(Updated) Psst! I’ve got a 15 year old tablet running Windows CE. Interested? It’s a bargain at just $5,600!
If that statement strikes you as insane, then you’re probably not a farmer who relies on heavy equipment manufactured by John Deere. For that group, decade old, second hand monitors to run its heavy equipment routinely sell online for thousands of dollars, despite running (comparatively) ancient hardware and buggy, outdated software.
But that upside down market may be due for a shakeup, after a security researcher known as Sick Codes used a presentation at the DEF CON hacker conference to show off a jailbreak of a recent vintage Deere monitor that allowed him to run a version of the classic first-person-shooter DOOM on Deere’s proprietary hardware.
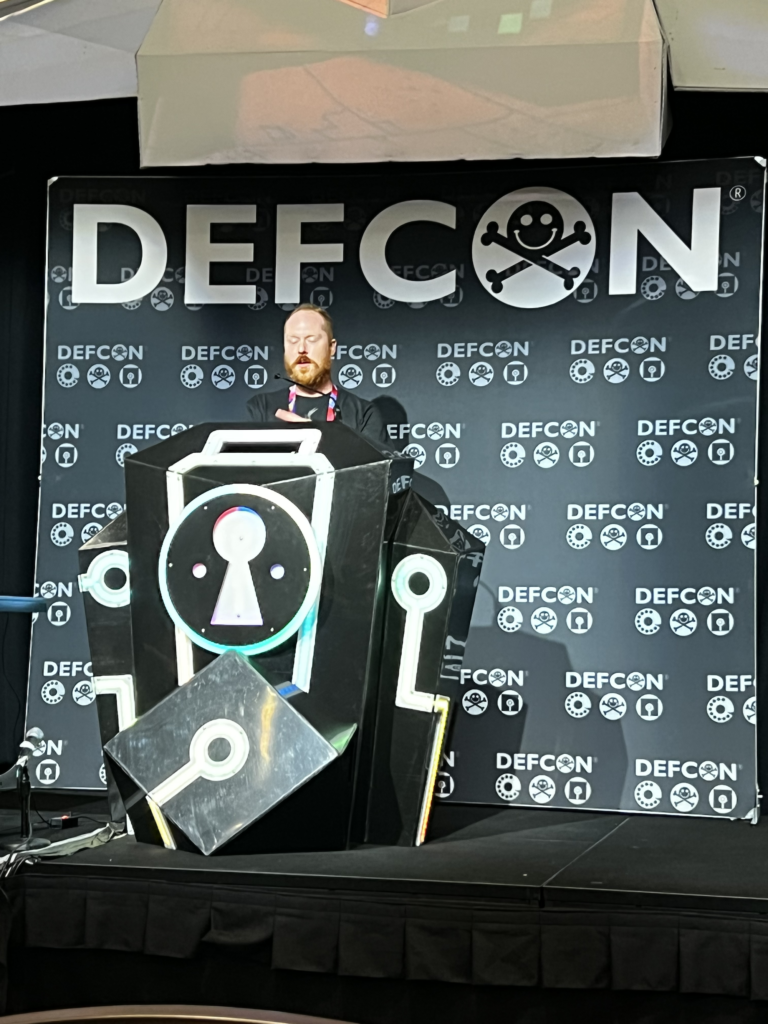
The presentation by Sick Codes on Saturday at the annual conference in Las Vegas – affectionately referred to as “hacker summer camp” -followed a similar talk last year in which the Australian-born researcher exposed widespread software vulnerabilities in software from Deere, Case IH and other agricultural equipment makers. In that talk, Sick Codes (@SickCodes), who works independently and declines to use his real name in public statements, worked with researchers from the group Sakura Samurai, uncovering 11 other flaws in Deere software and applications and that the group shared with the company as well as CISA, the Cybersecurity and Infrastructure Security Agency.
DEF CON: Security Holes in Deere, Case IH Shine Spotlight on Agriculture Cyber Risk
For this year’s talk, Sick Codes turned his attention from Deere’s software and services to the hardware that is installed in its farm machinery, which regularly sells for high six- and even seven figure sums. Most Deere equipment manufactured in the last 20 years is software driven, with farm implements equipped with in-cabin touch screen monitors that are used to control an array of ECUs (Electronic Control Units) on the equipment. That interface is supplemented by data from cellular mobile telematics gateways (MTGs) that communicate with cloud based servers run by Deere, as well as satellite based connections for realtime GPS signals that are used to direct the device in the field.
