The compromise of device maker Asus Live Update Utility is just the latest evidence that sophisticated attackers have software supply chains in the crosshairs.
News that computer maker Asus unknowingly pushed malware out onto thousands of its computers last year after one of its servers was hacked highlights a persistent vulnerability in the software supply chain– and one that bad actors are increasingly interested in exploiting.
Kaspersky Labs revealed Monday that the computer maker pushed out a compromised version of a utility via its own update service. That, after a threat actor last year modified the ASUS Live Update Utility, which delivers BIOS, UEFI and software updates to ASUS-manufactured laptop and desktop computers.
Live Update gone bad
The hackers added a “Trojan” back door to the utility, and then distributed it to users through official channels. That made it difficult to detect because the malicious software–which Kaspersky dubbed “ShadowHammer”–was signed with a legitimate certificate and hosted on the official dedicated ASUS update server.
Podcast Episode 115: Joe Grand on Unicorn Spotting and Bloomberg’s Supply Chain Story
“The criminals even made sure the file size of the malicious utility stayed the same as that of the original one,” Kaspersky wrote in a blog post published Monday.
The ASUS attack shows why supply chain remains one of the most difficult channels for companies to secure, they said.
“The ASUS backdoor exposes a trusted-vendor’s channel compromise distribution vector, which has historically caused damage worldwide,” said Colin Little, senior threat analyst from network cybersecurity firm Centripetal Networks.
No NotPetya… but still a big problem
Little cited the NotPetya malware, which cost hundreds of millions of dollars in damage after being unleashed on the Ukraine in 2017. The malware used the same distribution vector from a popular accounting software provider, making it difficult to detect.
“When we consider this history, we plainly see the need for validation of trusted-vendor channels in addition to digital signatures not just for software and platform updates, but any ‘trusted’ vendor network which has access into our environment requires validation above and beyond what the current offerings are,” he said. “The world is lucky there was not a cyber weapon involved in the ASUS backdoor, such as with the NotPetya example.”
Cisco Links Remote Access Tool Remcos to Cybercriminal Underground
Indeed, Shadow Hammer doesn’t at this point seem to be on the scale of NotPetya, which affected thousands of computers worldwide and is believed to be the most “devestating cyberattack in history,” causing upwards of $10 billion in damages. The NotPetya malware cost global shipping company Fedex alone upwards of half a billion dollars in damages.
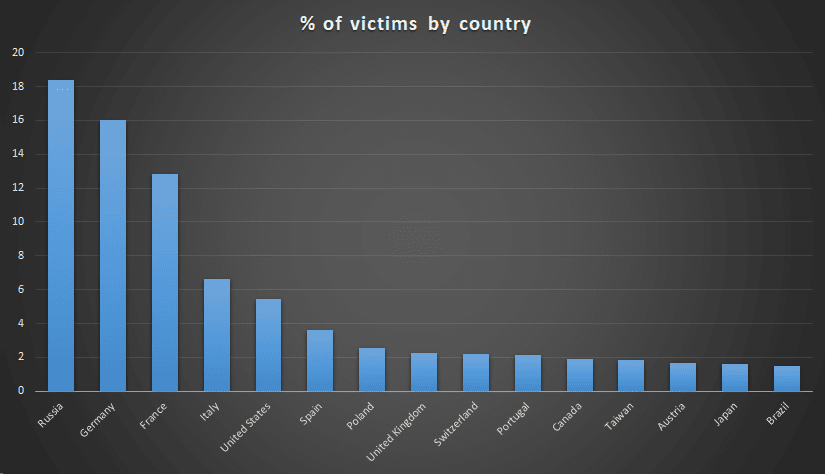
Calling ShadowHammer potentially “one of the biggest supply-chain incidents ever,” Kaspersky researchers estimated that the malware was distributed to about 1 million people total. However, the cybercriminals had specific targets–600 specific MAC addresses, for which the hashes were hardcoded into different versions of the utility. The company published an online tool for users to check if a system’s MAC address.
Still, Kaspersky researchers discovered that the same techniques used against ASUS also were used against software from three other vendors, which means it’s too soon to tell the extent of the systems affected. All four companies with affected software have been notified of the attack, which Kaspersky continues to investigate.
This isn’t the first such attack Kaspersky has detected. The Flame attack on Microsoft’s software update ecosystem in 2012 was a prominent, early example of how software update channels could be targeted. In 2017, the company warned that the update mechanism for Korean server management software provider NetSarang was compromised and serving a backdoor called ShadowPad.
Supply chain hacks are the new normal
Indeed, ShadowHammer is troubling news, suggesting that software supply chains will continue to be a security soft spot for organizations, said Allan Liska, senior solutions architect for security research firm Recorded Future.
“Any time you’re trusting an outside vendor you don’t have full visibility into risk is amplified,” he told Security Ledger.
Malware distributed through updates can be particularly tricky for companies in terms of supply-chain risk, since this type of activity is necessary to keep software and firmware up to date and often happens in one bulk action, Liska said.
“Often, this means thousands of updates from hundreds of vendors occurring all the time on the network,” he said. “It would take a large, specialized, team to verify each update prior to install.”
Instead, organizations tend to have confidence in updates and don’t question their legitimacy, “which is the right way to do it, but it is also a potential weakness in their security posture,” Liska said.
One small bright spot for those worried about supply chain attacks is that they are difficult and tricky to pull off, he said. “They generally require a lot of resources, planning and time,” he said.
Still, once an attack is successful, detection is difficult, and attackers have “a huge advantage because they’re starting from a privileged position inside the network–often in an area that is not closely monitored,” Liska said.
Code offers key to prevention
As affected companies scramble to gauge the impact of yet another potentially widespread and destructive malware, security experts are pondering the usual question of how to prevent these type of supply-chain attacks before they happen.
Recorded Future’s Liska suggests that hardware makers keep a closer eye on their code and code repositories for changes than they currently do. This might help them identify anomalies and allow them to take action to resolve issues more quickly.
“Often in these supply-chain attacks, attackers will compromise code that has been published to the vendor’s update server, replacing the legitimate code with trojanized code,” he said. “A continuous review of code repositories helps to ensure that the code that is supposed to be delivered to your customers is the correct code.”
Better code management also was the focus of advice offered by another expert, who suggested developers consider using an underrated component of secure coding practices–threat modeling.
“It’s a process that ensures security is built into software as it’s being developed by considering the ways the software could be compromised and cause harm,” said Mike Jordan, senior director of third-party risk-management organization The Shared Assessments Program. “A good threat modeling methodology in practice would identify the software update mechanism as a potential target for attack and consider ways to secure it.”


Pingback: Podcast Episode 141: Massive Data Breaches Just Keep Happening. We Talk about Why. | The Security Ledger