In-brief: FireEye is warning about a sophisticated campaign of online surveillance that combines web “super cookies” and common analytics software to target individuals with links to international diplomacy, the Russian government and the energy sector.
The security firm FireEye is warning about a sophisticated campaign of online surveillance that combines so-called web “super cookies” and common analytics software to target and track individuals with links to international diplomacy, the Russian government and the energy sector.
The company released a report this week that presented evidence of what the company said is a widespread campaign that combines so-called “watering hole” web sites with a tracking script dubbed “WITCHCOVEN” and Evercookie, super persistent web tracking code to assemble detailed profiles on specific users including the kind of computer they use, the applications and web browsers they have installed and what web sites they visit. While the aims of those behind the campaign aren’t known, FireEye said the use of compromised web sites and surreptitious tracking scripts doesn’t bode well.
“While many sites engage in profiling and tracking for legitimate purposes, those activities are typically conducted using normal third-party browser-based cookies and commercial ad services and analytics tools,” FireEye wrote in its report. “In this case, while the individuals behind the activity used publicly available tools, those tools had very specific purposes. Using a supercookie, in particular, implies that the actors wanted to ensure that visitors could be identified and tracked persistently over time, without having to worry about users enabling private browsing or deleting persistent cookies. This goes beyond ‘normal’ web analytics,” the company said.
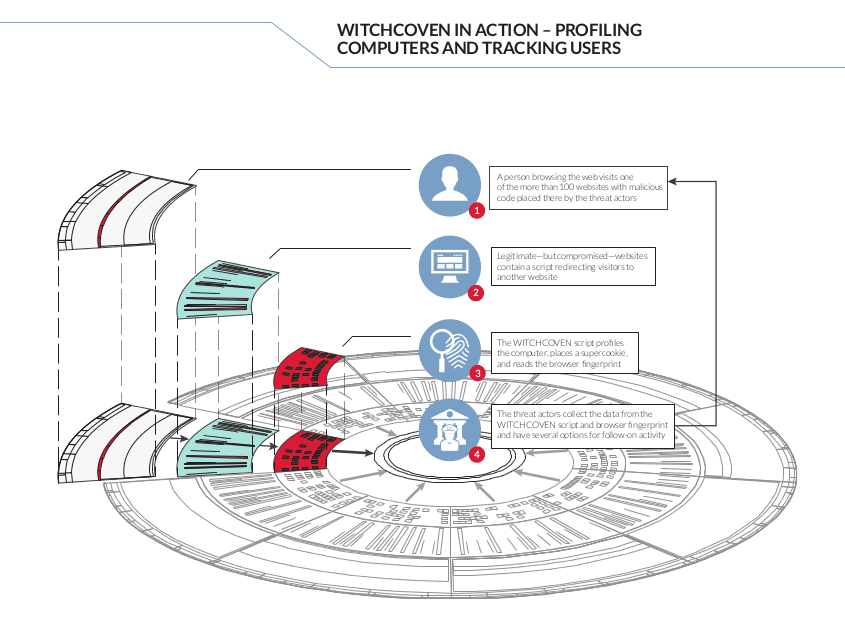
The company identified more than 100, legitimate web sites that had been compromised as part of the campaign. A redirection code was placed on the site so that visitors were sent to a secondary website, controlled by the attackers, that installed the WITCHCOVEN tracking script. That script was used to profile the compromised system and install Evercookie, a persistent web tracking cookie developed by Samy Kamkar, that can assemble a longitudinal view of all the web sites a user visits.
The campaign is remarkable in that it uses many commercial and open source tools common to mobile advertising, web publishing and even penetration testing. Among other things, FireEye detected use of programs like PluginDetect, a free library used to profile the browser plugin that a user has installed, as well as Detect Office, an open source penetration testing tool for determining what version of Microsoft Office an endpoint has installed.
Data from Evercookie and the WITCHCOVEN script are sent back to a compromised web server using an HTTP POST requests, FireEye said.
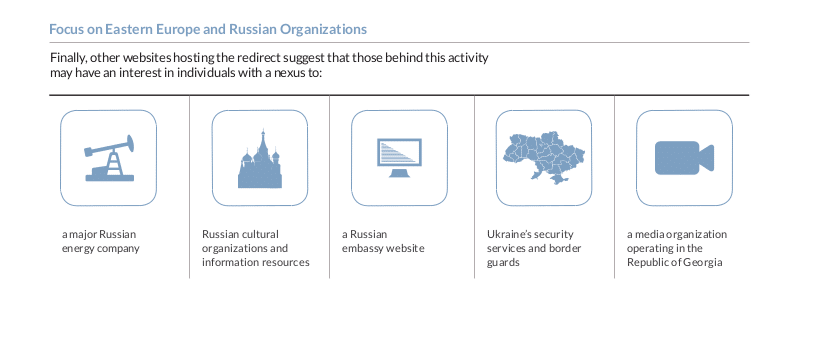
FireEye said that all the compromised web sites that were used as “watering holes” were not arbitrary but “fell into an overall pattern” described as sites that would attract “visitors involved in international travel, diplomacy, energy production and policy, and international economics, as well as those serving in foreign governments.” FireEye postulates that the actors behind the attack have links to a nation-state actor and that “all individuals that would likely have information pertinent to a state’s strategic interests.”

Among the more narrow interests that appear to be of interest to the group: Ukraine’s security services and border guards, a Russian embassy website, Russian cultural organizations, a “major Russian energy company” and a media organization operating out of the Republic of Georgia.
By combining the evercookie data with the WITCHCOVEN script profile data and HTTP logs, attackers can narrow their focus to identify specific users and to subsequently target them with a tailored exploit via a spear phishing e-mail or web link. The information could also bolster human intelligence data sources, FireEye said.
Given the quantity of data they collected from visitors to the site, the attackers may even need to rely on Customer Relationship Management (CRM) tool to create user profiles and continue monitoring individuals over time, FireEye said.
This isn’t the first time that user profiling has played a role in a targeted campaign. FireEye notes that a Chinese hacking group dubbed APT3 used a profiling script to identify targets before deploying a Flash zero-day exploit in an operation called “Clandestine Wolf.” An operation by suspected Russian hackers APT28 dubbed Russian Doll collected information about potential victim systems before deploying two zero-day exploits.
In both cases, profiling allowed exploit code to be delivered only to vulnerable systems, reducing the likelihood of detection, FireEye notes.
