RSA left few stones unturned in its recent report (PDF) on the so-called “VOHO” attacks against pro democracy, military industrial base and high finance firms. But one question that was notably left unanswered was perhaps the most important: “Who, or what, was behind the attacks?” Now the lead RSA security researcher trusted with analyzing the malware used in recent “watering hole” attacks tells Security Ledger that the malware left some clues as to the origins of the attacks, which affected tens of thousands of systems in more than 700 organizations, but not enough to conclusively link VOHO to a specific group, country or actor.
“It’s hard to tell,” said Chris Elisan, a Principal Malware Scientist at RSA and the lead investigator into the malware used in the VOHO attacks. “The malware is only part of it,” he said.

Other parts of what Elisan called the “attack chain” are needed to identify it as coming from a particular country or a known hacking crew, cyber criminal gang or cyber warfare unit. “You have to have all the components – the C&C (command and control) infrastructure, the drop zones (where stolen data is deposited), the malware update servers,” he said. “Its that combination of technical elements that let you identify the human element behind the attack – but that’s a long process.”
Elisan said that researchers will need more time to gather evidence about the attacks before they can offer thoughts on who or what was behind it. Asked whether there were any clues in the decompiled binaries collected from the attack that suggested whether the attack originated in China, as many have speculated, or somewhere else.
“Even if there are indicators there it’s not conclusive. Someone could put Chinese sayings or characters in there to fool people,” he said.
The official RSA report on the water holing, or VOHO, attacks was circumspect, also. The report doesn’t make a direct reference to “China,” though it acknowledges that a component of the VOHO attacks, a script dubbed xKungfoos, “likely originated in Asia” where it was used in attacks on political dissidents.
So, too, an earlier report by the security firm Symantec (PDF), which described the same campaign of sophisticated attacks and the use of “watering hole” sites. Symantec attributed the attacks to what it called the “Elderwood Project” or the “Elderwood Platform,” but made few suggestions of who or what owned and operated “Elderwood.”
However, in its “Conclusions,” RSA’s First Watch team said that the eight month old VOHO attacks were “carried out by threat actors commonly referred to in the industry as ‘APT’,” noting the use of the xKungFoo script in particular, the use of command and control infrastructure “in the Hong Kong area” and the similarities between the VOHO attacks and both the Aurora and GhostNet attacks – both of which were attributed directly to the Chinese government.
Similarly, Symantec’s report notes – tellingly – that human rights and religious groups concentrated in CHina, Hong Kong and Taiwan were the “second most common ” target after Western defense industries.

Of course, attribution in cyber attacks is always a difficult matter, and at least one authority on cyber war and cyber crime has criticized RSA for what he considers loose talk in the VOHO report.
“My issue was a lack of analysis on attribution options,” said Jeffrey Carr, the founder and CEO of TAIA Global, a boutique cyber security firm that specializes in protecting corporations from cyber crime and cyber espionage.
“They just assumed it was China and said as much by using the term ‘APT’ which is simply a poorly-kept ‘secret code word’ for China with its origins coming from the U.S. Air Force,” Carr wrote in an e-mail to Security Ledger.
Carr believes that connecting the use of specific scripts that have appeared in other attacks, or the geographic location of command and control servers don’t come close to meeting the standard of proof for attribution of a cyber attack.
Asked about the VOHO attacks, Mila Parkour, the malware analyst at Contagio, said that her guess was “China.” But she agreed that the attacks employed very common methods – like drive by downloads – to gain a foothold, and software exploits, malware and scripts that were both new and known – in other words: the portrait of the attacker or attackers is blurry.
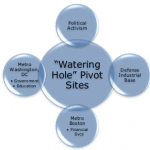
Will Gragido, the Senior Manager of Threat Research Intelligence at RSA said that the attackers choices of so-called “watering hole” sites that served as lures for victims were also carefully made.
“There was a combination of both surveillance and reconnaissance on the site,” he told Security Ledger. “The sites they chose had proximity and relevance and meaning to the target of interest…It was very highly thought out.” Similarly, the choice of targets involved with promoting democracy as well as with links to the U.S. Defense industry suggested that the attack was not merely opportunistic.
“There was a geopolitical intent that was strong and pervasive,” he said. “I think the data that we brought forth clearly revealed a pattern.” But Gragido also declined to say whether or not the clues his company had gathered pointed conclusively to China – or another nation- as being behind the VOHO hack. The nature of cyber attacks and cyber investigation makes it too easy for the real perpetrators to have plausible deniability, and for those investigating the crime to jump to incorrect conclusions, he said. “So, do you have copycats pursuing fraud using some of the organizational elements? Or do you have myriad elements launching parallel campaigns but using attack models that intersect?” Gragido posited. Many experts say its difficult to know for sure.
Parkour said that future attacks of this type may use similar tactics, or not – depending on what will allow the attackers to achieve their objective. “The exploits may change…the way legitimate sites are hacked may change. The trojans that were mentioned were (from the) Gh0st (family) but others could be used, too,” she wrote. But those changes won’t necessarily identify which actor is behind the attacks themselves.
The most surprising quality of VOHO was not any detail of the attack, itself, but that it was uncovered early and observed as it unfolded, said Gragido, not the attack itself. “This isn’t the only VOHO out there,” he said. “There could be any number of variants. This is just the one we have, and its unique to us.”
In the end, attribution for the attacks isn’t important or relevant for victims – unless they happen to be governments that are capable of (and interested in) retaliation, Carr said.
“Bottom line, you defend against a multitude of attacks in the same way, so attribution is irrelevant. But if you’re a government and you want to respond to an attack, proper attribution is vital.”