The U.S. government’s federal technology agency has published a draft version of a voluntary framework it hopes will guide the private sector in reducing the risk of cyber attacks on critical infrastructure. The National Institute of Standards and Technology (NIST) published a draft of its Preliminary Framework to Reduce Cyber Risks to Critical Infrastructure on Monday. The document provides a guide for critical infrastructure owners of different maturity levels to begin documenting and understanding their risk of cyber attack, and – eventually – to measure their performance in areas such as asset management, threat detection and incident response. The framework was called for by Executive Order 13636, signed by President Obama in February. In that order, NIST was charged with creating a framework for sharing cyber security threat information and information on successful approaches to reduce risks to critical infrastructure. The Framework is comprised of five major cybersecurity functions: Know […]
terrorism
NSA’s PRISM Puts Privacy Startup Silent Circle Into Orbit
Government surveillance has been getting a lot of attention in recent weeks, with the leak of classified information about spying by the National Security Agency using information provided by U.S. telecommunications and Internet firms including Verizon, Facebook, Google and Apple. The stories have revealed the very different legal standards that govern electronic communications and more traditional communications such as phone and postal mail. They have also put many otherwise lawful Internet users in search of technology that will keep their private conversations and thoughts well…private. That, in turn, has sparked concern in the government that civilian use of encryption will hamper lawful interception of communications. Wired.com reported last week that, for the first time, encryption thwarted government surveillance under court-approved wiretaps. That report, from the U.S. Administrative Office of the Courts (AO), said encryption was reported for 15 wiretaps in 2012, compared with just 7 wiretaps conducted during previous years. […]
Don’t Call It A Hack Back: Crowdstrike Unveils Falcon Platform
Lots of aspiring technology start-ups dream of getting their product written up in The New York Times or Wall Street Journal when it launches. For Crowdstrike Inc. a two year-old security start-up based in Laguna Niguel, California, media attention from the papers of record hasn’t been an issue. This reporter counted twelve articles mentioning the company in The Times in the last year, and another two reports in The Journal. Much of that ink has been spilled on stories related to Crowdstrike research on sophisticated attacks, or the company’s all-star executive team, including former McAfee executives George Kurtz (CEO) and Dmitri Alperovitch (CTO), as well as former FBI cybersecurity chief Shawn Henry (Crowdstrike’s head of services), who left the Bureau in April, 2012 to join the company. For much of that time, Crowdstrike has been known mostly as a security services and intelligence firm, but the goal was always to […]
Update: Serial Server Flaws Expose Critical Infrastructure
A survey conducted by the firm Rapid 7 has found evidence that widespread vulnerabilities and insecure configuration of ubiquitous networking components known as serial port (or “terminal”) servers, may expose a wide range of companies and critical assets – including point of sale terminals, ATMs and industrial control systems – to remote cyber attacks.(*) The vulnerable devices connected hardware like retail point-of-sale systems at a national chain of dry cleaners, providing direct access to employee terminals from which customer payment information could be accessed. Other exposed systems were used to monitor the location of cargo containers, train cargo as well as HVAC and industrial control systems, Rapid7 said. In the Rapid7 survey, over 114,000 unique IPs were identified in a scan using the Simple Network Management Protocol (SNMP), the vast majority manufactured by one company: Digi International. If left unaddressed, the vulnerable devices give remote attackers direct, administrative access to hardware devices […]
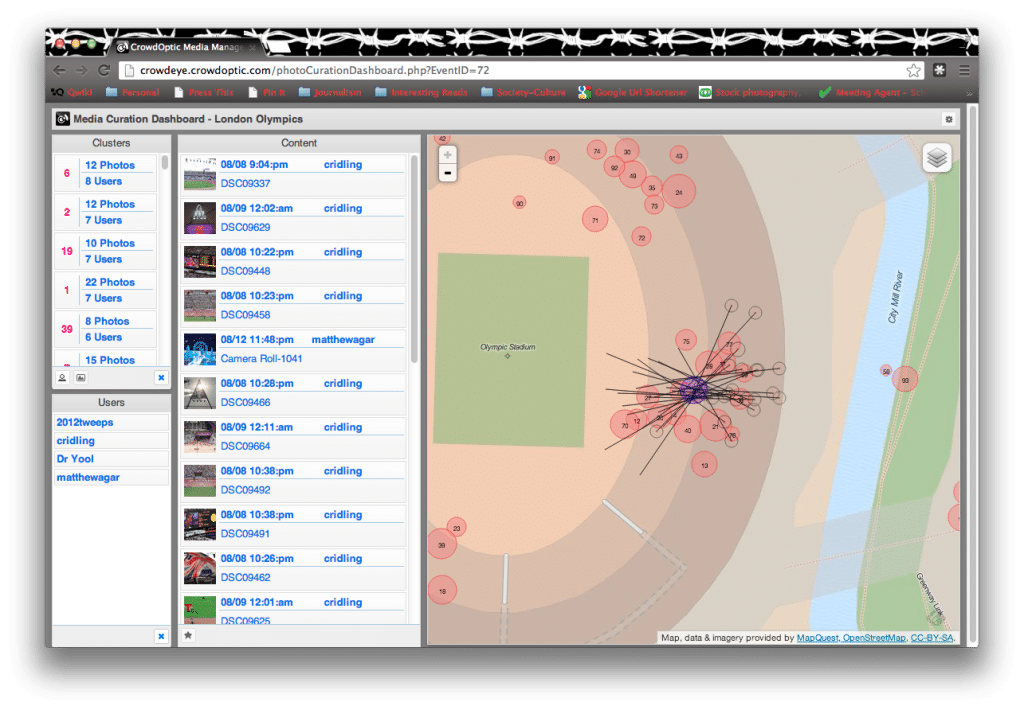
Meet The Software That Helped Catch The Boston Bombers
With one suspect in the Boston Marathon bombings dead and another on the run IN CUSTODY! the global, collective effort to identify those responsible for the crime has ended, and focus shifted to apprehending PROSECUTING Dzhokhor A. Tsarnaev, 19. He and his older brother, Tamerlan Tsarnaev, 26, were the subject of a massive manhunt, culminating in a firefight in the suburb of Watertown, Massachusetts, that killed the older Tsarnaev brother and set of a massive, daylong manhunt that shut down the metropolitan Boston area.(*) So how did crowdsourcing fare in the effort to catch the two? You’d have to say: not too well. High-profile collaborative efforts to crowdsource public images of the Boston Marathon bombing site, like those organized by the group 4Chan, assembled intriguing collections of material and clocked impressive pageviews (3.4 million and counting). In the end, those efforts yielded some clues: the type of clothing worn by the suspects, […]