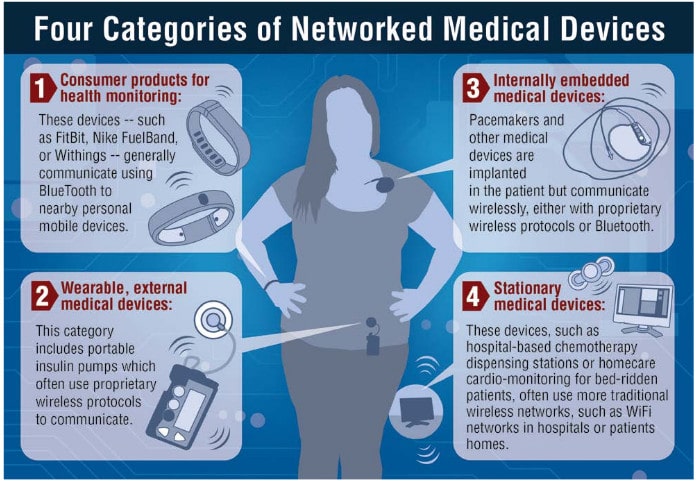
In this Spotlight Podcast, sponsored by Synopsys: In the wake of a presentation at Black Hat about security flaws in implantable pace maker devices, Synopsys Principal Consultant Dan Lyon joins us to talk about why medical device makers struggle to make their connected medical devices more secure. Dan and I discuss some of the flaws in the approach that medical device makers take to security, and how manufacturers can take a page out of their own book: applying the same standards to cyber security as they do to – say- device safety.
infusion pump
Securing Medical Devices, Rethinking OWASP’s Top 10 & BlackDuck CEO Lou Shipley
In this, our 70th episode of The Security Ledger podcast, we speak withXu Zou of the Internet of Things security startup Zingbox about the challenges of securing medical devices and clinical networks from cyber attack. Also: we take a look at the turmoil that has erupted around the OWASP Top 10, a list of common application security foibles. And finally: open source management vendor Black Duck Software announced that it was being acquired for more than half a billion dollars. We sit down with Black Duck CEO Lou Shipley to talk about the software supply chain and to hear what’s next for his company.
Code Blue: 8k Vulnerabilities in Software to manage Cardiac Devices
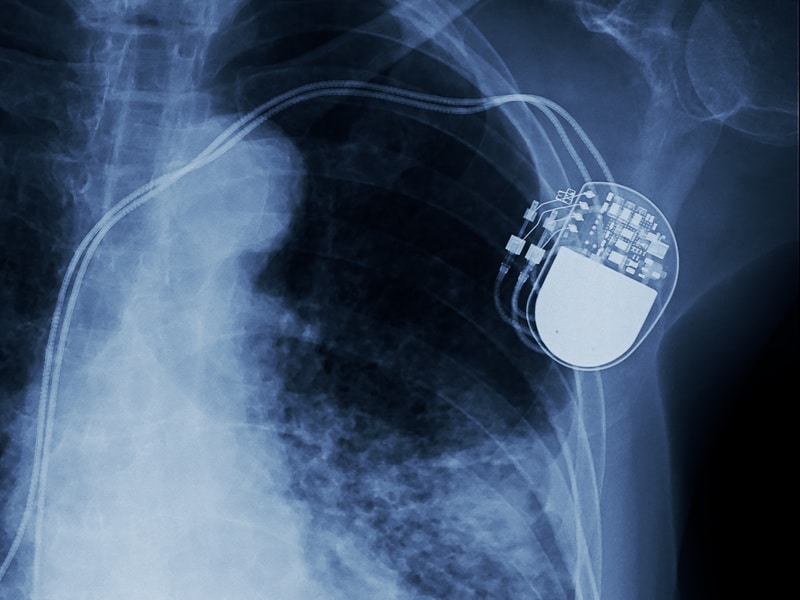
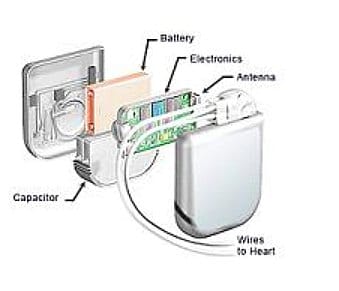
Software used to remotely program implantable cardiac devices by a number of vendors is rife with exploitable software vulnerabilities that leave the devices vulnerable to attacks and compromise, according to a report by the firm Whitescope Inc.
The Big Short: Alleged Security Flaws Fuel Bet Against St. Jude Medical
In-brief: The stock of medical device maker St. Jude plunged by 5% on Thursday after a report called for investors to bet against (or “short”) the company’s stock over serious security vulnerabilities in a range of the company’s implantable cardiac devices.
Could hackers break my heart via my pacemaker? – BBC News
In-brief: A BBC article profiles an information security expert who finds herself the bearer of an implanted pacemaker, raising issues about the risks and benefits of new, connected health devices.