We like to throw around the term ‘Advanced Persistent Threat’ casually these days to refer to a whole range of sophisticated and persistent attacks – usually on high value targets. But a blog post today by Cisco Systems makes clear that many otherwise sophisticated attackers do just fine with some pretty low tech and old school methods.
Case in point: an attack Cisco is dubbing “String of Paerls-” a series of attacks on companies involved in research and what Cisco calls the ‘industrial manufacturing vertical.’
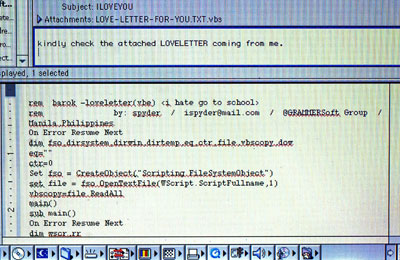
According to the report, the attacks start with a decidedly old school attack: a Microsoft Word document that includes a malicious Office Macro.”When the victim opens the Word document, an On-Open macro fires, which results in downloadin and executable and launching it on the victim’s machine.”
Now, macro-based attacks are truly vintage. They first came to light in the late 1990s, with the Melissa virus – an early and successful example of a fast spreading computer worm. They reached their apex of popularity in the early ‘nought years.
Microsoft has taken steps over the years to hamper the ability of macro-based malware to spread. But this macro, created using Visual Basic Scripting for Applications, works “quite effectively, Cisco said.
Other elements of the String of Paerls attack are more contemporary: the individual or group behind the attacks leverage the DropBox cloud based storage platform to host malware payloads that are then downloaded to the victim’s system. And, of course, the attackers rely on the continued ineffectiveness of anti malware programs. Only a small handful of AV products detected the malicious Word attachment.
The attackers have also proved adept at avoiding detection. Cisco said that research on some of the domains used in the attacks suggest that it has been active for as long as seven years – shifting between different domains and mixing up payloads and other elements of the attack.
Cisco says it has compiled a fat dossier on this particular threat actor and is publishing it in installments. You can read the first of them here: Threat Spotlight: A String of Paerls, Part One.