for the organization,” or deployed incorrectly, resulting in a waste of precious funds without any appreciable security benefit.
Hospitals also face a variety of unique problems that require special attention when addressing. Untrusted parties (i.e., patients and visitors) often have physical access to equipment and networks. People are an asset in these facilities, which is uncommon in most organizations’ security models. Furthermore, time, accuracy, and environment play a role in the survival of those assets –a circumstance not found in many other scenarios.
Security Evaluators provided free security assessments for the facilities, which were in six states and the District of Columbia. Researchers went on site at the facilities to survey network security as well as the security of equipment on site, including medical devices, looking for opportunities to exploit privileges, cross from administrative to medical device networks and so on.
Budget constraints on information security were an issue across the board. But there were also notable inefficiencies in the way budget was allocated. “Hospitals tend to focus on purchasing products rather than trying to look holistically at how to solve problems,” said Harrington. “In many cases, money they spent purchasing security products could have been better spent on training and hiring staff.”
Important decisions might be deferred based on the needs of doctors or hospital administrators, who frequently lacked the knowledge necessary to understand the security impact, he said.
Federal healthcare regulations like HIPAA and HITEC have had a profound effect on how hospitals view their mission: emphasizing the protection of “patient health information” (PHI), but saying little about “patient health,” Harrington notes.
And while many of the problems the researchers encountered within healthcare facilities are familiar to all organizations – such as the tension between the priorities of information technology groups and end users – the stakes are much higher, Harrington said.
Healthcare firms have been the target of large scale hacks in recent years, some with links to cyber criminal groups or nation-state actors. In February 2015, for example, the health insurer Anthem acknowledged that attackers made off with data on some 80 million patients after attackers gained “unauthorized access to Anthem’s IT system” and made off with “personal information from our current and former members such as their names, birthdays, medical IDs/social security numbers, street addresses, email addresses and employment information, including income data.”
More recently, Hollywood Presbyterian Medical Center in Los Angeles acknowledged this week that it ended a days-long attack that locked hospital staff out of critical systems by paying 40 BitCoin, worth approximately $17,000, to as-yet unknown and unidentified cyber criminals. The payment was made to end a 10 day long ransomware infection that had crippled many of the hospital’s patient management and diagnostic systems, including its electronic medical record (or “EMR”) system.

Pingback: Analytics Brief: Cybersecurity challenges in our hospitals | Make Data Work
Pingback: Analytics Brief: Cybersecurity challenges in our hospitals - Clouds of Big Data
Pingback: Study finds Password Misuse in Hospitals a Steaming Hot Mess | The Security Ledger