The Not-So-Mysterious Case of the $8k Windows CE Box
Unlike smartphones or laptops, farm equipment is expensive and is expected to be long-lived, with useful lives measured in decades rather than years. That has created a healthy aftermarket for parts – like 25 year old Deere 1800 series “Brown Box” monitors running Windows CE, that still sell for hundreds of dollars each.
Cyber Attack Halts Production at Ag Equipment Maker AGCO Fendt
“Farmers need equipment to be extremely reliable. When things go wrong during planting season or harvesting season, farmers get extremely frustrated, to say the least,” Sick Codes told the audience. Older monitors are particularly valuable because they come with “lifetime unlocks” – permanent subscription codes that can be transferred with the device itself, he said. The most common Deere monitor, the 2630, is 15 years old and runs a version of Microsoft’s Windows CE Version 6 operating system that is no longer supported by Microsoft. It sells for more than $8,000 online.
Sick Codes’ talk documented an exhaustive, year-long effort to extract software from a Deere 4240 monitor: buying second hand hardware on eBay, removing chips and other hardware from logic boards and extracting the software stored in the chips to understand better how the monitors work. That process was ripe with failures and re-starts, but eventually resulted in him extracting the underlying software from the 4240 monitor, a version of the WindRiver Linux operating system.
Feel Good Ukraine Tractor Story Highlights Ag Cyber Risk
The presentation is one of the first public efforts to “jailbreak” Deere hardware – a term used to describe removing restrictions put in place by hardware manufacturers that prevent device owners from running unauthorized software on the device. Jailbreaking has mostly attracted attention in the smart phone space, where some iPhone owners jailbreak their devices to permit them to load applications from sources other than Apple’s closely controlled App Store.
For farmers, the prospect of freeing themselves from a reliance on Deere software would be a game changer. In the last year, more than a dozen class action suits have been filed against the company by farmers over restrictions on service and repair that, plaintiffs claim, amount to an illegal monopoly.
Deere is estimated to control 53 percent of the U.S. market for large tractors and 60 percent of the U.S. market for farm combines. Unlike the automobile industry, however, where a Massachusetts law from 2013 provides owners and independent repair professionals with access to tools, software and information needed to diagnose and repair vehicles, no right to repair exists for agricultural equipment.
Practically, that means even common repairs requires the cooperation of a Deere dealership or authorized repair professional. That gives Deere the power to lock out customers or independent repair providers – anyone the company doesn’t designate an authorized repair professional. Ben Evers, a Nebraska farmer and owner of FarmFocused.com said that even simple repairs like replacing a broken injector require access to the dealer version of Deere’s Service Advisor software, which Deere refuses to make available to equipment owners. “You have to program in an ID for the ECU (Engine Controller Unit) to recognize (the part) and for the engine to run,” Evers notes.
Responding to customer complaints as well as renewed interest by the FTC in repair restrictions, Deere has said that it will make diagnostic software and information more available to farmers, who now must rely on John Deere authorized repair professionals for most substantive maintenance. However, as reported here, the company still charges thousands of dollars for an annual subscription to its Customer Service Advisor software, and Deere still severely restricts the ability of farmers to do many common repairs, even with a CSA subscription.
Sick Codes said his hope is that his research and demonstration of the DOOM game running on a Deere 4240 display will re-balance that skewed relationship, regardless of what Deere does- or doesn’t do. His example shows that farmers can “bypass dealership bullshit and run their own equipment.”
Asked whether he thought the prospect of running third party operating systems and applications on John Deere hardware was close at hand, Sick Codes responded “beyond close.”
Kevin Kenney of Grassroots Energy, who has worked to challenge Deere’s repair and service monopoly, said that it is critical for farmers to be able to run they own software and that freeing them from the kinds of vendor lock-in that Deere has instituted will save them thousands of dollars a year for each piece of equipment in operating costs and “give them back control of their own property.”
Right to repair advocates saw cause for optimism following the talk.
“John Deere’s refusal to allow growers to repair the computers on their tractors is increasingly untenable,” said Kyle Wiens, the founder of the repair website iFixit.com. “Building on research like this, I expect that farmers will start creating their own software tools.”
Red Flags Flying for Agriculture Cybersecurity
But demonstrating the possibility of a future in which Deere’s industry-leading hardware is liberated from the company’s onerous software is just one aspect of the DEF CON presentation. The other concerns the revelation that the majority of equipment critical to the U.S. food supply is running on a no-longer-supported operating system that was last updated 13 years ago.
