The revelations about US government spying keep coming fast and furious, thanks to Edward Snowden, the former Booz Allen Hamilton contractor who absconded with reams of classified (and highly classified) documents from the National Security Agency.

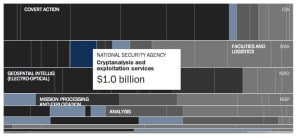
The latest details come courtesy of The Washington Post which on Thursday published documents detailing the so-called “Black Budget” – government spending on its intelligence services including the CIA and NSA – over the last nine years, including the $52 billion spent in 2013.
The documents give the most detailed accounting to date on U.S. government spending on intelligence in the post September 11 world and contain quite a few surprises. Among them: proof that the CIA receives far more money than does the NSA. But it is Uncle Sam’s work on cryptanalysis that has attracted a lot of attention from computer security and privacy experts.
First, the Black Budget reveals that the NSA alone spent around $1 billion in 2013 for cryptanlysis, while the entire government employs close to 35,000 people in its Consolidated Cryptologic Program, which includes the NSA, Air Force, Army, Navy and Marines.
What kind of work is funded with that money? The Black Budget doesn’t spell out specific investments. But, in a summary provided as part of the Congressional Budget Justification, for FY 2013 Director of National Intelligence James Clapper alludes to “groundbreaking cryptanalytic capabilities” that will allow NSA to “defeat adversarial cryptography and exploit Internet traffic.”
For anyone following the recent revelations about PRISM, the claim that the NSA is developing ways to “exploit Internet traffic” is chilling as it implies that the agency is working on or is close to having developed methods for eavesdropping on encrypted Internet communications.
A presentation at the recent Black Hat Briefings by researchers from Matasano Security, iSEC Partners and Artemis Security discussed breakthroughs in discrete mathematics that have the potential to undermine core encryption technologies, such as the widely used RSA encryption algorithm. The goal was to prepare security engineers for a “post-RSA world” in which many of the technologies that are currently used to ensure privacy online might be vulnerable to snooping by governments or private actors. The authors encouraged security conscious firms to start looking at alternatives, such as so-called “elliptic curve cryptography.”
Noted security experts like Bruce Schneier have cast doubt on the “cryptapocalypse” warnings – arguing that increasing the key length of encryption algorithms like RSA is an easy way to stay ahead of advances in compute power and the efficiency of factoring algorithms.
Still, its worth noting that the NSA itself omitted RSA from its so-called Suite B Cryptographic Standards back in 2005. Those specify which kinds of encryption can be used to secure classified and secret information on government systems. The exclusion of RSA back then implied that the NSA knew something that the rest of the world didn’t about RSA’s susceptibility to being cracked.
With $1 billion a year to spend on its cryptanalysis work and a stated interest in monitoring Internet traffic of all kinds at scale, the question is whether RSA or some other equally vital security technology has already fallen within the walls of the Agency’s Fort Meade headquarters and, if so, how the world might respond.

