Podcast: Play in new window | Download (Duration: 30:41 — 35.1MB) | Embed
In this episode of the podcast (#165), we talk with 19 year-old Noah Clements of University of New Brunswick about the blowback he received after reporting a serious hole in a smart doorbell. Also, staff attorney Tamir Israel from the Canadian Internet Policy and Public Interest Clinic (CIPPIC) joins us to talk about the still evolving legal picture for independent security researchers in Canada.
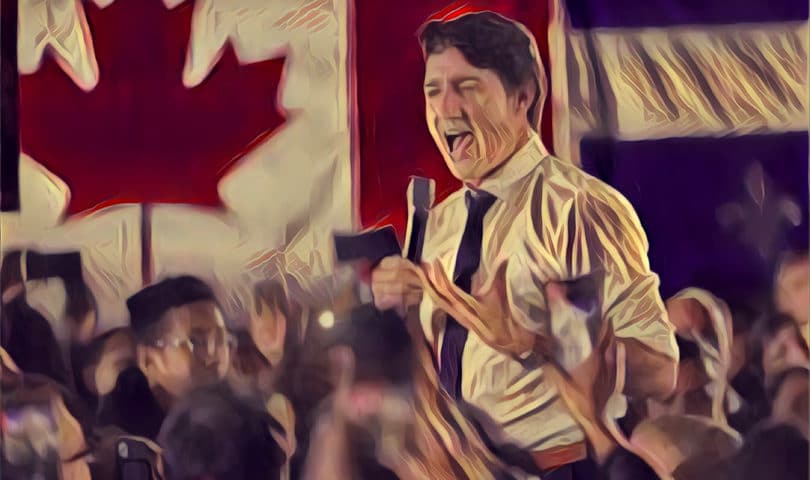
As Canada’s young, charismatic Prime Minister Justin Trudeau charged over the finish line to victory in national elections last week, the U.S.’s neighbor to the North seemed on track to retain its reputation as a redoubt of polite and progressive politics in North America.
But for independent security researchers, Canada’s reputation as a welcoming and friendly country may ring hollow. In fact, an absence of clear legal precedents risks making Canada a pretty cold and unwelcoming place for independent security researchers, just as their skills are needed the most.
In this week’s episode of the podcast we are looking at the issue two ways.
Ringing the Doh! Bell
If you want to understand how chilly it can be in Canada for independent security researchers, consider the experience of Noah Clement might be a good person to talk to. The 19 year old undergraduate at the University of New Brunswick took the opportunity to dig into the workings of a smart doorbell his parents had purchased for their home.

Noah’s discoveries led to the disclosure of serious vulnerability. Among other things, the device, the DB01-S Gen 1 from the Canadian firm dbell allows remote attackers to launch commands with no authentication verification via TCP port 81. That could allow attackers to send arbitrary commands to any doorbell it could connect to remotely or from the same wireless network. And, because the dbell also sports integrations with smart door locks, the flaw could potentially allow an attacker to open the door to the house from the Internet. (Noah posted a video of the “unlock door” attack here.)
Much of what Noah discovered is sadly common in connected or “smart” home devices. The doorbell, which was supposed to be controlled via a mobile app, sported an embedded web server that could be accessed via TCP Port 81 without needing any authentication at all.
But Clements experience after reporting the hole is one that is becoming less common for researchers in the U.S. and elsewhere.

Dbell initially welcomed Noah’s vulnerability report and even offered him a new dbell model at a reduced price in exchange for his help testing it. But the firm quickly became hostile when Noah expressed his desire to go public with his findings. That led to a months-long odyssey between Noah, dbell and dbell’s attorneys, which included everything from gratitude to charges of extortion and threats of legal action.
“If you were really genuine and honest to helping others and you had no malicious intention for extortion, you would have accepted the offer for our current product.”
email sent to Clements from dBell support team
For its part, dbell argued that the model that Noah tested had been discontinued by the time he discovered the flaws and therefore no longer posed a threat. However, in communications with Noah and Security Ledger, the firm declined to say how many of the affected devices it sold and whether effected models already deployed had been patched, replaced, disabled or what.
In a statement to Security Ledger, dbell said “any clients who had that model we gave an opportunity to upgrade to newer device.” It did not respond to a request for clarification as to whether those customers were give a free replacement or merely given the option to upgrade.
Eventually, with help from attorneys at Canada’s Internet Policy and Public Interest Clinic (CIPPIC), Noah was able to get dbell to drop its threats, but the whole experience left him with a bad taste in his mouth.
Check out Noah’s full story in our first segment.
A chill on Security Research
In our second segment, we dig a bit deeper into what’s behind Noah’s experience by talking with the attorney who helped fend off aggressive efforts by dbell and its attorneys to silence him. Our guest is Tamir Israel of Canadian Internet Policy and Public Interest Clinic (CIPPIC).

Its a common refrain that there are more similarities than differences between Canada and the United States – two countries that share a centuries old friendship and the longest open border in the world. But when it comes to protections for the work of independent security researchers, Canada often lags behind its neighbor to the south, Israel tells me. In this interview, Israel and I talk about the challenges faced by security researchers in Canada and the lack of clear case law protecting their work.
The problem isn’t a lack of laws, but a paucity of case law that clear up thorny issues such as whether independent investigations by white hats like Clements constitute illegal “hacking.” That lack of clear rulings makes even straight forward cases like Clements -where the researcher does everything by the book – legally fraught, Israel tells me.
Check out our conversation in part two of the podcast.

Pingback: Issue #85 – Volume XXI – SANS Newsbites – October 29th, 2019 | OSINT
Pingback: Westcom Medium ~ Info Tech Industry News December 1, 2019