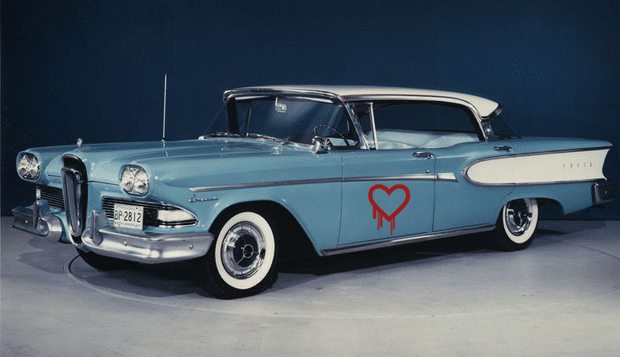
ZDNet’s @violetblue has a nice piece on the new fad for naming vulnerabilities – seen most recently with the OpenSSL Heartbleed vulnerability and the “Shellshock” vulnerability in Linux’s common BASH utility.
As Blue notes, the desire to “brand” bugs “changes the way we talk about security” – in part by giving complex, technical flaws down a common referent. But does giving a bug a logo make it frivolous?
As she notes: the penchant for naming vulnerabilities may stem not from a desire to trivialize them – but a very practical response to the need to keep track of so many security holes in software.
Regardless, Heartbleed – and the marketing by the firm Codenomicon that surrounde it – was the bug that launched a thousand ships, including Shellshock, Sandworm, and more.
| Read more coverage of Heartbleed here. |
But, as with . As security research and incident response are becoming more lucrative, expect the masonry of the trade – vulnerabilities, tools, techniques – to become more commercialized as well. Whether that will be good for the overall health of the community or not remains to be seen.
Read more on ZDNET’s Zero Day Blog via The branded bug: Meet the people who name vulnerabilities | ZDNet.
