The NotPetya wiper malware took a bite out of candy maker Mondelez International’s 2017 earnings, the company has reported.
Mondelez, which was hit by the outbreak in June, said that it spent $84 million in “incremental costs” to investigate the incident, remove the malware and restore systems infected by the so-called “wiper” malware. In addition, the disruptions caused by NotPetya shaved %.4 off Mondelez’s 2017 net revenue of $25.9 billion, due mostly to disrupted shipments of candy and other treats following the malware outbreak in the second quarter, putting the full cost of the incident at closer to $180 million for Mondelez.
The revelation, which was included in Mondelez’s annual 10-K filing with the U.S. Securities and Exchange Commission (SEC) is just the latest evidence of the cost of the NotPetya outbreak, which began in the Ukraine, but affected a wide range of other firms including Federal Express, Merck Pharmaceuticals and the shipping firm Maersk.
“During 2017, we estimate that the loss of revenue as a result of the malware incident had a negative impact of 0.4% on our net revenue and Organic Net Revenue growth,” Mondelez said. “We also incurred incremental expenses of $84 million predominantly during the second half of 2017 as part of the recovery effort.” The company said that it believed the NotPetya incident was “largely resolved” and that it was continuing to “strengthen our security measures and mitigate cybersecurity risk.” “We do not expect significant ongoing impacts or incremental expenses from this incident in future periods,” Mondelez said in the SEC filing.
The impact of the outbreak was felt across Mondelez’s global business as expected shipments were not made because of disruptions to Mondelez’s operations. Only a portion of those were recovered, the company said.
Mondelez, based in Deerfield, Illinois, makes snacks, beverages and candies. It’s various snack brands include household names like Nabisco, Oreo, Cadbury and Toblerone chocolate and Trident gum.
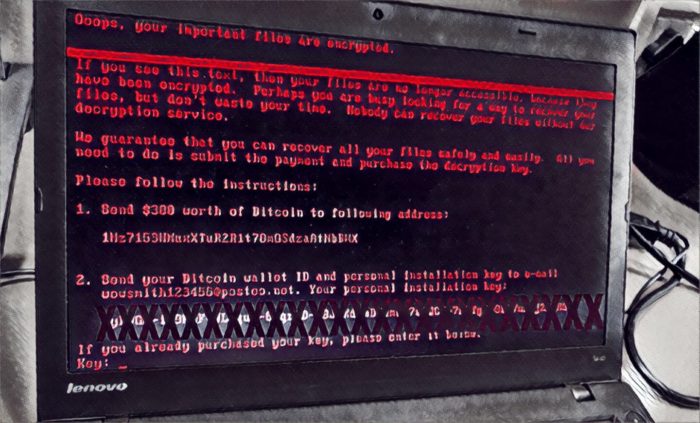
NotPetya began circulating on June 27, 2017 as signed software updates from M.E. Docs, a Ukrainian maker of accounting software. The software was a variant of ransomware known as “Petya” and appeared to be ransomware as well. However, the malware had been modified to wipe out, rather than simply encrypt hard drives that it infected, making the malware far more destructive for firms that were hit with it.
More than a million computers were infected, with the earliest victims almost all M.E. Docs customers, including the shipping giant Federal Express, which acquired M.E. Docs licenses through a recently acquired Dutch Subsidiary, TNT Express.
The Ukraine was particularly hard hit. More than 2,000 firms in that country were infected with NotPetya, according to a report by Ukrainian police. But significant outbreaks also spilled into The Russian Federation, Poland, Italy and Germany, in addition to other countries.
In addition to compromised software updates, NotPetya also spread as an Internet worm by harnessing the Eternal Blue and Eternal Romance exploits for Microsoft Windows – part of a trove of offensive hacking tools stolen from the NSA and leaked by a group known as ShadowBrokers.
The estimated $180 million price tag at Mondelez is small compared with Federal Express, which said the outbreak cost it more than $400 million in direct and indirect costs in 2017.






