In-brief: Andrew Auernheimer, an online provocateur who uses the handle “Weev,” has taken credit for causing 30,000 Internet connected printers to spew out antisemitic statements. Many of the connected printers were on the campuses of colleges and universities.
Bash
Unpatched Vulnerabilities Common on Docker Hub Images
In-brief: A survey out from the firm Banyan finds that official and general repositories on Docker Hub are rife with serious and exploitable software vulnerabilities, including Heartbleed, Shellshock and Poodle.
Ghost Vulnerability Replays Third Party Code Woes
In-brief: The security firm Qualys is warning of a serious and remotely exploitable vulnerability in a function of the GNU C Library (glibc) known as gethostbyname. The security hole raises more questions about dangers lurking in legacy, open source software.
Surprise: Branding a Bug is just as Hard as Branding Anything Else!
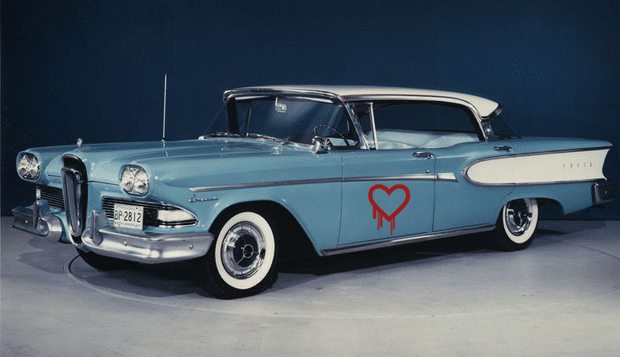
ZDNet’s @violetblue has a nice piece on the new fad for naming vulnerabilities – seen most recently with the OpenSSL Heartbleed vulnerability and the “Shellshock” vulnerability in Linux’s common BASH utility. As Blue notes, the desire to “brand” bugs “changes the way we talk about security” – in part by giving complex, technical flaws down a common referent. But does giving a bug a logo make it frivolous? As she notes: the penchant for naming vulnerabilities may stem not from a desire to trivialize them – but a very practical response to the need to keep track of so many security holes in software. Regardless, Heartbleed – and the marketing by the firm Codenomicon that surrounde it – was the bug that launched a thousand ships, including Shellshock, Sandworm, and more. Read more coverage of Heartbleed here. But, as with . As security research and incident response are becoming more lucrative, expect the masonry […]
Whack-A-Bash: New Vulnerabilities add to Patch Confusion
The good news about the rapid, industry response to the revelations about exploitable security holes in GNU Bash (Bourne Again Shell) (aka “Shellshock”) is that Linux users had a fix in hand almost as soon as they became aware of the problem those patches addressed. The bad news about the quick fixes for the two issues, CVE-2014-6271 and CVE-2014-7169, from the likes of Red Hat, Ubuntu, Debian and others is that – in being early- they fail to fix the problems we don’t yet know about. And that’s what we’re seeing in the wake of last week’s storm of patches: a steady drip-drip of disclosures that suggest that Bash may contain other problems worthy of new fixes. Within hours of the disclosure of the first holes, there were problems discovered by Red Hat Product Security researcher Todd Sabin, who found additional “off by one” errors in Bash that were assigned CVE-2014-7186 and CVE-2014-7187 and […]