That poses serious questions about the vulnerability of U.S. agriculture to cyber attacks, Sick Codes noted.
In addition to figuring out how to run third party code on Deere hardware, the researcher says he discovered a number of serious, exploitable software holes in the process. However, he has so far declined to disclose them, as John Deere’s official bug bounty program excludes vulnerabilities discovered on the software that runs Deere’s equipment, he told Security Ledger. He said official vulnerability disclosures via MITRE or another CVE Numbering Authority (CNA) are “in the cards,” but are not a priority right now. “I’m just working for free, so it gets done when it gets done,” Sick Codes said in an exchange via a secure messaging application.
Deere did not respond to an email request from Security Ledger for comment prior to publication of this story. We will update the story should the company offer comments subsequent to publication.
In an email statement to The Security Ledger, a John Deere spokesperson said the company’s “top priority is, and will always be, to protect our customers, their machines, and their data. The capabilities that Sick Codes demonstrated during his recent presentation at DEF CON were obtained through invasive/persistent physical access, disassembly of a hardware product and reverse engineering of proprietary software. At no point were a customer or dealer’s equipment, networks, or data at risk.”
(Editor’s note: technically this isn’t true, as Sick Codes suggested that some of the second hand John Deere hardware he purchased online still contained data from the prior customer that had not been wiped prior to sale.)
Deere said that “any researcher, given unfettered physical access and time, will eventually be able to adversely impact the operations of a device, and no company, including John Deere, is immune to such access.” However, the company said it was “deeply committed and work tirelessly to safeguard our customers, and the role they play in the global food supply chain. In addition to a dedicated team of over 300 product and information security professionals, we also work closely with industry-leading cybersecurity partners like HackerOne and embrace the broader ethical hacking community to ensure our security capabilities continue to lead the industry.”
The company was asked by Security Ledger whether it would consider expanding its public bug bounty program, which considers hardware based flaws “out of scope.” In its response, Deere did not provide a response to that question.
The federal government has taken an increased interest in cyber security risks to agriculture in recent months. Ransomware attacks on the meat processor JBS and grain co-ops throughout the midwest have underscored how U.S. food production is vulnerable to cyber disruption. CISA as well as the FBI issued a warning in April, 2022 following a string of ransomware attacks targeting grain cooperatives in the midwest.
However, that interest has so-far not extended to the agricultural equipment market, where manufacturers like Deere, Case IH and others are promoting “precision agriculture” using Internet connected and (often) autonomous equipment that promises to transform farming by increasing productivity and reducing labor costs. To date, however, little is known about the cyber security of such devices. And, with per-device costs in the high six and low seven figure range, even the most profitable cybersecurity firms can scarce afford to buy devices merely for the purposes of security testing, experts say.
That has prompted calls for the federal government to take a more active role in assessing and monitoring the cybersecurity of the fast-emerging precision agriculture sector.
The findings of researches like Sick Codes suggest that the security of agriculture hardware and related services bears scrutiny. In his presentation last year, for example, Sick Codes described a range of trivial flaws he discovered in Deere’s JDConnect and the John Deere Operations Center, which allows company support technicians and dealerships to remotely connect to and control equipment in the field.
For example, Sick Codes said that he discovered a DOM (document object model) cross site scripting (or XSS) flaw almost immediately after logging into Deere’s developer site. CDOM-based cross site scripting attacks allow the attacker to make malicious modifications to how a vulnerable website runs by altering client side code contained in the page.
However, tools like Operations Center can directly affect the operation of equipment in the field. In May, for example, Deere remotely disabled machinery stolen from a Ukrainian dealership by invading Russian troops. Such capabilities in the hands of a cybercriminal or nation-state actor could severely impact U.S. food production, experts have warned.
Recent years have seen the cyber security of hardware and critical infrastructure take on a higher profile at the DEF CON conference, which is in its 30th year. This year’s event featured “villages” focused on car hacking, voting machines, medical device (or medtech) hacking, Internet of Things and aerospace, among others.
(Editor’s note: this story was updated to include comment from John Deere. PFR 8/15/2022)


Pingback: Episode 242: Hacking the Farm (and John Deere) with Sick Codes
Pingback: Hacking the Farm (and John Deere) with In poor health Codes - Firnco
Pingback: Episode 242: Hacking the Farm (and John Deere) with Sick Codes – Raymond Tec
Pingback: Supply Chain Hackers LofyGang Behind Hundreds of Malicious Packages – Raymond Tec